The Perfect Server CentOS 7.6 with Apache, PHP 7.2, Postfix, Dovecot, Pure-FTPD, BIND and ISPConfig 3.1 - Page 2
This tutorial exists for these OS versions
On this page
- 7 Install Dovecot
- 8 Install Postfix
- 9 Install Getmail
- 10 Set MySQL Passwords and Configure phpMyAdmin
- 11 Install Amavisd-new, SpamAssassin, ClamAV, and Postgrey
- 12 Installing Apache with mod_php, mod_fcgi/PHP, PHP-FPM
- 13 Installation of mod_python
- 14 Install PureFTPd
- 15 Install BIND
- 16 Install Webalizer, and AWStats
- 17 Install Jailkit
- 18 Install Fail2Ban
- 19 Install rkhunter
- 20 Install Mailman
7 Install Dovecot
Dovecot can be installed as follows:
yum -y install dovecot dovecot-mysql dovecot-pigeonhole
Create an empty dovecot-sql.conf file and create symlinks:
touch /etc/dovecot/dovecot-sql.conf
ln -s /etc/dovecot/dovecot-sql.conf /etc/dovecot-sql.conf
ln -s /etc/dovecot/dovecot.conf /etc/dovecot.conf
Now create the system startup links and start Dovecot:
systemctl enable dovecot
systemctl start dovecot
8 Install Postfix
Postfix can be installed as follows:
yum -y install postfix
Then turn off Sendmail and start Postfix and MariaDB (MySQL):
systemctl enable mariadb.service
systemctl start mariadb.service
systemctl stop sendmail.service
systemctl disable sendmail.service
systemctl enable postfix.service
systemctl restart postfix.service
We disable sendmail to ensure that it does not get started in case it is installed on your server. So the error message "Failed to issue method call: Unit sendmail.service not loaded." can be ignored.
9 Install Getmail
Getmail can be installed as follows:
yum -y install getmail
10 Set MySQL Passwords and Configure phpMyAdmin
Set passwords for the MySQL root account:
mysql_secure_installation
[root@server1 tmp]# mysql_secure_installation
NOTE: RUNNING ALL PARTS OF THIS SCRIPT IS RECOMMENDED FOR ALL MariaDB
SERVERS IN PRODUCTION USE! PLEASE READ EACH STEP CAREFULLY!
In order to log into MariaDB to secure it, we'll need the current
password for the root user. If you've just installed MariaDB, and
you haven't set the root password yet, the password will be blank,
so you should just press enter here.
Enter current password for root (enter for none):
OK, successfully used password, moving on...
Setting the root password ensures that nobody can log into the MariaDB
root user without the proper authorisation.
Set root password? [Y/n] <-- ENTER
New password: <-- yourrootsqlpassword
Re-enter new password: <-- yourrootsqlpassword
Password updated successfully!
Reloading privilege tables..
... Success!
By default, a MariaDB installation has an anonymous user, allowing anyone
to log into MariaDB without having to have a user account created for
them. This is intended only for testing, and to make the installation
go a bit smoother. You should remove them before moving into a
production environment.
Remove anonymous users? [Y/n] <-- ENTER
... Success!
Normally, root should only be allowed to connect from 'localhost'. This
ensures that someone cannot guess at the root password from the network.
Disallow root login remotely? [Y/n] <-- ENTER
... Success!
By default, MariaDB comes with a database named 'test' that anyone can
access. This is also intended only for testing, and should be removed
before moving into a production environment.
Remove test database and access to it? [Y/n] <-- ENTER
- Dropping test database...
... Success!
- Removing privileges on test database...
... Success!
Reloading the privilege tables will ensure that all changes made so far
will take effect immediately.
Reload privilege tables now? [Y/n] <-- ENTER
... Success!
Cleaning up...
All done! If you've completed all of the above steps, your MariaDB
installation should now be secure.
Thanks for using MariaDB!
[root@server1 tmp]#
Now we configure phpMyAdmin. We change the Apache configuration so that phpMyAdmin allows connections not just from localhost (by commenting out the lines marked in red):
nano /etc/httpd/conf.d/phpMyAdmin.conf
# phpMyAdmin - Web based MySQL browser written in php
#
# Allows only localhost by default
#
# But allowing phpMyAdmin to anyone other than localhost should be considered
# dangerous unless properly secured by SSL
Alias /phpMyAdmin /usr/share/phpMyAdmin
Alias /phpmyadmin /usr/share/phpMyAdmin
<Directory /usr/share/phpMyAdmin/>
<IfModule mod_authz_core.c>
# Apache 2.4
# <RequireAny>
# Require ip 127.0.0.1
# Require ip ::1
# </RequireAny>
</IfModule>
<IfModule !mod_authz_core.c>
# Apache 2.2
Order Deny,Allow
Deny from All
Allow from 127.0.0.1
Allow from ::1
</IfModule>
</Directory>
Next, we change the authentication in phpMyAdmin from cookie to http:
nano /etc/phpMyAdmin/config.inc.php
[...] /* Authentication type */ $cfg['Servers'][$i]['auth_type'] = 'http'; [...]
Then we create the system startup links for Apache and start it:
systemctl enable httpd.service
systemctl restart httpd.service
Now you can direct your browser to http://server1.example.com/phpmyadmin/ or http://192.168.0.100/phpmyadmin/ and log in with the user name root and your new root MySQL password.
11 Install Amavisd-new, SpamAssassin, ClamAV, and Postgrey
To install amavisd-new, SpamAssassin and ClamAV, run the following command:
yum -y install amavisd-new spamassassin clamav-server clamav-data clamav-update clamav-filesystem clamav clamav-scanner-systemd clamav-devel clamav-lib clamav-server-systemd unzip bzip2 perl-DBD-mysql postgrey re2c
Then we start freshclam, amavisd, and clamd.amavisd:
sa-update
freshclam
systemctl enable amavisd.service
systemctl start amavisd.service
systemctl start [email protected]
systemctl enable postgrey.service
systemctl start postgrey.service
12 Installing Apache with mod_php, mod_fcgi/PHP, PHP-FPM
ISPConfig 3 allows you to use mod_php, mod_fcgi/PHP, cgi/PHP, and PHP-FPM on a per website basis.
We can install Apache2 with mod_php, mod_fcgid, and PHP as follows:
yum -y install php php-devel php-gd php-imap php-ldap php-mysql php-odbc php-pear php-xml php-xmlrpc php-pecl-apc php-mbstring php-mcrypt php-mssql php-snmp php-soap php-tidy curl curl-devel perl-libwww-perl ImageMagick libxml2 libxml2-devel mod_fcgid php-cli httpd-devel php-fpm php-intl php-imagick php-pspell wget
Next we open /etc/php.ini...
nano /etc/php.ini
... and change the error reporting (so that notices aren't shown any longer), set the timezone and uncomment cgi.fix_pathinfo=1:
[...] ;error_reporting = E_ALL & ~E_DEPRECATED error_reporting = E_ALL & ~E_NOTICE & ~E_DEPRECATED & ~E_STRICT [...] ; cgi.fix_pathinfo provides *real* PATH_INFO/PATH_TRANSLATED support for CGI. PHP's ; previous behaviour was to set PATH_TRANSLATED to SCRIPT_FILENAME, and to not grok ; what PATH_INFO is. For more information on PAppp.tldTH_INFO, see the cgi specs. Setting ; this to 1 will cause PHP CGI to fix its paths to conform to the spec. A setting ; of zero causes PHP to behave as before. Default is 1. You should fix your scripts ; to use SCRIPT_FILENAME rather than PATH_TRANSLATED. ; http://www.php.net/manual/en/ini.core.php#ini.cgi.fix-pathinfo cgi.fix_pathinfo=1
[...]
date.timezone = 'Europe/Berlin' [...]
Enable httpd and PHP-FPM to get started at boot time and start the PHP-FPM service.
systemctl start php-fpm.service
systemctl enable php-fpm.service
systemctl enable httpd.service
Finally, we restart Apache:
systemctl restart httpd.service
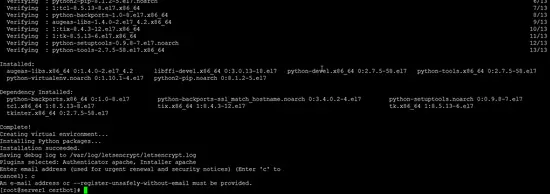
Now we will add support for Let's encrypt.
mkdir /opt/certbot
cd /opt/certbot
wget https://dl.eff.org/certbot-auto
chmod a+x ./certbot-auto
Now run the certbot-auto command which will download and install the software and it's dependencies.
./certbot-auto
The command will then tell you that "no names were found in your configuration files" and asks if it shall continue, please chose "c" to cancel here as the certs will be created by ispconfig.
13 Installation of mod_python
The Apache module mod_python is not available as RPM package, therefore we will compile it from source. The first step is to install the python development files and download the current mod_python version as .tar.gz file
yum -y install python-devel
cd /usr/local/src/
wget http://dist.modpython.org/dist/mod_python-3.5.0.tgz
tar xfz mod_python-3.5.0.tgz
cd mod_python-3.5.0
and then configure and compile the module.
./configure
make
There is an error in the compiled module that will cause the installation to fail with the error "version = "fatal: Not a git repository (or any of the parent directories): .git". To fix that, run this sed command (the command is one line!).
sed -e 's/(git describe --always)/(git describe --always 2>\/dev\/null)/g' -e 's/`git describe --always`/`git describe --always 2>\/dev\/null`/g' -i $( find . -type f -name Makefile\* -o -name version.sh )
Then install the module with this command.
make install
and enable the module in Apache:
echo 'LoadModule python_module modules/mod_python.so' > /etc/httpd/conf.modules.d/10-python.conf
systemctl restart httpd.service
14 Install PureFTPd
PureFTPd can be installed with the following command:
yum -y install pure-ftpd
Then create the system startup links and start PureFTPd:
systemctl enable pure-ftpd.service
systemctl start pure-ftpd.service
Now we configure PureFTPd to allow FTP and TLS sessions. FTP is a very insecure protocol because all passwords and all data are transferred in clear text. By using TLS, the whole communication can be encrypted, thus making FTP much more secure.
OpenSSL is needed by TLS; to install OpenSSL, we simply run:
yum install openssl
Open /etc/pure-ftpd/pure-ftpd.conf...
nano /etc/pure-ftpd/pure-ftpd.conf
If you want to allow FTP and TLS sessions, set TLS to 1 by removing the # in front of the TLS line. It is highly recommended to enable TLS.
[...] # This option can accept three values : # 0 : disable SSL/TLS encryption layer (default). # 1 : accept both traditional and encrypted sessions. # 2 : refuse connections that don't use SSL/TLS security mechanisms, # including anonymous sessions. # Do _not_ uncomment this blindly. Be sure that : # 1) Your server has been compiled with SSL/TLS support (--with-tls), # 2) A valid certificate is in place, # 3) Only compatible clients will log in. TLS 1 [...]
In order to use TLS, we must create an SSL certificate. I create it in /etc/ssl/private/, therefore I create that directory first:
mkdir -p /etc/ssl/private/
Afterwards, we can generate the SSL certificate as follows:
openssl req -x509 -nodes -days 7300 -newkey rsa:2048 -keyout /etc/ssl/private/pure-ftpd.pem -out /etc/ssl/private/pure-ftpd.pem
Country Name (2 letter code) [XX]: <-- Enter your Country Name (e.g., "DE").
State or Province Name (full name) []:<-- Enter your State or Province Name.
Locality Name (eg, city) [Default City]:<-- Enter your City.
Organization Name (eg, company) [Default Company Ltd]:<-- Enter your Organization Name (e.g., the name of your company).
Organizational Unit Name (eg, section) []:<-- Enter your Organizational Unit Name (e.g. "IT Department").
Common Name (eg, your name or your server's hostname) []:<-- Enter the Fully Qualified Domain Name of the system (e.g. "server1.example.com").
Email Address []:<-- Enter your Email Address.
Change the permissions of the SSL certificate:
chmod 600 /etc/ssl/private/pure-ftpd.pem
Create a DHParam file:
openssl dhparam -out /etc/ssl/private/pure-ftpd-dhparams.pem 2048
Finally, restart PureFTPd:
systemctl restart pure-ftpd.service
That's it. You can now try to connect using your FTP client; however, you should configure your FTP client to use TLS.
15 Install BIND
We can install BIND as follows:
yum -y install bind bind-utils haveged
Make a backup of the existing /etc/named.conf file and create a new one as follows:
cp /etc/named.conf /etc/named.conf_bak
cat /dev/null > /etc/named.conf
nano /etc/named.conf
//
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
options {
listen-on port 53 { any; };
listen-on-v6 port 53 { any; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
allow-query { any; };
allow-recursion {"none";};
recursion no;
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.conf.local";
Create the file /etc/named.conf.local that is included at the end of /etc/named.conf (/etc/named.conf.local will later on get populated by ISPConfig if you create DNS zones in ISPConfig):
touch /etc/named.conf.local
Then we create the startup links and start BIND:
systemctl enable named.service
systemctl start named.service
systemctl enable haveged.service
systemctl start haveged.service
16 Install Webalizer, and AWStats
AWStats can be installed as follows:
yum -y install webalizer awstats perl-DateTime-Format-HTTP perl-DateTime-Format-Builder
Edit the file /etc/httpd/conf.d/awstats.conf:
nano /etc/httpd/conf.d/awstats.conf
and change the line:
Require local
to:
Require all granted
And restart apache:
systemctl restart httpd.service
17 Install Jailkit
Jailkit is used to chroot SSH users and cronjobs. It can be installed as follows:
cd /tmp
wget http://olivier.sessink.nl/jailkit/jailkit-2.20.tar.gz
tar xvfz jailkit-2.20.tar.gz
cd jailkit-2.20
./configure
make
make install
cd ..
rm -rf jailkit-2.20*
18 Install Fail2Ban
This is optional but recommended, because the ISPConfig monitor tries to show the log.
yum -y install iptables-services fail2ban fail2ban-systemd
systemctl stop firewalld.service
systemctl mask firewalld.service
systemctl disable firewalld.service
systemctl stop firewalld.service
Next we create the /etc/fail2ban/jail.local file and enable monitoring for ssh, email and ftp service.
nano /etc/fail2ban/jail.local
Add the following content to the jail.local file:
[sshd]
enabled = true
action = iptables[name=sshd, port=ssh, protocol=tcp]
[pure-ftpd]
enabled = true
action = iptables[name=FTP, port=ftp, protocol=tcp]
maxretry = 3
[dovecot]
enabled = true
action = iptables-multiport[name=dovecot, port="pop3,pop3s,imap,imaps", protocol=tcp]
maxretry = 5
[postfix-sasl]
enabled = true
action = iptables-multiport[name=postfix-sasl, port="smtp,smtps,submission", protocol=tcp]
maxretry = 3
Then create the system startup links for fail2ban and start it:
systemctl enable fail2ban.service
systemctl start fail2ban.service
19 Install rkhunter
rkhunter can be installed as follows:
yum -y install rkhunter
20 Install Mailman
If you like to manage mailing lists with Mailman on your server, then install mailman now. Mailman is supported by ISPConfig, so you will be able to create new mailing lists trough ISPConfig later.
yum -y install mailman
Before we can start Mailman, a first mailing list called mailman must be created:
touch /var/lib/mailman/data/aliases
postmap /var/lib/mailman/data/aliases
/usr/lib/mailman/bin/newlist mailman
ln -s /usr/lib/mailman/mail/mailman /usr/bin/mailman
[root@server1 tmp]# /usr/lib/mailman/bin/newlist mailman
Enter the email of the person running the list: <-- admin email address, e.g. [email protected]
Initial mailman password: <-- admin password for the mailman list
To finish creating your mailing list, you must edit your /etc/aliases (or
equivalent) file by adding the following lines, and possibly running the
`newaliases' program:
## mailman mailing list
mailman: "|/usr/lib/mailman/mail/mailman post mailman"
mailman-admin: "|/usr/lib/mailman/mail/mailman admin mailman"
mailman-bounces: "|/usr/lib/mailman/mail/mailman bounces mailman"
mailman-confirm: "|/usr/lib/mailman/mail/mailman confirm mailman"
mailman-join: "|/usr/lib/mailman/mail/mailman join mailman"
mailman-leave: "|/usr/lib/mailman/mail/mailman leave mailman"
mailman-owner: "|/usr/lib/mailman/mail/mailman owner mailman"
mailman-request: "|/usr/lib/mailman/mail/mailman request mailman"
mailman-subscribe: "|/usr/lib/mailman/mail/mailman subscribe mailman"
mailman-unsubscribe: "|/usr/lib/mailman/mail/mailman unsubscribe mailman"
Hit enter to notify mailman owner... <-- ENTER
[root@server1 tmp]#
Open /etc/aliases afterwards...
nano /etc/aliases
... and add the following lines:
[...] mailman: "|/usr/lib/mailman/mail/mailman post mailman" mailman-admin: "|/usr/lib/mailman/mail/mailman admin mailman" mailman-bounces: "|/usr/lib/mailman/mail/mailman bounces mailman" mailman-confirm: "|/usr/lib/mailman/mail/mailman confirm mailman" mailman-join: "|/usr/lib/mailman/mail/mailman join mailman" mailman-leave: "|/usr/lib/mailman/mail/mailman leave mailman" mailman-owner: "|/usr/lib/mailman/mail/mailman owner mailman" mailman-request: "|/usr/lib/mailman/mail/mailman request mailman" mailman-subscribe: "|/usr/lib/mailman/mail/mailman subscribe mailman" mailman-unsubscribe: "|/usr/lib/mailman/mail/mailman unsubscribe mailman"
Run
newaliases
afterwards and restart Postfix:
systemctl restart postfix.service
Now open the Mailman Apache configuration file /etc/httpd/conf.d/mailman.conf...
nano /etc/httpd/conf.d/mailman.conf
... and add the line ScriptAlias /cgi-bin/mailman/ /usr/lib/mailman/cgi-bin/. Comment out Alias /pipermail/ /var/lib/mailman/archives/public/ and add the line Alias /pipermail /var/lib/mailman/archives/public/:
#
# httpd configuration settings for use with mailman.
#
ScriptAlias /mailman/ /usr/lib/mailman/cgi-bin/
ScriptAlias /cgi-bin/mailman/ /usr/lib/mailman/cgi-bin/
<Directory /usr/lib/mailman/cgi-bin/>
AllowOverride None
Options ExecCGI
Order allow,deny
Allow from all
</Directory>
#Alias /pipermail/ /var/lib/mailman/archives/public/
Alias /pipermail /var/lib/mailman/archives/public/
<Directory /var/lib/mailman/archives/public>
Options Indexes MultiViews FollowSymLinks
AllowOverride None
Order allow,deny
Allow from all
AddDefaultCharset Off
</Directory>
# Uncomment the following line, to redirect queries to /mailman to the
# listinfo page (recommended).
# RedirectMatch ^/mailman[/]*$ /mailman/listinfo
Restart Apache:
systemctl restart httpd.service
Create the system startup links for Mailman and start it:
systemctl enable mailman.service
systemctl start mailman.service
After you have installed ISPConfig 3, you can access Mailman as follows:
You can use the alias /cgi-bin/mailman for all Apache vhosts (please note that suExec and CGI must be disabled for all vhosts from which you want to access Mailman!), which means you can access the Mailman admin interface for a list at http://<vhost>/cgi-bin/mailman/admin/<listname>, and the web page for users of a mailing list can be found at http://<vhost>/cgi-bin/mailman/listinfo/<listname>.
Under http://<vhost>/pipermail/<listname> you can find the mailing list archives.