How To Protect Your Web Server With Sophos UTM
In this Howto I will show, how you can setup a webserver to be protected in the demilitarized zone of an enterprise grade firewall. I will use the Sophos UTM Gateway which is available as a software appliance to be installed on "any" hardware and is free for home and personal use.
Disclaimer: I am not employed by Sophos or Astaro or connected in any other way. I checked some other firewall distributions: completely open or with a community edition and an enterprise edition, but they did not offer such nice protection profiles and possibilities when exposing a webserver to the internet. This is why I chose to go with the Sophos UTM, although you need to register to use it.
The Scenario
I will setup a firewall with three network interfaces with the following IP addresses:
- eth0: WAN interface (ethernet)
- eth1: LAN 192.168.0.1/24 with DHCP
- eth2: DMZ 10.0.0.1/24 without DHCP and a webserver 10.0.0.10, that should be exposed externally.
The Download
You can download the Installer ISO image without registration at the download page. Which will lead you to this ISO image.
From the name of the download server you can see, that the Sophos UTM is the former Astaro Security Gateway. Three years ago Sophos acquired the German firewall company Astaro, located in Karlsruhe - which was the visionary in Gartners magic quadrants in 2009/2010.
The Sophos UTM is free for personal and home use. Although it is free, you need to register later and get a user license!
The Installation
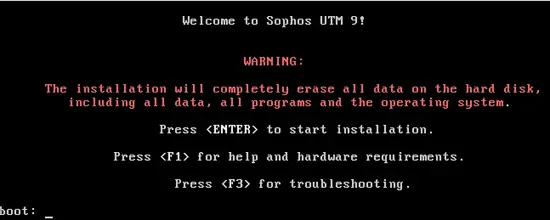
When booting the CD you are warned that it will wipe your disc.
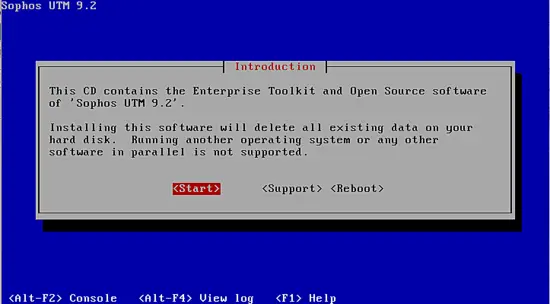
Of course the firewall will not allow any dual boot scenario ;-)
At the beginning of the installation you are asked to select a keyboard setting and a timezone.
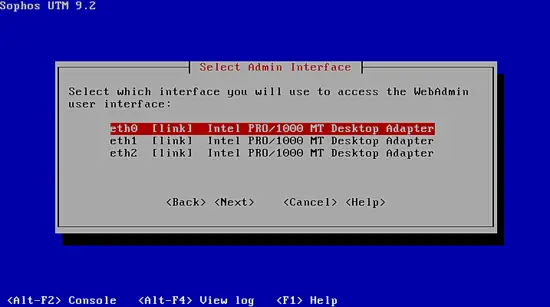
You may select, which of the interfaces is used to do the web based setup, later. I choose eth1 as the internal (LAN) interface...
If you are unsure of your interfaces, you should only plug in one cable.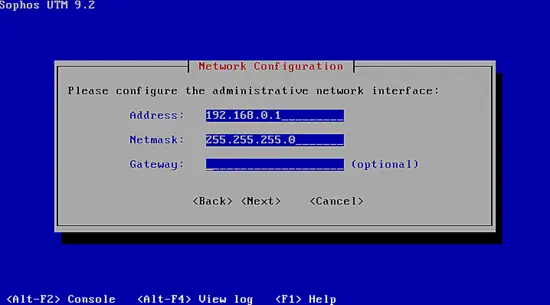
...and set the IP address to 192.168.0.1/24. You do not need to enter anything for the gateway!
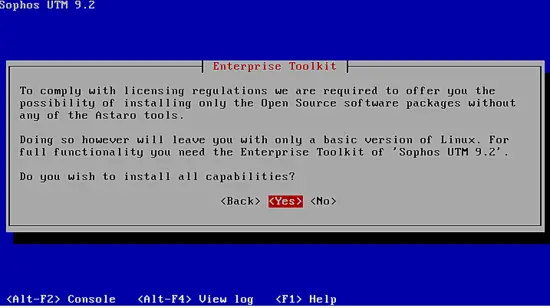
The installation also contains closed source components, you are informed about this. But installing the system without those components will only make limited sense!
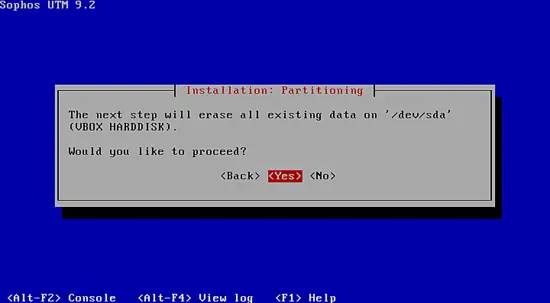
Yes, please use my harddisk! The harddisk is partitioned and the RPM packages are copied and installed.
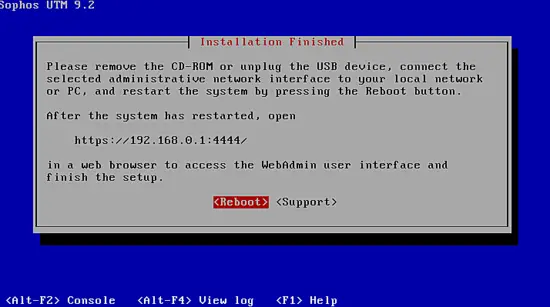
The installation is complete, you should remove the CD and after the reboot you can go to the specified website (Port 4444!) with your browser.
In the next step you will perform the basic setup of the firewall. So it is a good idea to only connect the firewall to the client machine, you use to setup the system!
The Setup
So take your client machine and use your browser to visit https://192.168.0.1:4444.
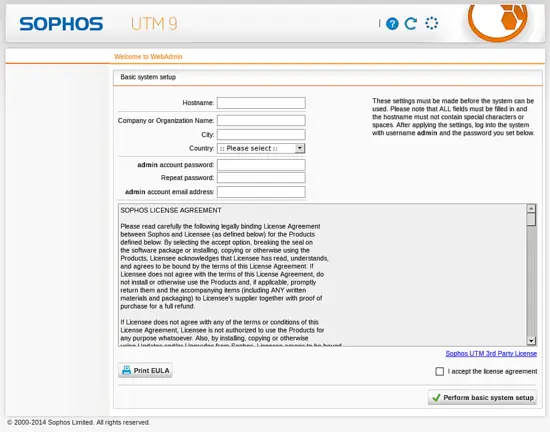
Although it is not noted, these fields are mandatory.
Choose a good password.
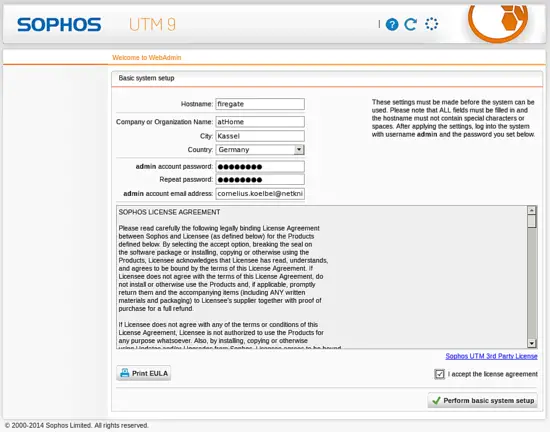
Click Perform basic setup.
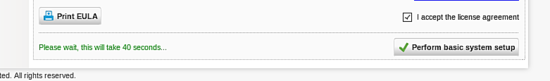
You only need to hit the button once! You might miss the information, that you have to wait 40 seconds. The system performs some tasks, like regenerating the SSL certificate based on the hostname you entered.
This is why you will get a certificate warning again, before you can login...
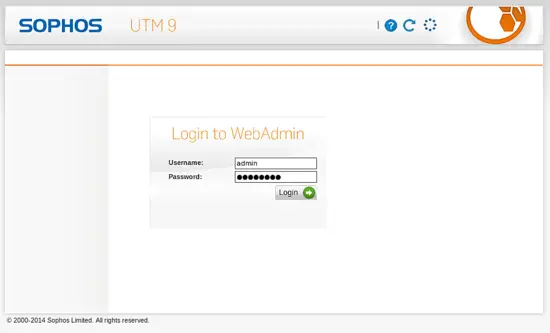
Enter your administrator credentials and a small setup wizard is launched.
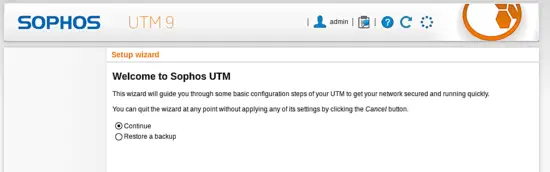
You could install a backup file, but we are doing a fresh install.
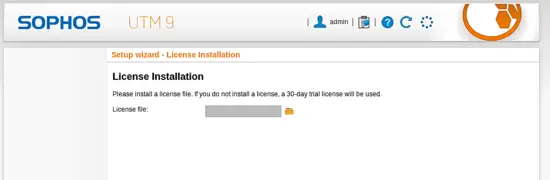
If you already have your home license file, you can upload it here, but I continue without the license, which will give me a 30 day test period.
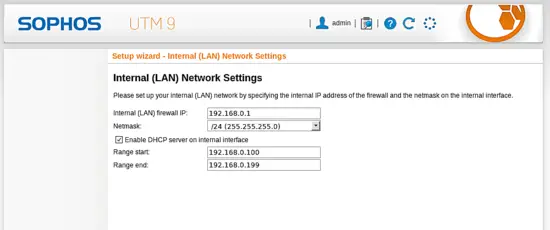
I choose eth1 where my client is connected to be the local network with the firwalls IP address 192.168.0.1.
I like the firewall to provide a DHCP service to the local network. But since I might want to use some fixed addresses, I will only use 192.168.0.100-199 as the IP pool.
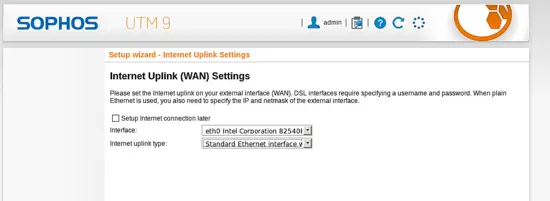
The WAN interface will be my eth0, which is an uplink to my local production network. This is why I choose Standard Ethernet interface in this scenario.
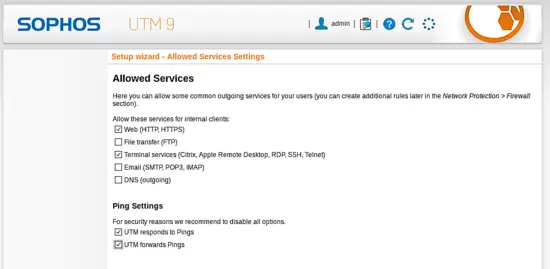
Now you can already do some choices for the firewall rules and define, which services the clients in the local network should be allowed to access on the internet.
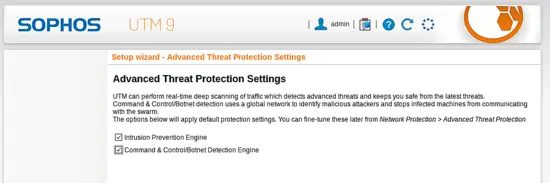
You can select the threat protection if it is ok for you to scan the content to block malicious code and data.
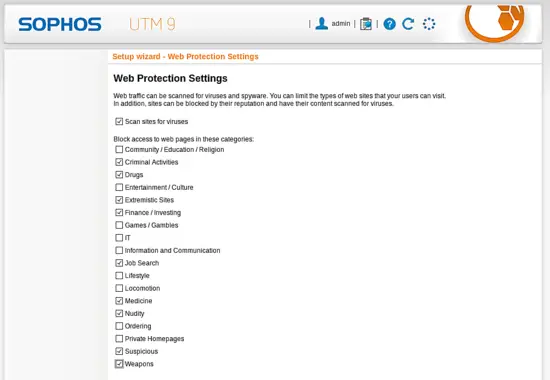
You can setup the category based webfilter, to block websites of certain categories. The websites are pre-categorized, so that the firewall already knows the category before fetching the website.
I choose to block some real evil content, that I do not want to see and I want my children not to know - like Finance / Investing!
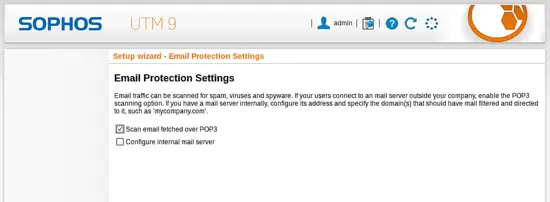
If by any chance some of your internel users still use unencrypted POP3 email accounts, you can scan those emails for viruses.
The safer solution might be to block unencrypted POP3...
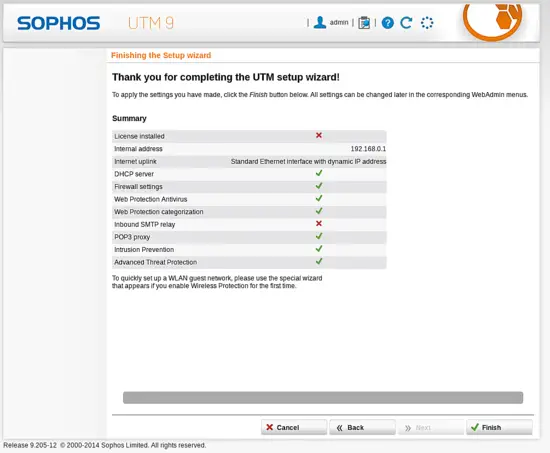
Perfect - we are done and allowed to click the button Finish.
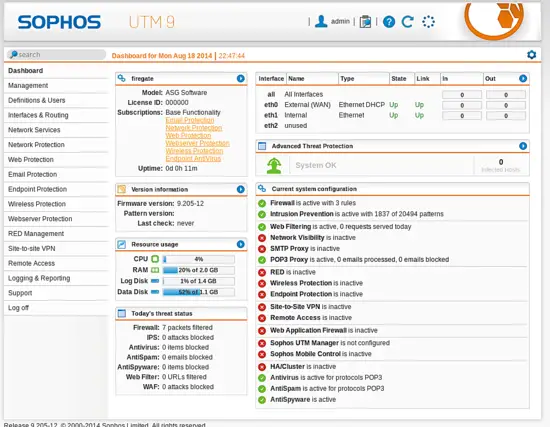
Finally we get a dashboard, an overview of the firewall system.
On the left side you can find a menu with all configurations and actions.
On the right side you see some statistics. You can see eth0 being our WAN interface and eth1 the LAN interface.
eth2 is unused and we will now set it up to be our demiliterized zone.
Setup the DMZ
Now we configure a new interface to be the demilitarized zone.
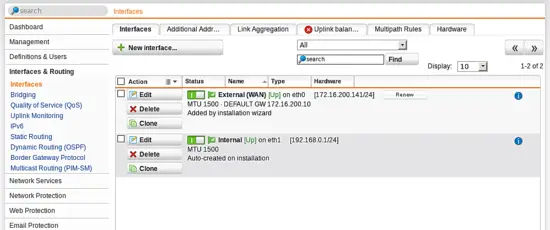
Go to Interfaces & Routing ? Interfaces and click New Interface
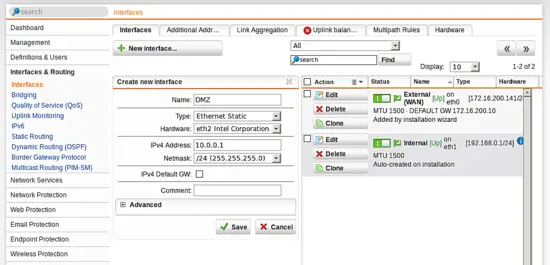
Fill out all information for the new interface. A static ethernet interface on hardware eth2 with the nice name DMZ. I choose the IP address 10.0.0.1/24.
You do not need to set a default gateway! Click Save.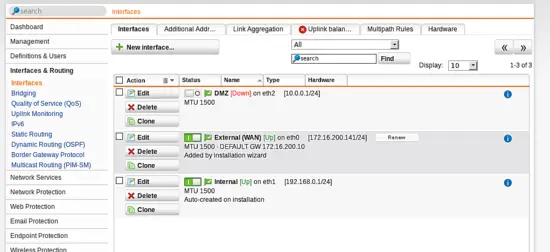
The new interface list will also show eth2, now. The small switch indicates that the interface is not active at the moment. The red [Down] is also an indication. You can click the switch to active the interface.
For me the [Down] indication did not update, until I change to another tab and returned to this tab again.
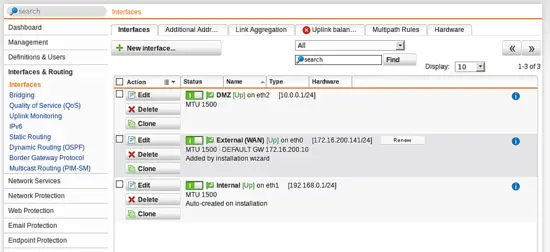
Finally, You see all three interfaces up and running.
At this point your LAN client should be able to ping the webserver and vice versa. Your LAN client can access the webserver in the DMZ, but your webserver can not access the LAN, perfect!
This firewall rule was set, as we configured the DMZ interface later and configured (during wizard run) that the LAN clients are allowed to access all web services.
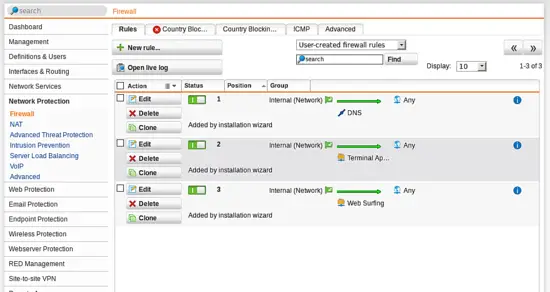
Go to Network Protection ? Firewall and you will see the firewall rules.
You can see the rule Websurfing allowing the internal network to connect to all webservers (including the DMZ). If you want the DMZ to interact with the outside world, you would have to add additional rules. But we skip this for the moment!
Our Webserver
As stated initially we want to expose our webserver to the internet. I assume that you have setup a webserver listening on IP 10.0.0.10 and connected to the DMZ port of the firewall.
Create Network object
First we need to create a Host object.
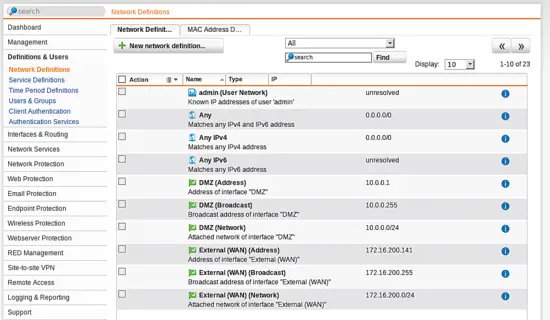
Go to Definitions & Users ? Network Definitions and click New Network definition to create an object for our webserver.
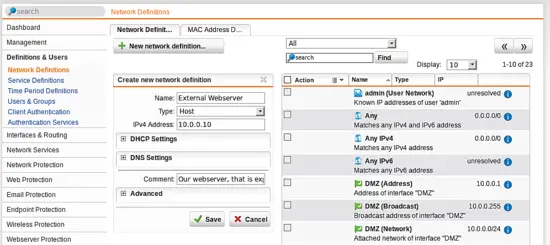
The new network definition is of type host. Enter a name like "External Webserver" and the IP address 10.0.0.10. Click Save.
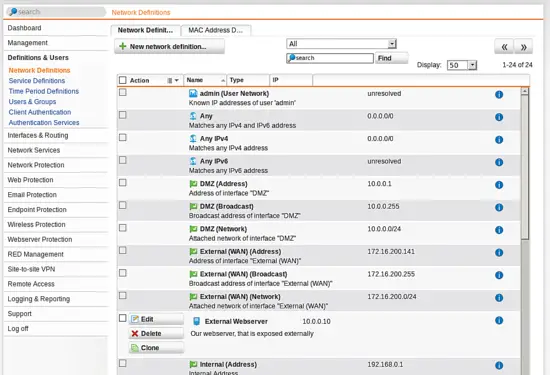
In the overview of the network object you can now see "External Webserver".
Create virtual webservice
The scenario of exposing a webservice to the internet is not called DNAT but "Virtual Webservice". You can search the dashboard for any configuration based on a keyword.
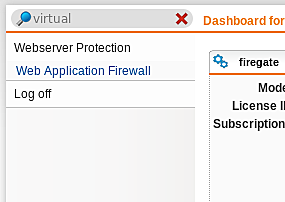
Searching for "virtual" returns Webserver protection with the submenu Webapplication firewall.
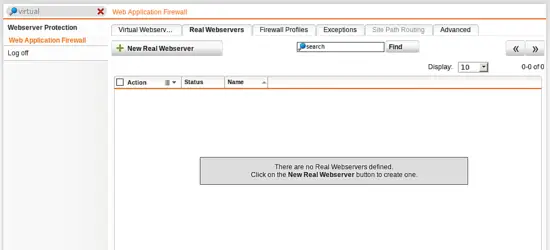
First you need to create a real webserver. On the tab Real Webservers click New Webserver.
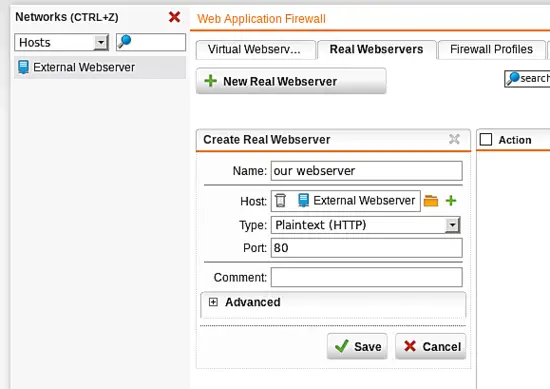
Choose a nice name like "our webserver" and add the network object "External Webservier" via Drag and Drop to the Host field. Select the port and the type (plaintext). Click Save.
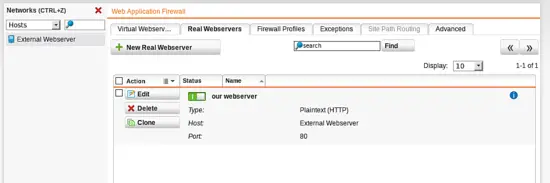
The "Real Webserver" definition now should appear in the webservers list.
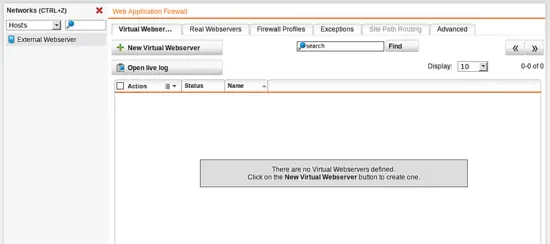
Now, go to the tab "Virtual Webserver" and click New Virtual Webserver.
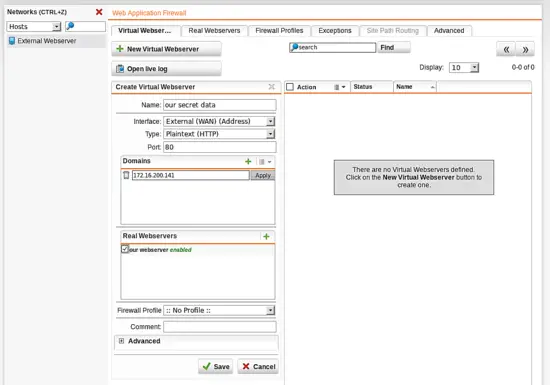
Enter a name for the virtual webserver like "our secret data". Select the interface (the WAN interface) where the content of the real webserver should be served.
Enter a domain name - only requests to this domain will be forwarded to the real webserver. I entered the external IP address (of the WAN interface), since I have not setup DNS correctly.
Finally, choose the real webserver to which the request should be forwarded. Click Save.
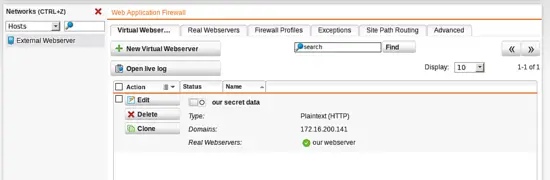
The virtual webserver "our secret data" now appears in the list of the virtual webservers. We only need to switch this virtual webserver on.
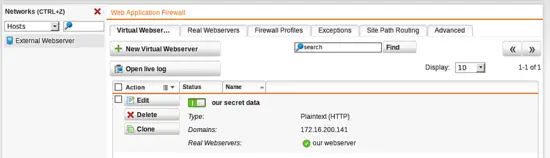
When switched on (green switch) the server now can be accessed from the internet. You do not need to define any firewall rule.
Firewall profiles
This is for further experimenting to use the full capabilities of the Sophos UTM.
In the virtual server you can choose a firewall profile.
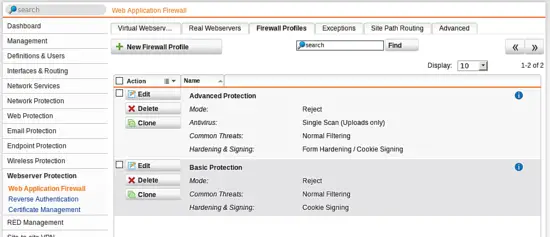
This can be defined in Webserver Protection ? Web Application Firewall ? Firewall Profiles and the firewall will then perform web application firewall features. It can scan the traffic between the client and your webserver for viruses, block content, harden input forms and much more. You could set the mode from "Reject" to "Monitor". But this is out of the scope of this howto. But feel free to play around and have fun!
Get your home-use-license
You can register and get your free home license here. The license file will be emailed to you.
In the firewall management search for the license menu...
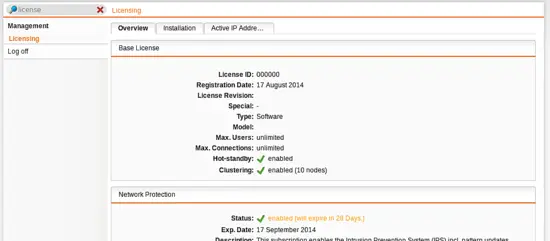
You see the trial license period.
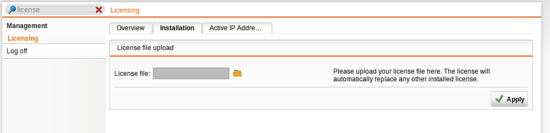
Select the license file that was emailed to you and...
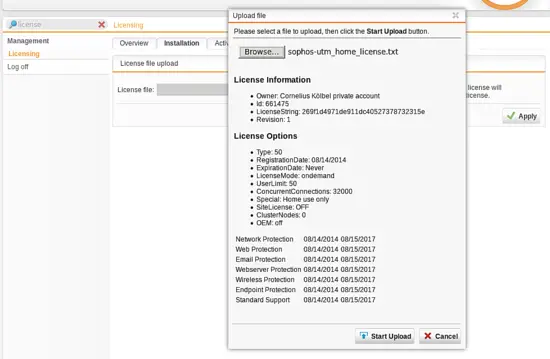
upload the license file and you will be fine...
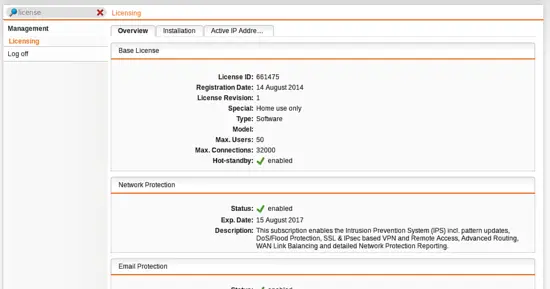
for the next three years.
Conclusion
We installed the enterprise grade firewall and configured it to allow protected access to a webserver in the demilitarized zone. We only made a first small step, what is possible. Feel free to experiment with new things like Email protection, Virus scanning or VPN. One of the next Howtos will deal with authentication with this firewall.
So stay tuned!


