How to Install Nextcloud with Apache and Let's Encrypt SSL on Ubuntu 22.04 LTS
This tutorial exists for these OS versions
- Ubuntu 22.04 (Jammy Jellyfish)
- Ubuntu 20.04 (Focal Fossa)
- Ubuntu 18.04 (Bionic Beaver)
On this page
Nextcloud is a free and open-source, file sharing and syncing solution that helps you to store your personal documents, files, photos, and other in a central location. It is very similar to other cloud storage solutions like Dropbox, Google Drive, iCloud, etc. You should switch to NextCloud if you are worried about privacy because you can install Nextcloud on your own server. You can upload files and other docs to your Nextcloud server and then sync all of them to your desktop pc, laptop, or smartphone.
In this tutorial, we will show you how to install Nextcloud on Ubuntu 22.04 server.
Requirements
- A server running Ubuntu 22.04.
- A valid domain name pointed to the server IP.
- A root password is configured on your server.
Install Apache, PHP, and MariaDB
Before starting, LAMP stack must be installed on your server. If not installed, you can install it with the following command:
apt install apache2 mariadb-server php php-cli php-fpm php-json php-intl php-imagick php-pdo php-mysql php-zip php-gd php-mbstring php-curl php-xml php-pear php-bcmath apache2 libapache2-mod-php -y
After installing all packages, edit the PHP configuration file and change some default settings:
nano /etc/php/8.1/apache2/php.ini
Change the following lines:
date.timezone = UTC memory_limit = 512M upload_max_filesize = 500M post_max_size = 500M max_execution_time = 300
Save and close the file then restart the Apache service to apply the changes:
systemctl restart apache2
Create a Database for Nextcloud
Nextcloud uses a MariaDB database as a database backend so you will need to create a database and user in MariaDB.
First, connect to the MariaDB shell with the following command:
mysql
Once you are connected to the MariaDB, create a database and user with the following command:
CREATE DATABASE nextcloud;
CREATE USER 'nextcloud'@'localhost' identified by 'password';
Next, grant all the privileges to the Nextcloud database with the following command:
GRANT ALL PRIVILEGES ON nextcloud.* TO 'nextcloud'@'localhost';
Next, flush the privileges and exit from the MariaDB with the following command:
FLUSH PRIVILEGES;
QUIT;
Download Nextcloud
At the time of writing the article, the latest version of Nextcloud is 24.0.1. You can download it with the following command:
wget https://download.nextcloud.com/server/releases/nextcloud-24.0.1.zip
Once the download is completed, unzip the downloaded file with the following command:
unzip nextcloud-24.0.1.zip
Next, move the extracted directory to the Apache web root with the following command:
mv nextcloud /var/www/html/
Next, change the ownership and permission of the Nextcloud directory using the following command:
chown -R www-data:www-data /var/www/html/nextcloud
chmod -R 775 /var/www/html/nextcloud
Create an Apache Virtual Host for Nextcloud
Next, you will need to create an Apache virtual host configuration file for Nextcloud. You can create it with the following command:
nano /etc/apache2/sites-available/next.conf
Add the following lines:
<VirtualHost *:80>
ServerAdmin [email protected]
DocumentRoot /var/www/html/nextcloud
ServerName next.example.com
ErrorLog /var/log/apache2/nextcloud-error.log
CustomLog /var/log/apache2/nextcloud-access.log combined
<Directory /var/www/html/nextcloud>
Options +FollowSymlinks
AllowOverride All
Require all granted
SetEnv HOME /var/www/html/nextcloud
SetEnv HTTP_HOME /var/www/html/nextcloud
<IfModule mod_dav.c>
Dav off
</IfModule>
</Directory>
</VirtualHost>
Save and close the file then activate the Apache virtual host and other required Apache modules with the following command:
a2ensite next
a2enmod rewrite dir mime env headers
Next, restart the Apache service to apply the changes:
systemctl restart apache2
You can also check the status of the Apache with the following command:
systemctl status apache2
You will get the Apache status in the following output:
? apache2.service - The Apache HTTP Server
Loaded: loaded (/lib/systemd/system/apache2.service; enabled; vendor preset: enabled)
Active: active (running) since Fri 2022-06-17 15:04:27 UTC; 4s ago
Docs: https://httpd.apache.org/docs/2.4/
Process: 16746 ExecStart=/usr/sbin/apachectl start (code=exited, status=0/SUCCESS)
Main PID: 16750 (apache2)
Tasks: 6 (limit: 2292)
Memory: 14.7M
CPU: 98ms
CGroup: /system.slice/apache2.service
??16750 /usr/sbin/apache2 -k start
??16751 /usr/sbin/apache2 -k start
??16752 /usr/sbin/apache2 -k start
??16753 /usr/sbin/apache2 -k start
??16754 /usr/sbin/apache2 -k start
??16755 /usr/sbin/apache2 -k start
Jun 17 15:04:27 ubuntu2204 systemd[1]: Starting The Apache HTTP Server...
Access Nextcloud Web Interface
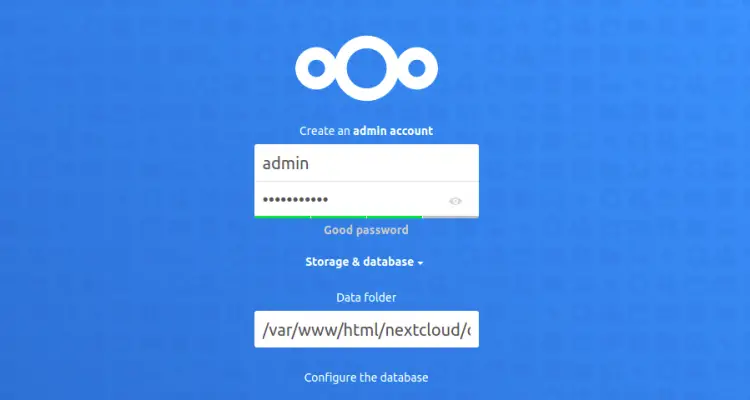
Now, open your web browser and access the Nextcloud web UI using the URL http://next.example.com. You should see the following screen:
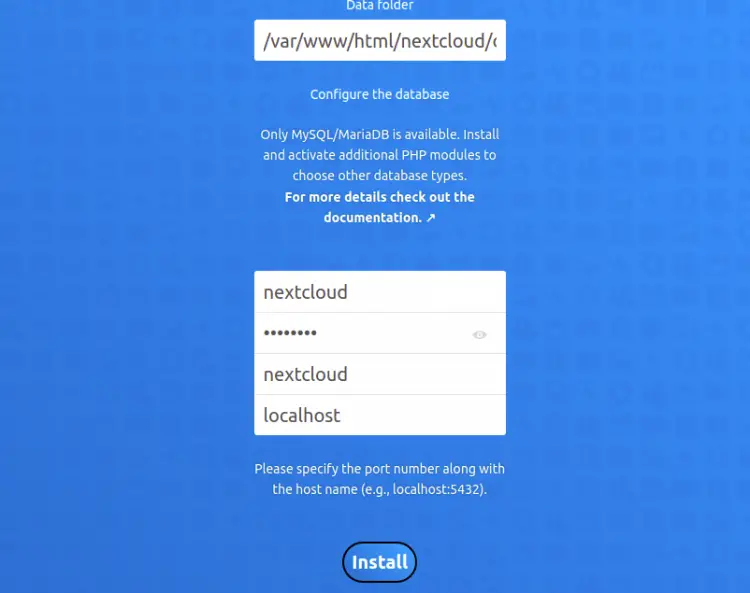
Define your admin username, password, database, and click on the Install button. Once the Nextcloud is installed, you should see the following screen:
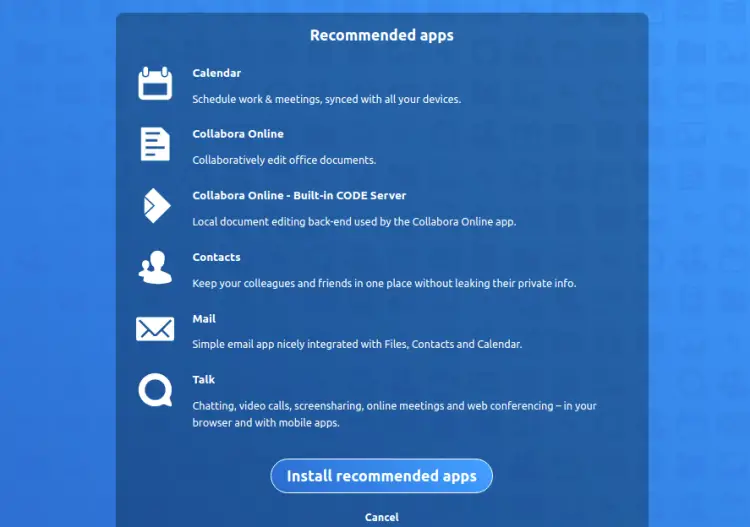
Click on the Install recommended apps to install all required applications. You should see the following screen:
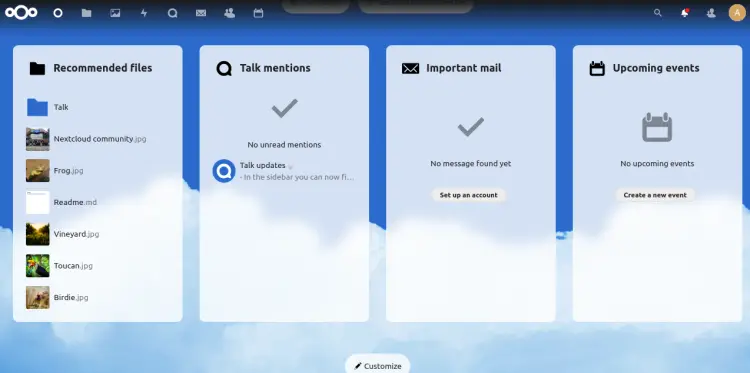
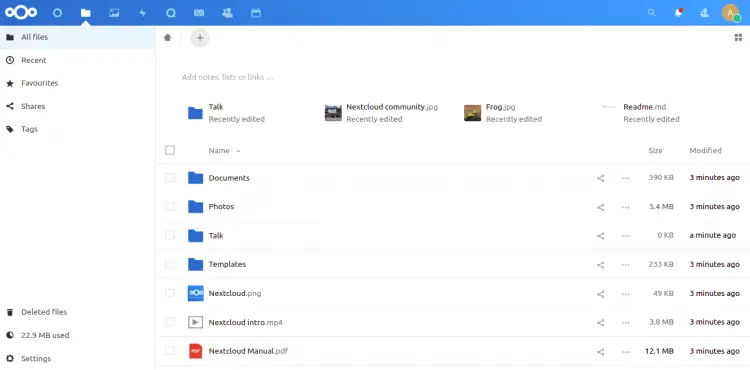
Click on the All files. You should see the Nextcloud storage manager on the following screen:
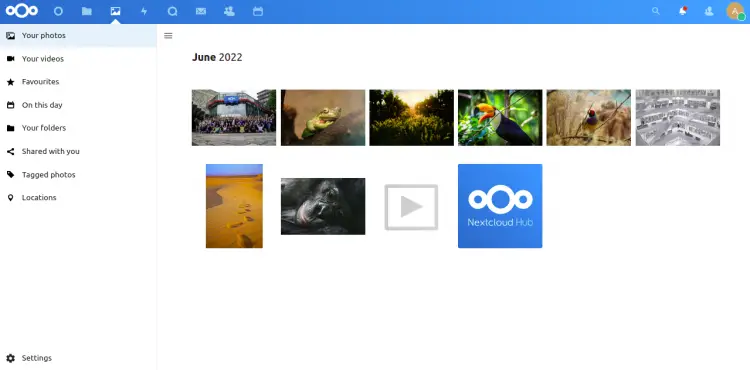
Click on the Your photos. You should see the Nextcloud photo manager on the following screen:
Enable SSL on Nextcloud
It is also recommended to enable SSL on the Nextcloud domain for secure communication. First, install the Certbot package with the following command:
apt-get install python3-certbot-apache -y
Once installed, run the following command to secure your website with Let's Encrypt SSL:
certbot --apache -d next.example.com
You will be asked to provide your email and accept the term of service as shown below:
Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator standalone, Installer None Enter email address (used for urgent renewal and security notices) (Enter 'c' to cancel): [email protected] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf. You must agree in order to register with the ACME server at https://acme-v02.api.letsencrypt.org/directory - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (A)gree/(C)ancel: A - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y Plugins selected: Authenticator apache, Installer apache Obtaining a new certificate Performing the following challenges: http-01 challenge for next.example.com Enabled Apache rewrite module Waiting for verification... Cleaning up challenges Created an SSL vhost at /etc/apache2/sites-available/next-le-ssl.conf Enabled Apache socache_shmcb module Enabled Apache ssl module Deploying Certificate to VirtualHost /etc/apache2/sites-available/next-le-ssl.conf Enabling available site: /etc/apache2/sites-available/next-le-ssl.conf
Next, select whether or not to redirect HTTP traffic to HTTPS as shown below:
Please choose whether or not to redirect HTTP traffic to HTTPS, removing HTTP access. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 1: No redirect - Make no further changes to the webserver configuration. 2: Redirect - Make all requests redirect to secure HTTPS access. Choose this for new sites, or if you're confident your site works on HTTPS. You can undo this change by editing your web server's configuration. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Select the appropriate number [1-2] then [enter] (press 'c' to cancel): 2
Type 2 and hit Enter to install the Let's Encrypt SSL for your website:
Enabled Apache rewrite module Redirecting vhost in /etc/apache2/sites-enabled/next.conf to ssl vhost in /etc/apache2/sites-available/next-le-ssl.conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Congratulations! You have successfully enabled https://next.example.com You should test your configuration at: https://www.ssllabs.com/ssltest/analyze.html?d=next.example.com - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at: /etc/letsencrypt/live/next.example.com/fullchain.pem Your key file has been saved at: /etc/letsencrypt/live/next.example.com/privkey.pem Your cert will expire on 2022-09-21. To obtain a new or tweaked version of this certificate in the future, simply run certbot again with the "certonly" option. To non-interactively renew *all* of your certificates, run "certbot renew" - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le
Conclusion
Congratulations! you have successfully installed Nextcloud with Apache and Let's Encrypt SSL on Ubuntu 22.04. You can now upload your files, docs, and photos, and sync them with your computer, laptop, and mobile devices.