Linux Tutorials on the topic “linux”
-
How to Install and Configure VNC Server on CentOS 8
Author: Hitesh Jethva • Tags: centos, linux, server • Comments: 3VNC stands for "Virtual Network Computing" is a GUI desktop sharing application that can be used to access and control other computers over a network. In this tutorial, we will show you how to install VNC server on CentOS 8.
-
How to Install Terraform on Ubuntu 18.04 LTS
Author: Blago Eres • Tags: cloud, linux, ubuntu • Comments: 2Terraform is an open-source infrastructure automation tool which allows you to define and describe your infrastructure as code inside configuration files using a declarative language and to deploy and manage that infrastructure across a variety of public cloud providers like AWS, GCP and Azure.
-
How to Install Apache ActiveMQ and Hawt.io on CentOS 8
Author: Hitesh Jethva • Tags: centos, linux, programming • Comments: 0Apache ActiveMQ is a free, open-source and Java-based message broker that can be used to send messages between two applications. In this tutorial, we will learn how to install Apache ActiveMQ on CentOS 8.
-
-
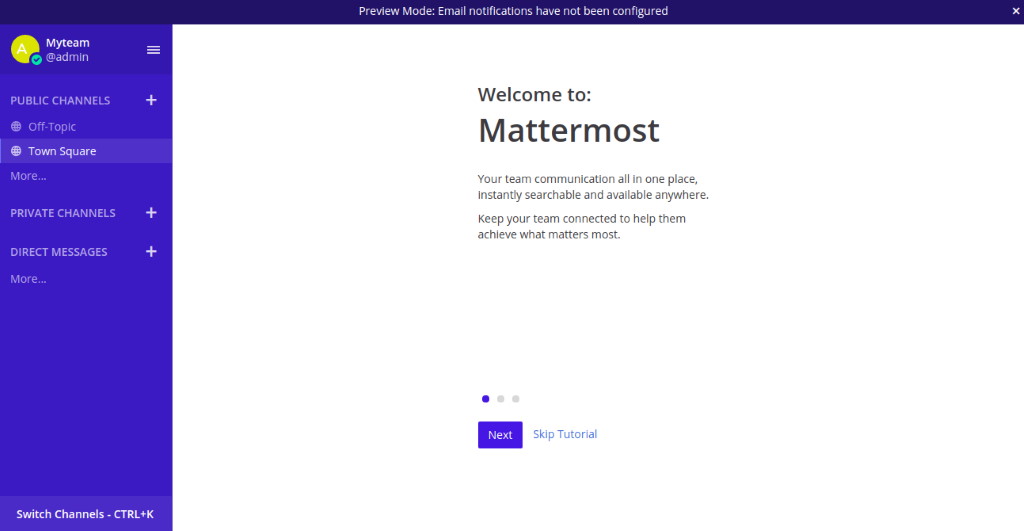
How to Install and Configure Mattermost on CentOS 8
Author: Hitesh Jethva • Tags: centos, linux, nginx, web server • Comments: 2Mattermost is a free, open-source and self-hosted enterprise team collaboration messaging system. In this tutorial, we will show you how to install Mattermost with Nginx reverse Proxy on CentOS 8.
-
How to Install Visual Studio Code Server on Debian 10
Author: Muhammad Arul • Tags: debian, linux, programming • Comments: 0In this tutorial we show you how to install the code server on the Debian Buster 10. We will install and configure the code server using Nginx as a reverse proxy, secure it with SSL Letsencrypt and enable code server basic authentication.
-
How to Install OpenProject on Debian 10
 Author: Hitesh Jethva •
Tags: debian, linux •
Comments: 0
Author: Hitesh Jethva •
Tags: debian, linux •
Comments: 0 OpenProject is a web-based project management system written in Ruby on Rails and AngularJS. It provides a rich set of features including, project planning, timelines reports, task management, WYSIWYG text editor, intelligent workflows, conditional formatting and much more.
-
What is umask in Linux?
Author: Nitesh Bhavsar • Tags: linux, shell • Comments: 3UMASK in Linux or Unix systems is known as User Mask or it is also called as User file creation Mask. This is a base permission or default permission when a new file or folder is created in the Linux machine.
-
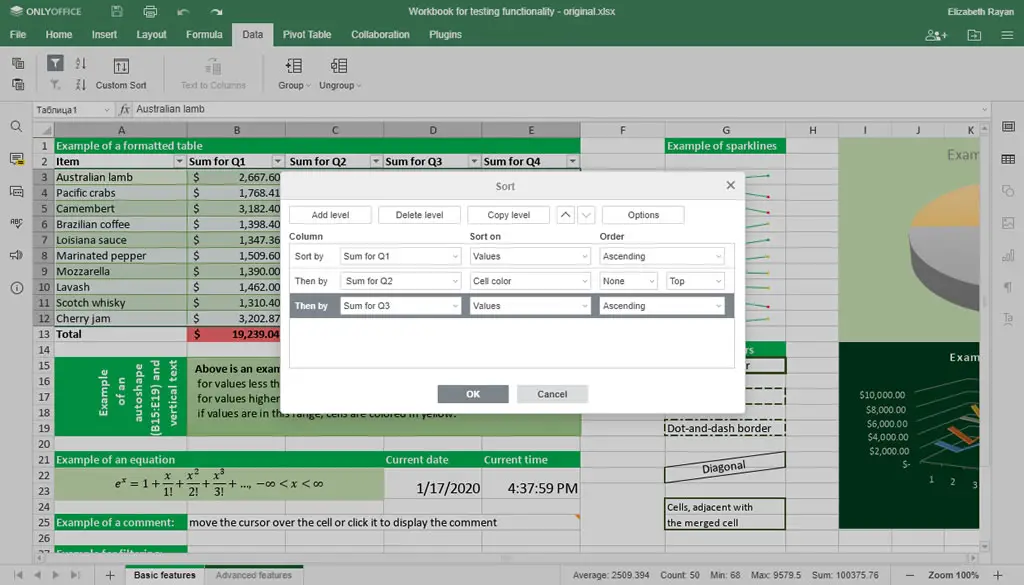
How to update ONLYOFFICE Document Server to version 5.5
Author: Daria • Tags: linux • Comments: 0In this tutorial, we'll learn how to update ONLYOFFICE Document Server to version 5.5 separately from other components. ONLYOFFICE is a free open-source solution with online editors and collaboration platform that includes doc management, projects, CRM, mail, chat, calendar and more.
-
Converting your Python 2 code to Python 3
Author: grothe • Tags: linux, programming • Comments: 0Python 2 reached the end of life on January 1, 2020. Python 3 has been available since 2008, but converting from 2 to 3 has been slow because of dependencies on libraries that were not available in Python 3 initially. This tutorial will show you how to convert Python 2 code to Python 3 using the 2to3 tool.
-
How to Install an Email Server with ISPConfig on Debian 10
Author: Tapio Lehtonen • Tags: debian, email, ispconfig, linux • Comments: 4This tutorial shows how to install a mail server on Debian 10 using ISPConfig server control panel.