Three Tools to Scan a Linux Server for Viruses, Malware and Rootkits
Servers connected to the Internet are exposed to a constant stream of attacks and scans throughout the day. While a firewall and regular system updates are a good first defense to keep the system safe, you should also regularly check that no attacker has infiltrated. The tools described in this tutorial are made for these tests, scanning for malware, viruses and rootkits. They should be run regularly, for example every night, and send you reports via email. You can also use Chkrootkit, Rkhunter and ISPProtect to scan a system when you notice suspicious activity, such as high load, suspicious processes or when the server suddenly starts sending malware.
All these scanners must be run as root users. Log in as root before running them. On Ubuntu, use:
sudo -s
to become the root user.
chkrootkit - Linux Rootkit Scanner
Chkrootkit is a classic rootkit scanner. It checks your server for suspicious rootkit processes and checks for a list of known rootkit files.
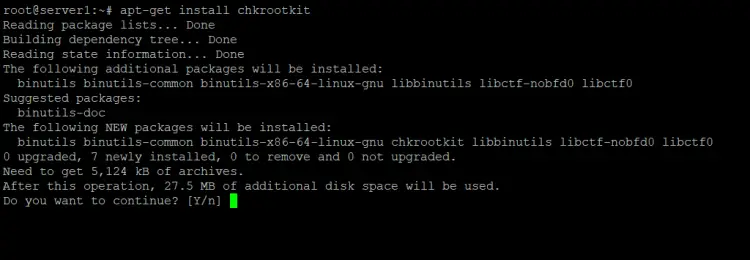
Either install the package that comes with your distribution (on Debian and Ubuntu you would run
apt-get install chkrootkit
), or download the sources from www.chkrootkit.org and install manually:
wget --passive-ftp ftp://ftp.pangeia.com.br/pub/seg/pac/chkrootkit.tar.gz
tar xvfz chkrootkit.tar.gz
cd chkrootkit-*/
make sense
Afterward, you can move the chkrootkit directory somewhere else, e.g. to /usr/local/chkrootkit:
cd ..
mv chkrootkit-<version>/ /usr/local/chkrootkit
and create a symlink for easy access:
ln -s /usr/local/chkrootkit/chkrootkit /usr/local/bin/chkrootkit
To check your server with chkrootkit, run the command:
chkrootkit
A common false positive report is:
Checking `bindshell'... INFECTED (PORTS: 465)
Don't worry when you get this message on an email server, this is the SMTPS (Secure SMTP) port of your mail system and a well known false positive.
You can even run chkrootkit by a cron job and get the results emailed to you. First, find out the path where chkrootkit is installed on your server with:
which chkrootkit
Example:
root@server1:/tmp/chkrootkit-0.52# which chkrootkit
/usr/sbin/chkrootkit
Chkrootkit is installed in the path /usr/sbin/chkrootkit, we need this path in the cron line below:
Run:
crontab -e
To create a cron job like this:
0 3 * * * /usr/sbin/chkrootkit 2>&1 | mail -s "chkrootkit output of my server" [email protected])
That would run chkrootkit every night at 3:00. Replace the path to chkrootkit with the path you received from the above command and exchange the email address with your actual address.
Lynis - Universal Security Auditing Tool and Rootkit Scanner
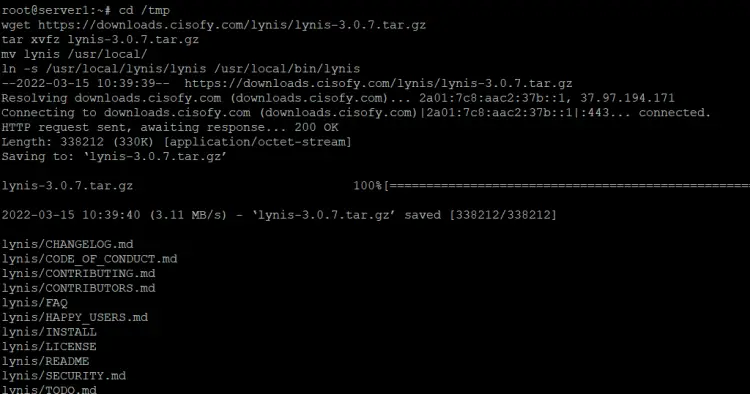
Lynis (formerly rkhunter) is a security auditing tool for Linux and BSD-based systems. It performs detailed auditing of many security aspects and configurations of your system. Download the latest Lynis sources from https://cisofy.com/downloads/lynis/:
cd /tmp
wget https://downloads.cisofy.com/lynis/lynis-3.0.7.tar.gz
tar xvfz lynis-3.0.7.tar.gz
mv lynis /usr/local/
ln -s /usr/local/lynis/lynis /usr/local/bin/lynis
This will install Lynis to the directory /usr/local/lynis and creates a symlink for easy access. Now run
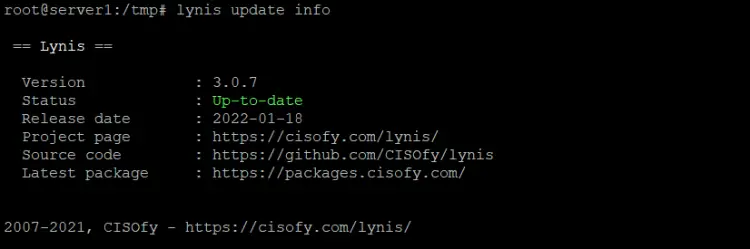
lynis update info
to check if you use the latest version.
Now you can scan your system for rootkits by running:
lynis audit system
Lynis will perform a few checks and then stops to give you some time to read the results. Press [ENTER] to continue with the scan.
In the end, it will show you a summary of the scan.
To run Lynis non-interactively, start it with the --quick option:
lynis --quick
To run Lynis automatically at night, create a cron job like this:
0 3 * * * /usr/local/bin/lynis --quick 2>&1 | mail -s "lynis output of my server" [email protected])
This will run Lynis every night a 3:00h. Replace the email address with your real address.
ISPProtect - Website Malware Scanner
ISPProtect is a malware scanner for web servers, it scans for malware in website files and CMS systems like WordPress, Joomla, Drupal etc. If you run a web hosting server, then the hosted websites are the most attacked part of your server and it is recommended to do sanity checks on them regularly. ISPProtect contains 5 scanning engines:
- Signature-based malware scanner.
- Heuristic malware scanner.
- A scanner to show the installation directories of outdated CMS systems.
- A scanner that shows you all the outdated WordPress plugins of the whole server.
- A database content scanner that checks MySQL databases for potentially malicious content.
ISPProtect is not free software, but there is a free trial that can be used without registration to check your server for malware or clean an infected system. The free license key to use the full version of the software once on your server is simply 'trial'.
ISPProtect requires PHP and ClamAV to be installed on the server, this should be the case on most hosting systems. ClamAV is used by ISPProtect in the first scan level with ISPProtect's own Malware signature set. In case you don't have a command-line PHP installed yet, execute:
sudo apt install php7.4-cli php7.4-curl clamav
on Debian 11 or Ubuntu 20.04 or
yum install PHP php-curl
on AlmaLinux, Fedora, CentOS or Rocky Linux.
Run the following commands to install ISPProtect.
mkdir -p /usr/local/ispprotect chown -R root:root /usr/local/ispprotect chmod -R 750 /usr/local/ispprotect cd /usr/local/ispprotect wget http://www.ispprotect.com/download/ispp_scan.tar.gz tar xzf ispp_scan.tar.gz rm -f ispp_scan.tar.gz ln -s /usr/local/ispprotect/ispp_scan /usr/local/bin/ispp_scan
To start ISPProtect, run:
ispp_scan
The scanner automatically checks for updates, then asks for the key (enter the word "trial" here) and then asks for the path of the websites, normally that's /var/www.
Please enter scan key: <-- trial
Please enter path to scan: <-- /var/www
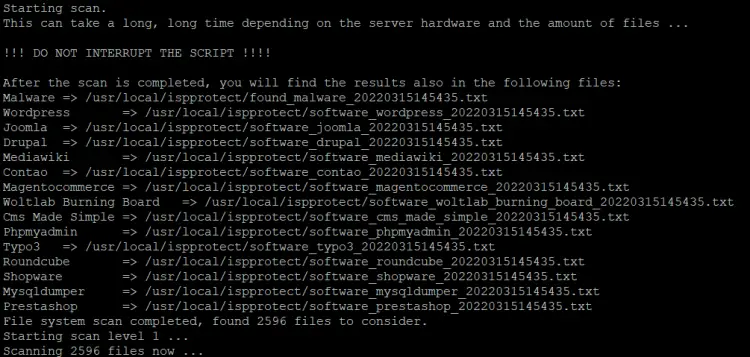
The scanner will now start the scan. Scanning progress is shown. The names of the infected files are shown on the screen at the end of the scan and the results are stored in file in the ISPProtect install directory for later use:
To update ISPProtect, run the command:
ispp_scan --update
To run ISPProtect automatically as a nightly cronjob, create a cron file with nano:
nano /etc/cron.d/ispprotect
and insert the following line:
0 3 * * * root /usr/local/ispprotect/ispp_scan --update && /usr/local/ispprotect/ispp_scan --path=/var/www --email-results=root@localhost --non-interactive --scan-key=AAA-BBB-CCC-DDD
Replace "root@localhost" with your email address, the scan report is sent to this address. Then exchange "AAA-BBB-CCC-DDD" with your license key. You can get a license key here.
A full list of command-line options of ISPProtect ispp_scan command can be obtained with:
ispp_scan --help