Using mod_spdy With Apache2 On CentOS 6.3
Version 1.0
Author: Falko Timme  Follow me on Twitter
Follow me on Twitter
SPDY (pronounced "SPeeDY") is a new networking protocol whose goal is to speed up the web. It is Google's alternative to the HTTP protocol and a candidate for HTTP/2.0. SPDY augments HTTP with several speed-related features such as stream multiplexing and header compression. To use SPDY, you need a web server and a browser (like Google Chrome and upcoming versions of Firefox) that both support SPDY. mod_spdy is an open-source Apache module that adds support for the SPDY protocol to the Apache HTTPD server. This tutorial explains how to use mod_spdy with Apache2 on CentOS 6.3.
I do not issue any guarantee that this will work for you!
1 Preliminary Note
SPDY runs over HTTPS, so we need an HTTPS-enabled web site to test SPDY. Please note that SPDY will fall back to HTTPS if the user's browser does not support SPDY or if things go wrong, so installing mod_spdy doesn't hurt your existing setup.
I'm assuming that you have a working LAMP setup, as described on Installing Apache2 With PHP5 And MySQL Support On CentOS 6.3 (LAMP).
For testing purposes I will simply use the default SSL web site that comes with the Apache package on CentOS (you don't need to do this if you already have an SSL web site on your server). If you have no SSL web site, you can enable the default SSL web site as follows:
yum install mod_ssl openssl
openssl genrsa -out ca.key 4096
openssl req -new -key ca.key -out ca.csr
openssl x509 -req -days 365 -in ca.csr -signkey ca.key -out ca.crt
cp ca.crt /etc/pki/tls/certs
cp ca.key /etc/pki/tls/private/ca.key
cp ca.csr /etc/pki/tls/private/ca.csr
vi +/SSLCertificateFile /etc/httpd/conf.d/ssl.conf
[...] SSLCertificateFile /etc/pki/tls/certs/ca.crt [...] SSLCertificateKeyFile /etc/pki/tls/private/ca.key [...] |
/etc/init.d/httpd restart
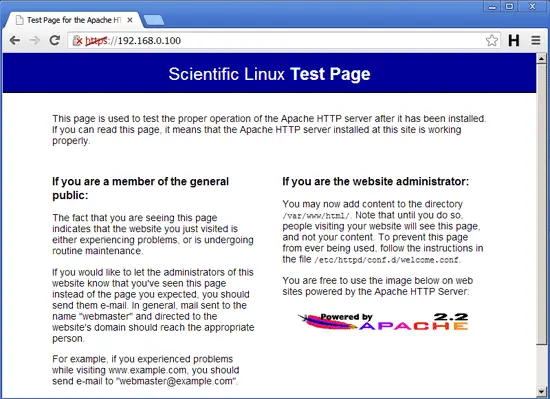
Go to the default SSL web site's URL (e.g. https://www.example.com) and test if it works (I'm using the default self-signed certificate here, that's why I have a certificate warning, but this has no effect on using SPDY):
2 Installing mod_spdy
First make sure at is installed:
yum install at
Google provides Fedora/CentOS packages for mod_spdy on https://developers.google.com/speed/spdy/mod_spdy/. Simply download the correct one for your architecture (32- or 64-bit) to your server...
64-bit:
cd /tmp
wget https://dl-ssl.google.com/dl/linux/direct/mod-spdy-beta_current_x86_64.rpm
32-bit:
cd /tmp
wget https://dl-ssl.google.com/dl/linux/direct/mod-spdy-beta_current_i386.rpm
... and install it as follows:
rpm -U mod-spdy-*.rpm
Restart Apache afterwards:
/etc/init.d/httpd restart
The good thing is, mod_spdy needs no configuration, it works out of the box!
(In fact, there is a configuration file, /etc/httpd/conf.d/spdy.conf, but the default settings should be ok.
cat /etc/httpd/conf.d/spdy.conf
LoadModule spdy_module /usr/lib64/httpd/modules/mod_spdy.so
<IfModule spdy_module>
# Turn on mod_spdy. To completely disable mod_spdy, you can set
# this to "off".
SpdyEnabled on
# In order to support concurrent multiplexing of requests over a
# single connection, mod_spdy maintains its own thread pool in
# each Apache child process for processing requests. The default
# size of this thread pool is very conservative; you can override
# it with a larger value (as below) to increase concurrency, at
# the possible cost of increased memory usage.
#
#SpdyMaxThreadsPerProcess 30
# Memory usage can also be affected by the maximum number of
# simultaneously open SPDY streams permitted for each client
# connection. Ideally, this limit should be set as high as
# possible, but you can tweak it as necessary to limit memory
# consumption.
#
#SpdyMaxStreamsPerConnection 100
</IfModule>
|
You can learn more about the configuration options on https://developers.google.com/speed/spdy/mod_spdy/install.
)
3 Testing
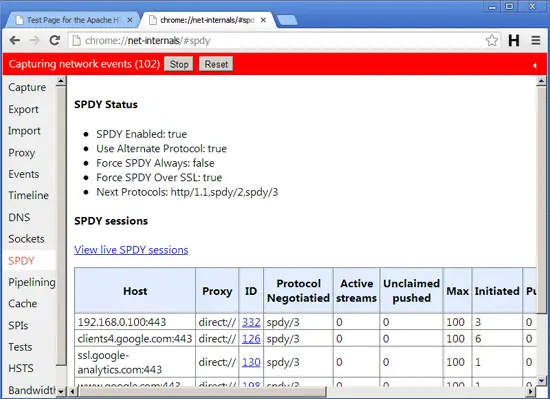
Now let's test if SPDY is working. We need a browser with SPDY support. e.g. Google Chrome. Open Chrome and reload your SSL web site (e.g. https://www.example.com) - it is important that you reload it so that it can use SPDY (the first time you loaded it in chapter 1 it used normal HTTPS). Afterwards, open a new tab and type in the URL
chrome://net-internals/#spdy
If everything went well, your SSL vhost should now be listed in the table which means SPDY support is working.
(Because of SPDY's fallback mechanism to HTTPS, your SSL vhost will still work in any other browser that does not support SPDY.)
4 Links
- SPDY: https://developers.google.com/speed/spdy/
- Apache mod_spdy: http://code.google.com/p/mod-spdy/
- mod_spdy Binary Packages: https://developers.google.com/speed/spdy/mod_spdy/
- mod_spdy Configuration: https://developers.google.com/speed/spdy/mod_spdy/install
- Apache: http://httpd.apache.org/
- CentOS: http://www.centos.org/