Virtualization With KVM On A Fedora 17 Server - Page 3
6 Creating A Debian Squeeze Guest (Image-Based) From The Desktop With virt-manager
Instead of creating a virtual machine from the command line (as shown in chapter 4), you can as well create it from the Fedora desktop using virt-manager (of course, the virtual machine will be created on the Fedora 17 KVM host - in case you ask yourself if virt-manager is able to create virtual machines on remote systems).
To do this, click on the following button:
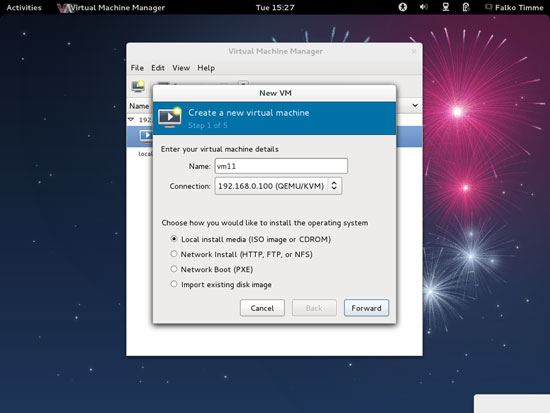
The New VM dialogue comes up. Fill in a name for the VM (e.g. vm11), select Local install media (ISO image or CDROM), and click on Forward:
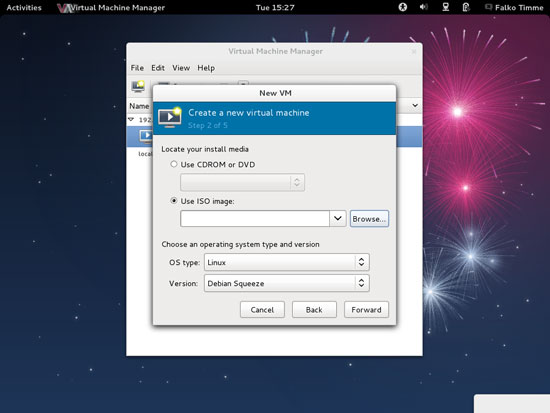
Next select Linux in the OS type drop-down menu and Debian Squeeze in the Version drop-down menu, then check Use ISO image and click on the Browse... button:
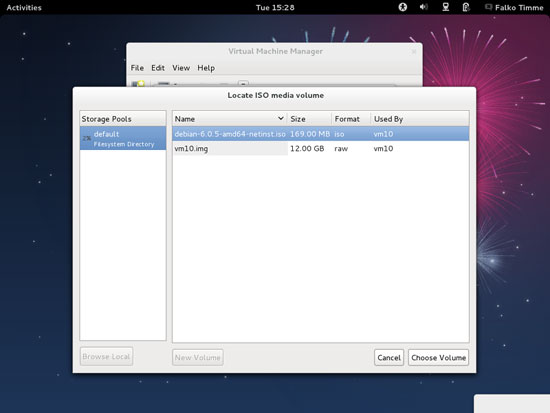
Select the debian-6.0.2.1-amd64-netinst.iso image that you created in chapter 4 and click on Choose Volume:
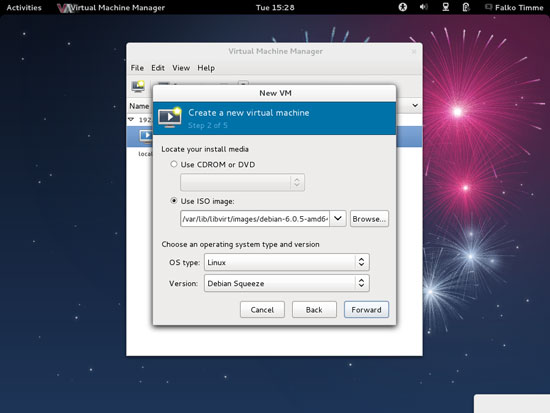
Now click on Forward:
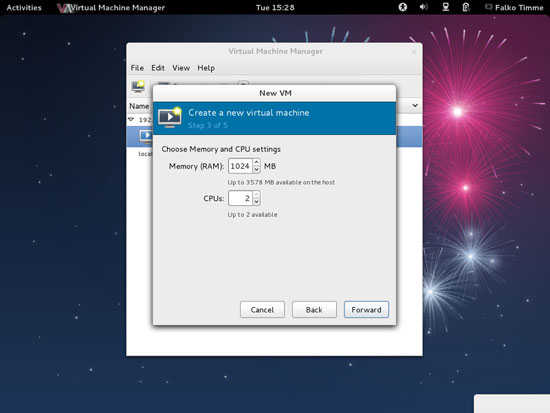
Assign memory and the number of CPUs to the virtual machine and click on Forward:
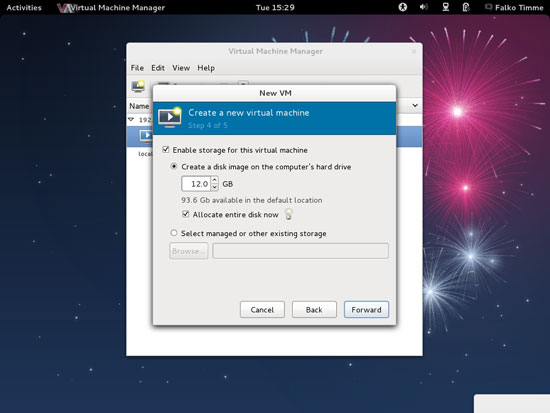
Now we come to the storage. Check Enable storage for this virtual machine, select Create a disk image on the computer's hard drive, specify the size of the hard drive (e.g. 12GB), and check Allocate entire disk now. Then click on Forward:
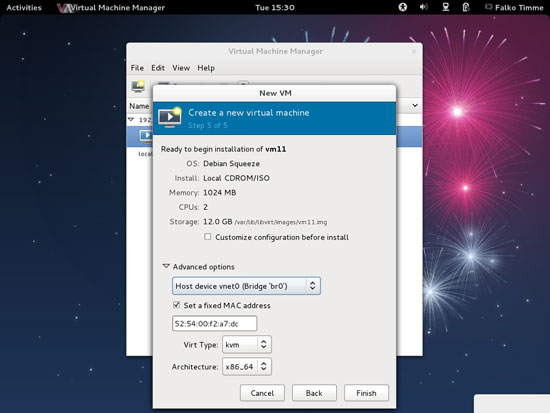
Now we come to the last step of the New VM dialogue. Go to the Advanced options section. Select Host device vnet0 (Bridge 'br0'); that is the name of the bridge which we created in chapter 2. Click on Finish afterwards:
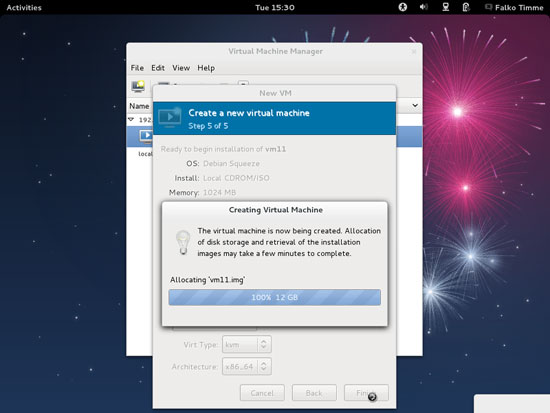
The disk image for the VM is now being created:
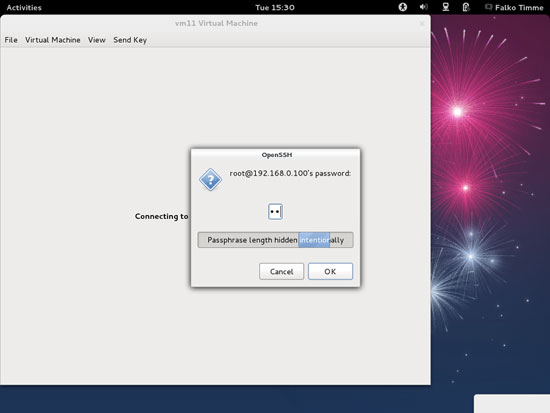
Afterwards, the VM will start. Type in the root password of the Fedora 17 KVM host:
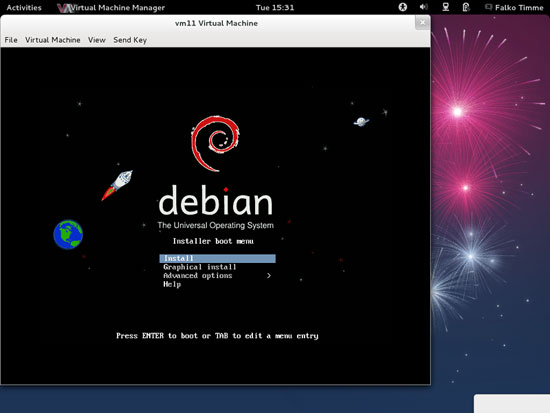
You should now be connected to the graphical console of the guest and see the Debian installer:
Now install Debian as you would normally do on a physical system.