How to Install osTicket with Nginx on Debian 11
osTicket is a free and open-source support ticket system used to scale and streamline your customer service and improve your customer experience. It offers a web-based interface to manage, organize, and track all support tickets. It is written in PHP and supports various databases such as MySQL and PostgreSQL.
Features
- Dashboard Reports
- Configurable Help Topic
- Service Level Agreements
- Ticket Filters
- Customer Support Portal
- Auto-Responder
This tutorial will show you how to install osTicket on Debian 11.
Prerequisites
- A server running Debian 11.
- A valid domain name is pointed with your server IP.
- A root password is configured on the server.
Getting Started
First, update and upgrade all system packages to the latest version using the following command.
apt update -y
apt upgrade -y
Once all the packages are updated, you can install other required packages with the following command:
apt install ca-certificates apt-transport-https software-properties-common wget curl
Once all the required packages are installed, you can proceed to the next step.
Install Nginx, and PHP
First, install the Nginx web server package using the following command.
apt install nginx -y
Next, add the PHP repository using the following command.
curl -sSL https://packages.sury.org/php/README.txt | bash -x
Next, install the latest version of PHP and other required PHP dependencies using the following command.
apt install php8.1 php8.1-mysql php8.1-cgi php8.1-fpm php8.1-cli php8.1-curl php8.1-gd php8.1-imap php8.1-mbstring php8.1-intl php8.1-apcu php8.1-common php8.1-gettext php8.1-bcmath php8.1-xml php8.1-dom -y
After the installation, edit the PHP configuration file.
nano /etc/php/8.1/fpm/php.ini
Change the following line.
cgi.fix_pathinfo=0
Save and close the file then restart the PHP-FPM service to apply the changes.
systemctl restart php8.1-fpm
Install and Configure MariaDB
First, install the MariaDB database server using the following command.
apt install mariadb-server -y
Next, secure the MariaDB installation with the following command.
mysql_secure_installation
Answer all the questions below:
Set root password? [Y/n] Y New password: Re-enter new password: Remove anonymous users? [Y/n] Y Disallow root login remotely? [Y/n] Y Remove test database and access to it? [Y/n] Y Reload privilege tables now? [Y/n] Y
Next, log in to the MariaDB shell as a root user.
mysql -u root -p
Next, create a database and user for osTicket.
MariaDB [(none)]> create database osticketdb;
MariaDB [(none)]> grant all privileges on osticketdb.* to osticketuser identified by 'secure-password';
Next, flush the privileges and exit from the MariaDB shell with the following command.
MariaDB [(none)]> flush privileges;
MariaDB [(none)]> exit;
Install osTicket
First, download the latest version of osTicket from the GitHub download page.
wget https://github.com/osTicket/osTicket/releases/download/v1.17.2/osTicket-v1.17.2.zip
Once the download is complete, create a directory for osTicket and extract the downloaded file inside that directory.
mkdir /var/www/html/osticket
unzip osTicket-v1.17.2.zip -d /var/www/html/osticket
Next, set ownership and permission on the osticket directory.
chown -R www-data:www-data /var/www/html/osticket
chmod -R 755 /var/www/html/osticket
Next, rename the osTicket sample configuration file.
mv /var/www/html/osticket/upload/include/ost-sampleconfig.php /var/www/html/osticket/upload/include/ost-config.php
Once you are finished, you can proceed to the next step.
Configure Nginx for osTicket
Next, you will need to create an Nginx virtual host configuration file for osTicket. You can create it with the following command.
nano /etc/nginx/conf.d/osticket.conf
Add the following configuration.
server {
listen 80;
server_name osticket.example.com;
root /var/www/html/osticket/upload;
index index.php index.html index.htm;
access_log /var/log/nginx/access.log;
error_log /var/log/nginx/error.log;
# Enable gzip
gzip on;
gzip_min_length 1000;
gzip_types text/plain application/x-javascript text/xml text/css application/xml;
set $path_info "";
location ~ /include {
deny all;
return 403;
}
if ($request_uri ~ "^/api(/[^\?]+)") {
set $path_info $1;
}
location ~ ^/api/(?:tickets|tasks).*$ {
try_files $uri $uri/ /api/http.php?$query_string;
}
if ($request_uri ~ "^/scp/.*\.php(/[^\?]+)") {
set $path_info $1;
}
location ~ ^/scp/ajax.php/.*$ {
try_files $uri $uri/ /scp/ajax.php?$query_string;
}
location / {
try_files $uri $uri/ index.php;
}
location ~ \.php$ {
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
include fastcgi_params;
include snippets/fastcgi-php.conf;
fastcgi_pass unix:/run/php/php8.1-fpm.sock;
}
}
Save and close the file then verify the Nginx configuration with the following command.
nginx -t
You will get the following output.
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok nginx: configuration file /etc/nginx/nginx.conf test is successful
Next, restart the Nginx service to apply the changes.
systemctl restart nginx
You can also check the Nginx status using the following command.
systemctl status nginx
You should see the Nginx status in the following output.
? nginx.service - A high performance web server and a reverse proxy server
Loaded: loaded (/lib/systemd/system/nginx.service; enabled; vendor preset: enabled)
Active: active (running) since Wed 2022-12-21 08:15:10 UTC; 4s ago
Docs: man:nginx(8)
Process: 24700 ExecStartPre=/usr/sbin/nginx -t -q -g daemon on; master_process on; (code=exited, status=0/SUCCESS)
Process: 24701 ExecStart=/usr/sbin/nginx -g daemon on; master_process on; (code=exited, status=0/SUCCESS)
Main PID: 24702 (nginx)
Tasks: 2 (limit: 2339)
Memory: 3.1M
CPU: 25ms
CGroup: /system.slice/nginx.service
??24702 nginx: master process /usr/sbin/nginx -g daemon on; master_process on;
??24703 nginx: worker process
Dec 21 08:15:10 debian11 systemd[1]: nginx.service: Succeeded.
Dec 21 08:15:10 debian11 systemd[1]: Stopped A high performance web server and a reverse proxy server.
Dec 21 08:15:10 debian11 systemd[1]: Starting A high performance web server and a reverse proxy server...
Dec 21 08:15:10 debian11 systemd[1]: nginx.service: Failed to parse PID from file /run/nginx.pid: Invalid argument
Dec 21 08:15:10 debian11 systemd[1]: Started A high performance web server and a reverse proxy server.
At this point, Nginx is installed and configured for osTicket. You can now proceed to access osTicket.
Access osTicket Web Interface
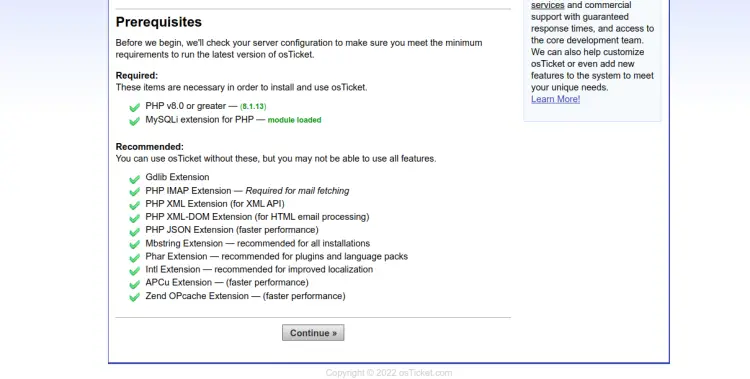
Open your web browser and access the osTicket installation page using the URL http://osticket.example.com. You should see the prerequisites page.
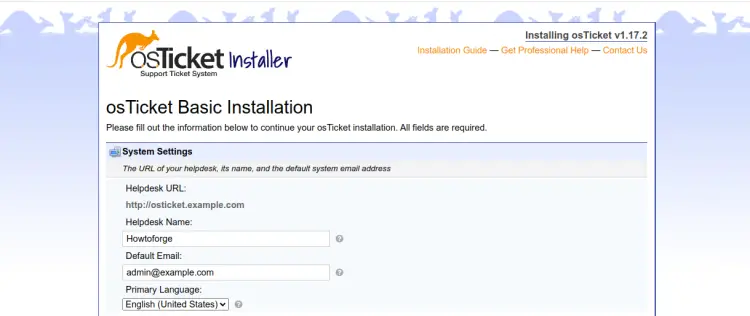
Click on the Continue. You should see the basic installation page.
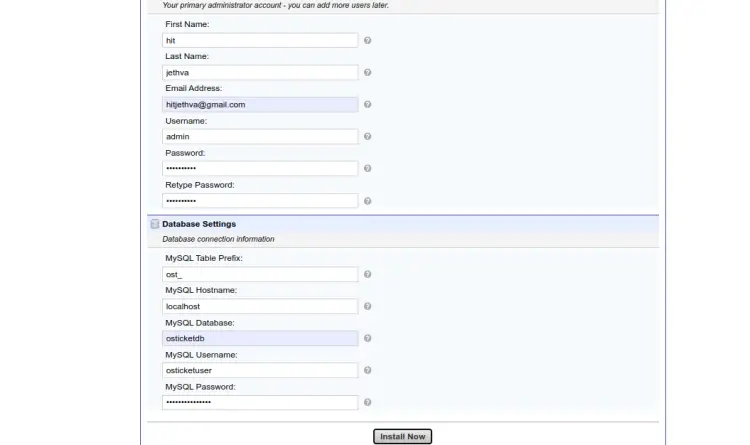
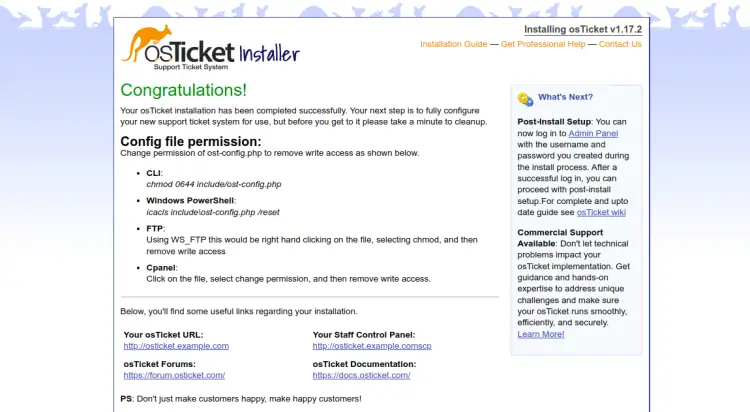
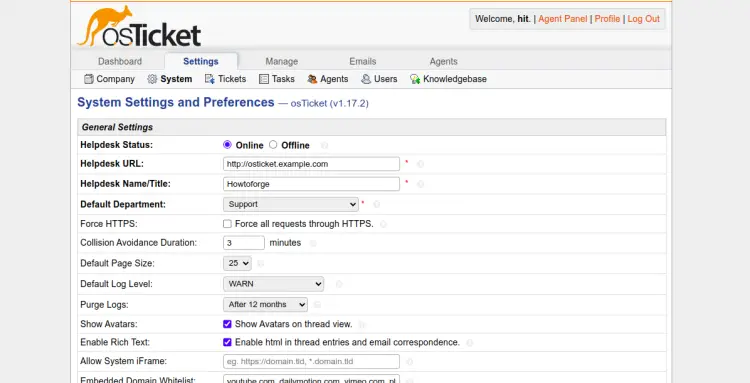
Define your helpdesk URL, name, email, database name, username, password, then click on the Install Now button to start the installation. Once the osTicket is installed, you should see the following page.
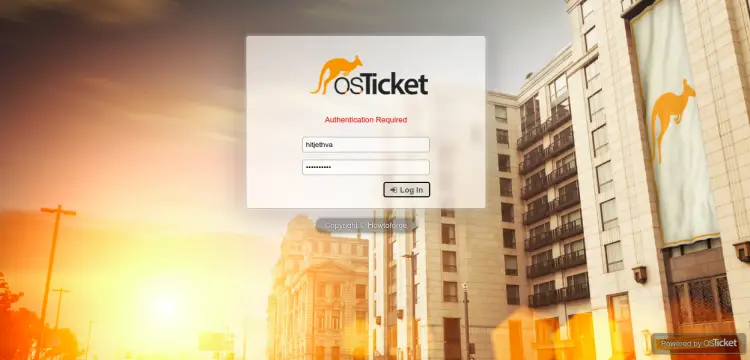
To access the osTicket control panel, type the URL http://osticket.example.com/scp in your web browser. You should see the osTicket login page.
Provide your admin username, password and click on the Login button. You should see the osTicket dashboard on the following screen.
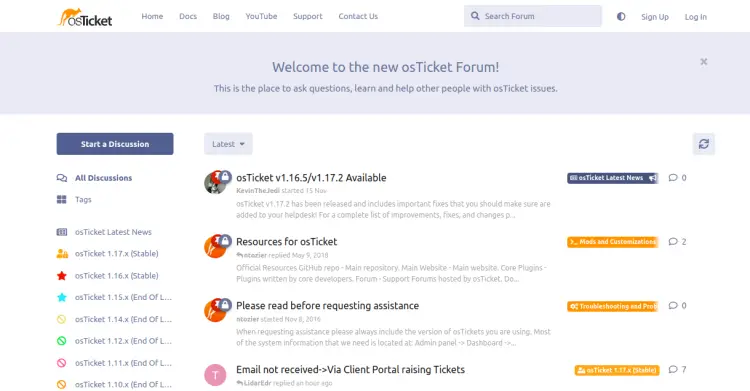
You can also access the osTicket forum page using the URL https://forum.osticket.com.
Enable SSL on osTicket
To install the Let's Encrypt SSL on the osTicket website, you will need to install the certbot package on your server.
First, install the Snap package manager with the following command:
apt install snapd
Next, update the Snap package to the latest version:
snap install core
snap refresh core
Next, install the certbot package using the following command:
snap install --classic certbot
Next, create a symbolic link for the Certbot binary to the system location:
ln -s /snap/bin/certbot /usr/bin/certbot
Next, run the following command to download and install Let's Encrypt SSL certificates:
certbot --nginx -d osticket.example.com
You will be asked to provide your email address and accept the term of service:
Saving debug log to /var/log/letsencrypt/letsencrypt.log Enter email address (used for urgent renewal and security notices) (Enter 'c' to cancel): [email protected] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at https://letsencrypt.org/documents/LE-SA-v1.3-September-21-2022.pdf. You must agree in order to register with the ACME server. Do you agree? - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing, once your first certificate is successfully issued, to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y
Type Y and press the Enter key to download and install the SSL certificates for your domain:
Account registered. Requesting a certificate for osticket.example.com Successfully received certificate. Certificate is saved at: /etc/letsencrypt/live/osticket.example.com/fullchain.pem Key is saved at: /etc/letsencrypt/live/osticket.example.com/privkey.pem This certificate expires on 2023-03-22. These files will be updated when the certificate renews. Certbot has set up a scheduled task to automatically renew this certificate in the background. Deploying certificate Successfully deployed certificate for osticket.example.com to /etc/nginx/conf.d/osticket.conf Congratulations! You have successfully enabled HTTPS on https://osticket.example.com - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - If you like Certbot, please consider supporting our work by: * Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate * Donating to EFF: https://eff.org/donate-le - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Conclusion
Congratulations! you have successfully installed osTicket with Nginx on Debian 11. You can now implement osTicket in your company and use it as a helpdesk management system. Feel free to ask me if you have any questions.