Ubuntu 18.04 (LTS) LAMP server tutorial with Apache, PHP 7.2, and MySQL
This tutorial exists for these OS versions
- Ubuntu 24.04 (Noble Numbat)
- Ubuntu 22.04 (Jammy Jellyfish)
- Ubuntu 18.04 (Bionic Beaver)
- Ubuntu 16.04 (Xenial Xerus)
- Ubuntu 15.10 (Wily Werewolf)
- Ubuntu 15.04 (Vivid Vervet)
On this page
- Preliminary Note
- 1. Installing MySQL or MariaDB Database
- 2. Install Apache Web Server
- 3. Install PHP 7.2
- 4. Test PHP and get details about your PHP installation
- 5. Get MySQL / MariaDB support in PHP
- 6. Install the Opcache + APCu PHP cache to speed up PHP
- 7. Enable the SSL website in apache
- 8. Get a free SSL Certificate from Let's Encrypt
- 9. Install phpMyAdmin
- 10 Virtual machine image download of this tutorial
- 11 Links
LAMP is short for Linux, Apache, MySQL, PHP. This tutorial shows how you can install an Apache web server on an Ubuntu 18.04 LTS (Bionic Beaver) server with PHP 7.2 (mod_php) and MySQL / MariaDB support and how to setup an SSL certificate with Let's encrypt. Additionally, I will install PHPMyAdmin to make MySQL administration easier. A LAMP setup is a perfect basis for popular CMS systems like Joomla, Wordpress or Drupal.
Preliminary Note
In this tutorial, I will use the hostname server1.example.com with the IP address 192.168.1.100. These settings might differ for you, so you have to replace them where appropriate.
I recommend to use a minimal Ubuntu server setup as basis for the tutorial, that can be a virtual- or root server image with an Ubuntu 18.04 minimal install from a web hosting company or you use our minimal server tutorial to install a server from scratch.
I'm running all the steps in this tutorial with root privileges, so make sure you're logged in as root:
sudo -s
1. Installing MySQL or MariaDB Database
There are currently two widely used MySQL database systems available, the classic "MySQL" server which is developed by Oracle and is available in version 5.7 now and the MySQL fork named MariaDB which is developed by the original MySQL developer Monty Widenius.
I will show you how to install both alternatives below. Just follow either chapter 1.1 or 1.2 but not both. I will use MySQL 5.7 for the virtual machine image that can be downloaded from Howtoforge.
1.1 Install MySQL 5.7
To install MySQL 5.7, execute this command:
apt-get -y install mysql-server mysql-client
The packages mysql-server and mysql-client are so-called 'meta-packages', they install always the latest MySQL version that is available from Ubuntu. The latest version is currently MySQL 5.7.
We have set the root password for MySQL already during installation, but I would like to remove the anonymous user and test database for security reasons. Run the mysql_secure_installation command below to achieve that.
mysql_secure_installation
You will be asked these questions:
Securing the MySQL server deployment.
Enter password for user root: <-- Enter the MySQL root password
VALIDATE PASSWORD PLUGIN can be used to test passwords
and improve security. It checks the strength of password
and allows the users to set only those passwords which are
secure enough. Would you like to setup VALIDATE PASSWORD plugin?
Press y|Y for Yes, any other key for No:
Using existing password for root.
Change the password for root ? ((Press y|Y for Yes, any other key for No) : <-- Choose 'y' here if you like to enable the password validation, I don't need that function, so I choose 'n' here.
... skipping.
By default, a MySQL installation has an anonymous user,
allowing anyone to log into MySQL without having to have
a user account created for them. This is intended only for
testing, and to make the installation go a bit smoother.
You should remove them before moving into a production
environment.
Remove anonymous users? (Press y|Y for Yes, any other key for No) : <-- y
Success.
Normally, root should only be allowed to connect from
'localhost'. This ensures that someone cannot guess at
the root password from the network.
Disallow root login remotely? (Press y|Y for Yes, any other key for No) : <-- y
Success.
By default, MySQL comes with a database named 'test' that
anyone can access. This is also intended only for testing,
and should be removed before moving into a production
environment.
Remove test database and access to it? (Press y|Y for Yes, any other key for No) : <-- y
- Dropping test database...
Success.
- Removing privileges on test database...
Success.
Reloading the privilege tables will ensure that all changes
made so far will take effect immediately.
Reload privilege tables now? (Press y|Y for Yes, any other key for No) : <-- y
Success.
All done!
The MySQL setup has been secured now.
1.2 Install MariaDB 10
Run the following command to install MariaDB-server and client:
apt-get -y install mariadb-server mariadb-client
Now we set a root password for MariaDB.
mysql_secure_installation
You will be asked these questions:
Enter current password for root (enter for none): <-- press enter
Set root password? [Y/n] <-- y
New password: <-- Enter the new MariaDB root password here
Re-enter new password: <-- Repeat the password
Remove anonymous users? [Y/n] <-- y
Disallow root login remotely? [Y/n] <-- y
Reload privilege tables now? [Y/n] <-- y
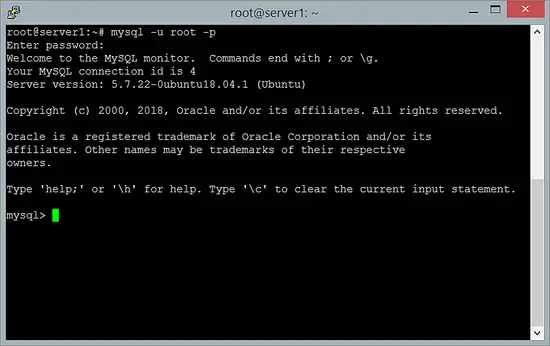
1.3 Test the MySQL/MariaDB root login
Test the login to MariaDB with the "mysql command"
mysql -u root -p
and enter the MariaDB root password that you've set above. The result should be similar to the screenshot below:
To leave the MySQL/MariaDB shell, enter the command "quit" and press enter.
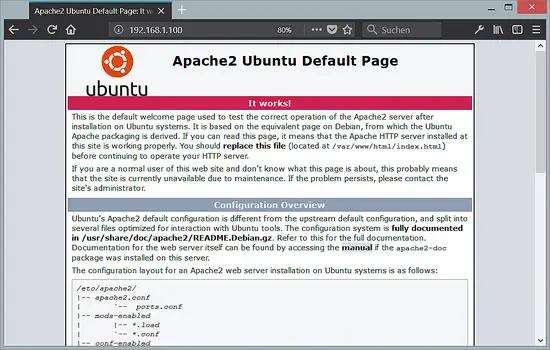
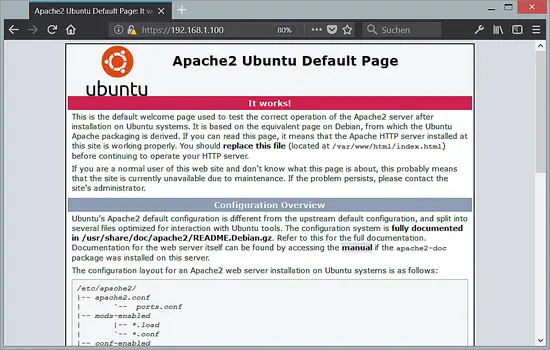
2. Install Apache Web Server
Apache 2 is available as an Ubuntu package, therefore we can install it like this:
apt-get -y install apache2
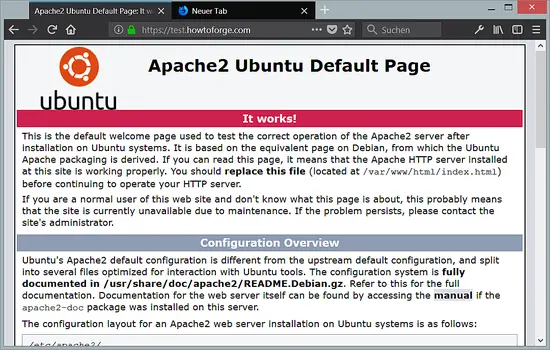
Now direct your browser to http://192.168.1.100, and you should see the Apache2 default page (It works!):
The document root of the apache default vhost is /var/www/html on Ubuntu and the main configuration file is /etc/apache2/apache2.conf. The configuration system is fully documented in /usr/share/doc/apache2/README.Debian.gz.
3. Install PHP 7.2
We can install PHP 7.2 and the Apache PHP module as follows:
apt-get -y install php7.2 libapache2-mod-php7.2
Then restart Apache:
systemctl restart apache2
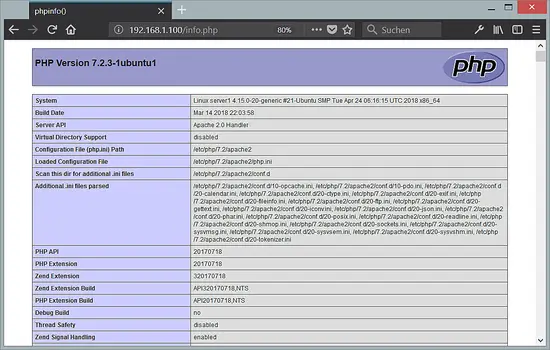
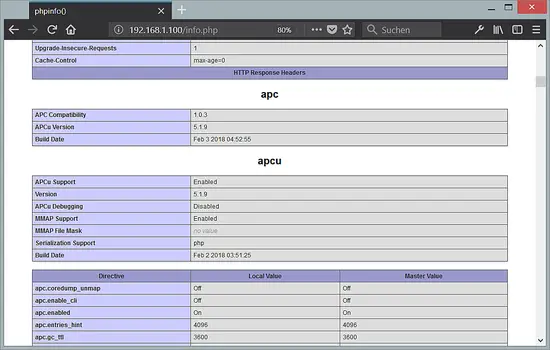
4. Test PHP and get details about your PHP installation
The document root of the default web site is /var/www/html. We will now create a small PHP file (info.php) in that directory and call it in a browser. The file will display lots of useful details about our PHP installation, such as the installed PHP version.
nano /var/www/html/info.php
<?php
phpinfo();
Then change the owner of the info.php file to the www-data user and group.
chown www-data:www-data /var/www/html/info.php
Now we call that file in a browser (e.g. http://192.168.1.100/info.php):
As you see, PHP 7.2 is working, and it's working through the Apache 2.0 Handler, as shown in the Server API line. If you scroll further down, you will see all modules that are already enabled in PHP. MySQL is not listed there which means we don't have MySQL / MariaDB support in PHP yet.
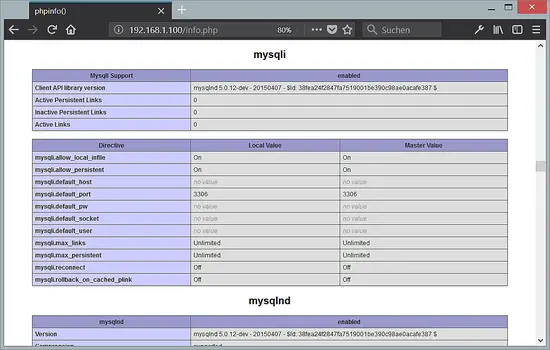
5. Get MySQL / MariaDB support in PHP
To get MySQL support in PHP, we can install the php7.2-mysql package. It's a good idea to install some other PHP modules as well as you might need them for your applications. You can search for available PHP modules like this:
apt-cache search php7.2
and
apt-cache search php-
as not all PHP packages have the version number 7.2 in their name.
Pick the ones you need and install them like this:
apt-get -y install php7.2-mysql php7.2-curl php7.2-gd php7.2-intl php-pear php-imagick php7.2-imap php-memcache php7.2-pspell php7.2-recode php7.2-sqlite3 php7.2-tidy php7.2-xmlrpc php7.2-xsl php7.2-mbstring php-gettext
Now restart Apache2:
systemctl restart apache2
PHP 7.2 has now MySQL / MariaDB support as shown in phpinfo() above.
6. Install the Opcache + APCu PHP cache to speed up PHP
PHP 7 ships with a built-in opcode cacher for caching and optimizing PHP intermediate code, it has the name 'opcache' and is available in the package php7.0-opcache. It is strongly recommended to have an Opcache installed to speed up your PHP page. Besides opcache, I will install APCu which is a compatibility wrapper for opcache to provide the functions of the APC cache, an often used caching system in PHP 5.x versions and many CMS systems still use it.
Opcache and APCu can be installed as follows:
apt-get -y install php7.2-opcache php-apcu
Don't worry if it shows that Opcache is already installed.
Now restart Apache:
systemctl restart apache2
Now reload http://192.168.1.100/info.php in your browser and scroll down to the modules section again. You should now find lots of new modules there:
Please don't forget to delete the info.php file when you don't need it anymore as it provides sensitive details of your server. Run the following command to delete the file.
rm -f /var/www/html/info.php
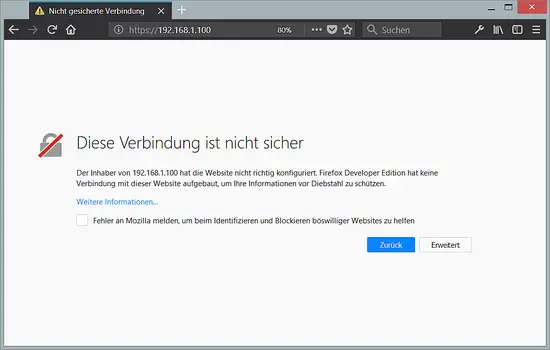
7. Enable the SSL website in apache
SSL/ TLS is a security layer to encrypt the connection between the web browser and your server. Most web browsers start to show sites as insecure today when the connection between the server and the web browser is not encrypted with SSL. In this chapter, I will show you how to secure your website with SSL.
Execute the following commands on your server to enable SSL (https://) support. Run:
a2enmod ssl
a2ensite default-ssl
which enables the SSL module and adds a symlink in the /etc/apache2/sites-enabled folder to the file /etc/apache2/sites-available/default-ssl.conf to include it into the active apache configuration. Then restart apache to enable the new configuration:
systemctl restart apache2
Now test the SSL connection by opening https://192.168.1.100 in a web browser.
You will receive an SSL warning as the SSL certificate of the server is a "self-signed" SSL certificate, this means that the browser does not trust this certificate by default and you have to accept the security warning first. After accepting the warning, you will see the apache default page.
The closed "Green Padlock" in front of the URL in the browser shows that the connection is encrypted.
There are two ways to get rid of the SSL warning, either replace the self-signed SSL certificate /etc/ssl/certs/ssl-cert-snakeoil.pem with an officially signed SSL certificate that you buy from an SSL Authority or you get a free SSL certificate from Let's encrypt, which I will describe in chapter 8.
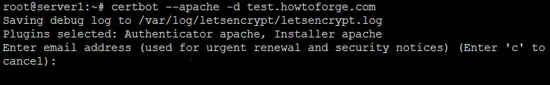
8. Get a free SSL Certificate from Let's Encrypt
The first step to secure the website with a Let's Encrypt SSL Certificate is to install the python3-certbot-apache package. Run the following command:
apt-get -y install python3-certbot-apache
In the next step, we will request an SSL cert from Let's Encrypt by using the certbot client program, during this process, the Let's Encrypt server tries to connect to your server through the domain name that you provide to the certbot command. It is important that this domain name points to your server in DNS already so that the website is reachable by its domain name on port 80 (http) already. If the website is not reachable from the internet, then the creation of the Let's Encrypt SSL certificate will fail.
Before we can start to create the SSL cert, set the domain name in the vhost configuration file. Open the default vhost file with an editor:
nano /etc/apache2/sites-available/000-default.conf
and add the line:
ServerName example.com
Right below the 'DocumentRoot' line. Replace example.com with the domain name of your own website.
Then create the SSL Certificate with this command:
certbot --apache -d example.com
Replace example.com with your domain name here again. The command will start a wizard that asks you several questions.
Enter the email address where the administrator who is responsible for this website can be reached.
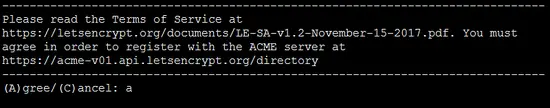
Accept the terms and conditions of the Let's Encrypt SSL authority.
Certbot will ask you now if you like to share your email address with the Electronic Frontier Foundation. Choose here whatever you prefer.
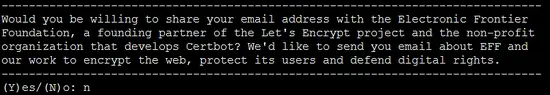
Then choose if you want to redirect non-SSL requests to https:// automatically. I'll select yes here to avoid duplicate content problems when the website is available as http:// and https:// version.
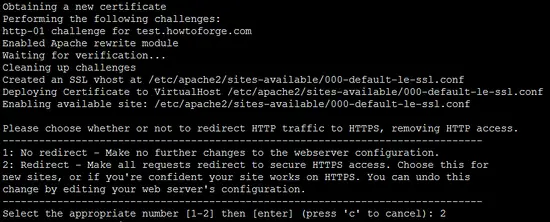
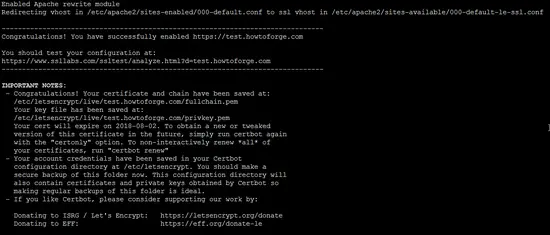
The SSL certificate has been issued successfully.
When you access the website now with a browser, you will get redirected automatically to SSL and the green padlock in front of the URL bar in the browser shows that we are using a trusted SSL certificate now.
8.1 Let's encrypt Auto Renewal
Let's Encrypt SSL certificates are valid for a short period of 80 days only. Therefore a cronjob to auto-renew the SSL certificates is necessary that runs the certbot --renew command.
This cronjob get setup automatically when you install certbot, the cron file is /etc/cron.d/certbot. So there is nothing more to do here. If you like to know what the cronjob looks like, run the command:
/etc/cron.d/certbot
The result is:
root@server1:~# cat /etc/cron.d/certbot
# /etc/cron.d/certbot: crontab entries for the certbot package
#
# Upstream recommends attempting renewal twice a day
#
# Eventually, this will be an opportunity to validate certificates
# haven't been revoked, etc. Renewal will only occur if expiration
# is within 30 days.
SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
0 */12 * * * root test -x /usr/bin/certbot -a \! -d /run/systemd/system && perl -e 'sleep int(rand(43200))' && certbot -q renew
9. Install phpMyAdmin
phpMyAdmin is a web interface through which you can manage your MySQL databases. It's a good idea to install it:
apt-get -y install phpmyadmin
IMPORTANT: The apt installer will ask you several questions now, one of them is to select the web server type. A common mistake is that the web server type is just highlighted but not selected. To select an item in an apt menu you have to press the space bar on the keyboard after you navigated to the item with tab or cursor keys. Just highlighting it is not enough!
You will see the following questions:
Web server to configure automatically: <-- Select the option: apache2
Configure database for phpmyadmin with dbconfig-common? <-- Yes
MySQL application password for phpmyadmin: <-- Press enter, apt will create a random password automatically.
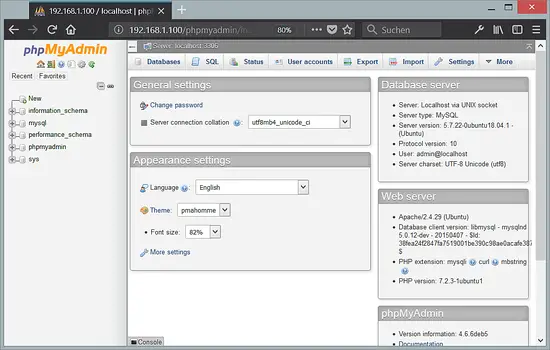
9.1 Root access to PHPMyAdmin
MariaDB and MySQL enable a plugin called "unix_socket" for the root user by default, this plugin prevents that the root user can log into PHPMyAdmin and that TCP connections to MySQL are working for the root user. To get a user with privileges to create other users and databases in PHPMyAdmin, I will create a new MySQL user with the name "admin" with the same privileges than the root user.
Login to the MySQL database as root user on the shell:
mysql -u root
Create a new user with the name "admin" and password "howtoforge". Replace the password "howtoforge" with a secure password in the commands below!
CREATE USER 'admin'@'localhost' IDENTIFIED BY 'howtoforge';
GRANT ALL PRIVILEGES ON *.* TO 'admin'@'localhost' WITH GRANT OPTION;
FLUSH PRIVILEGES;
exit
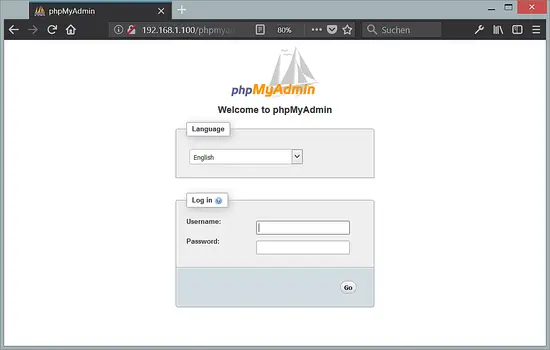
Afterward, you can access phpMyAdmin under http://192.168.1.100/phpmyadmin/:
10 Virtual machine image download of this tutorial
This tutorial is available as ready to use virtual machine image in ovf/ova format that is compatible with VMWare and Virtualbox. The virtual machine image uses the following login details:
SSH / Shell Login
Username: administrator
Password: howtoforge
This user has sudo rights.
MySQL Login
Username: root
Password: howtoforge
The IP of the VM is 192.168.1.100, it can be changed in the file /etc/network/interfaces. Please change all the above passwords to secure the virtual machine.
11 Links
- Apache: http://httpd.apache.org/
- PHP: http://www.php.net/
- MySQL: http://www.mysql.com/
- MariaDB: https://mariadb.com/
- Ubuntu: http://www.ubuntu.com/
- phpMyAdmin: http://www.phpmyadmin.net/