How to track your Linux laptop
On this page
So, you just bought a new shiny laptop and you are uncomfortable about the possibility to see it stolen and lost forever? There are many things you can do to help you recover your laptop after such an unfortunate thing happens, and almost all of them involve some kind of tracking software. Here is a quick guide on how to set up easy to use tools that will help you locate your stolen laptop.
Prey
Prey is a multi-platform tracking software that allows the tracking of up to three devices for free. It uses geolocation methodologies to track your device based on the IP of the connection that your set up device is using to access the internet, or the GPS sensor if your laptop has one. The software is distributed under the GPL license, so it's open source.
First, visit the download webpage and download the latest Prey package. You may also find it on your distribution's default repositories as well. After the installation is done, you will be prompt to create a new account.
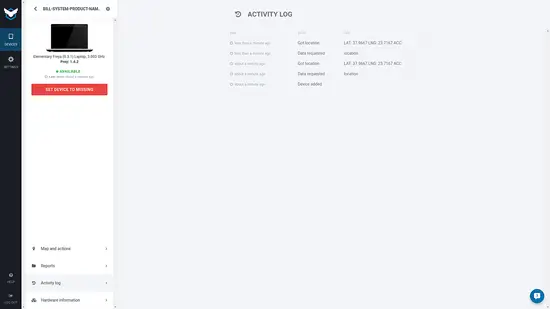
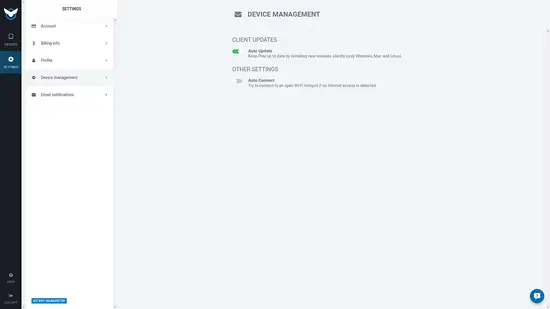
After this is done, Prey will add the device on its online database and connect it with your account. You may then simply visit the Prey website and login to start tracking your device.
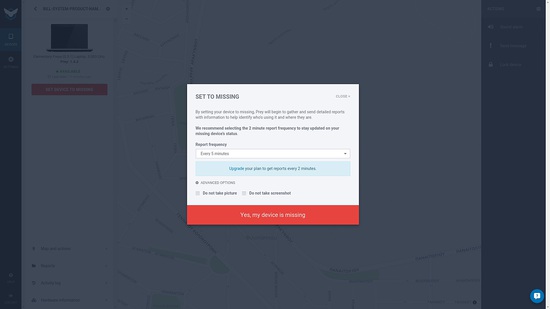
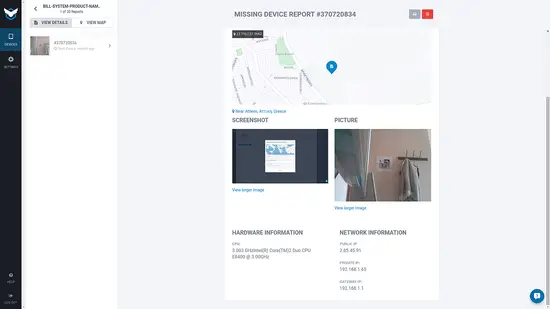
Once I set my device as “missing” Prey will begin sending me reports. Those reports contain the device's location (best guess), a screenshot of the desktop, and a photograph from the webcam.
Note that the webcam didn't light up when it took the above picture, so the person who stole your device doesn't have a clue that it is being tracked. Prey generally tries to stay in the background as much as possible, and it is very light on power consumption.
Dropbox
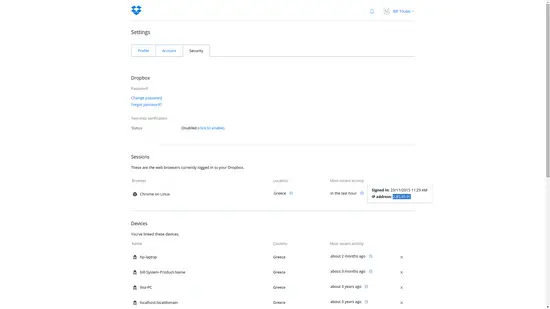
Dropbox is not a tracking software but a cloud data service. However, there are many Linux users who have Dropbox integration installed in their systems so every time your laptop connects to the internet Dropbox syncs the latest data changes with the defined local folder. This basically tells the online service approximately where your device is through IP tracking. Go to the Dropbox website and login to your account. Then go to “Settings” and choose the “Security” tab and there you will get the IP of the last session.
Location Magic
Another way to track down your stolen/lost Linux laptop is Location Magic (https://locationmagic.org). After creating a new account on this service, you receive an email with a unique token needed to access the webpage that contains the geolocation information. For this to work, you will need to install the Location Magic script in your system. To do this, enter the following command on a terminal:
wget https://locationmagic.org/install_scripts/locationmagic.sh && sudo bash ./locationmagic.sh -install linux 70f0fc3f6c2fbb23a75a
This will basically add a cron job in your system that will run the script one every hour. You may also check the (open source) code of the script on Git (https://github.com/unwiredlabs/location-magic/blob/master/README.md#installation-instructions-for-unix-devices) and install it manually on your crontab. After this is done, you may follow the link on the email that you got from the service, insert your token and track your device.