How to Setup FTP Server with vSFTPd and TLS on Ubuntu 22.04
This tutorial exists for these OS versions
- Ubuntu 22.04 (Jammy Jellyfish)
- Ubuntu 20.04 (Focal Fossa)
- Ubuntu 18.04 (Bionic Beaver)
On this page
vSFTPd or Very Secure FTP Daemon is free and open-source FTP Server software. It's an FTP Daemon for Unix-like operating systems and comes with GNU General Public License. vSFTPd is one of the most used FTP daemons, it's fast and lightweight in system resources, secure through PAM and SSL integration, and stable. vSFTPd earned the trust because of its maturity, used by large companies such as RedHat, SUSE, Debian, Gnome, KDE, etc.
vSFTPd can be run with IPv6, and also supports virtual IP configuration and virtual users. It can be run as a standalone daemon or using the inetd operation. On user management, vSFTPd provides a feature that lets the user have their own configuration, as per-source-IP limits and reconfigurability, and also bandwidth throttling. It also supports a pluggable authentication module (PAM) for virtual users, and also provides security integration with SSL/TLS.
In this tutorial, I will show you how to set up an FTP server with VSFTPD (Very Secure FTP Daemon) on the Ubuntu 22.04 server. This post includes how to secure the vSFTPd with TLS/SSL certificates.
Prerequisites
Before you begin with this guide, you should have the following requirements:
- An Ubuntu 22.04 server.
- A non-root user with root/administrator privileges.
- An FTP Client is installed on the local machine.
Installing vSFTPd Package
The default Ubuntu repository provides multiple FTP daemon, including the vSFTPd package. This makes administrator easier to install and set up an FTP server without any additional repository or third-party repository.
The first step here is to install the vSFTPd to the Ubuntu server. But before installing the package, you will be required to update and refresh the package index for your system. Type the following command to update and refresh the Ubuntu repository.
sudo apt update
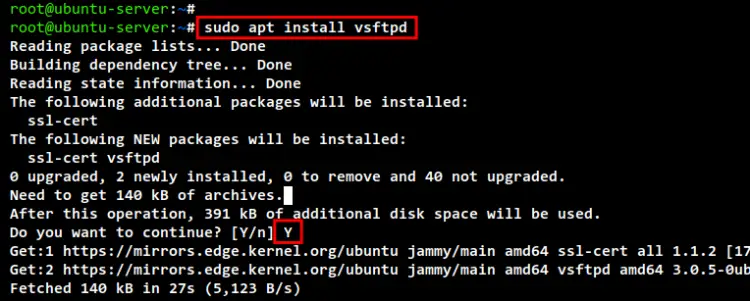
Now install the vSFTPd package using the following command. Input Y to confirm the installation and press ENTER to continue. And the vSFTPd installation will begin.
sudo apt install vsftpd
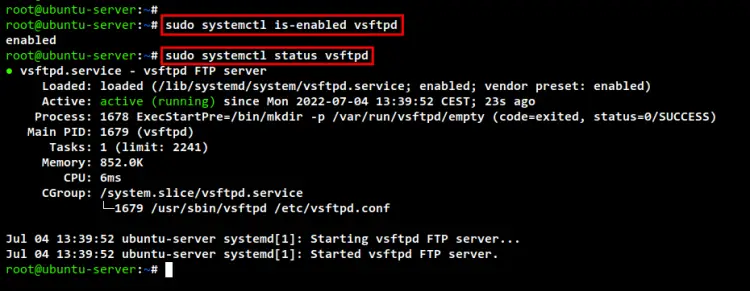
After the vSFTPd installation is finished, run the command below to check and verify the vSFTPd service. You should see the vSFTPd service is "enabled", which means will be running automatically at system startup. Also, the current status of the vSFTPd service is running.
sudo systemctl is-enabled vsftpd
sudo systemctl status vsftpd
Configuring VSFTPD Server
In this section, you will generate the SSL/TLS certificates to enable vSFTPd over TLS. Then, you will start editing the vSFTPd configuration file "/etc/vsftpd.conf" for creating a secure FTP server.
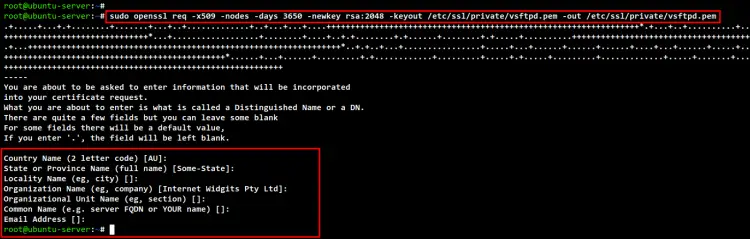
Run the openssl command below to generate the Self-Signed SSL/TLS certificate for the vSFTPd server. This will prompt you for some information about your certificate, be sure to input details information. The certificate will be stored at "/etc/ssl/private/vsftpd.pem"
sudo openssl req -x509 -nodes -days 3650 -newkey rsa:2048 -keyout /etc/ssl/private/vsftpd.pem -out /etc/ssl/private/vsftpd.pem
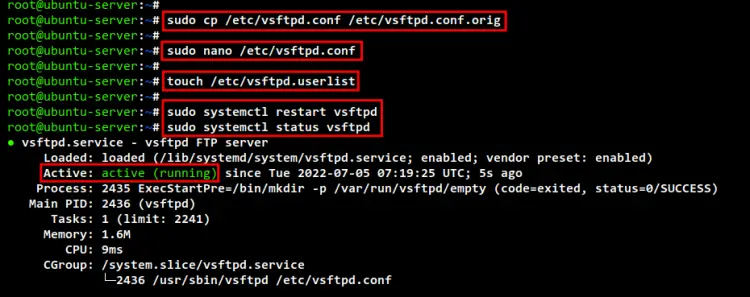
Next, backup the default vsFTPd configuration before editing the file using the following command.
sudo cp /etc/vsftpd.conf /etc/vsftpd.conf.orig
Once the original file is copied, open the vSFTPd configuration file "/etc/vsftpd.conf" using the command below.
sudo nano /etc/vsftpd.conf
Ensure the option "anonymous_enable" is set to "NO" to disable anonymous access to the FTP server.
anonymous_enable=NO
Uncomment the "local_enable" option to allow users to access and log in to the FTP server. This option must be enabled when you need to set up virtual users, which will enable a normal user account in the /etc/passwd file to be able to log in to the FTP server.
local_enable=YES
Uncomment the "write_enable" option to allow users to be able to write and upload files to the FTP server.
write_enable=YES
Uncomment the "chroot_local_users" to enable jail for each FTP user. This will add more security to your FTP server because every FTP user will automatically be placed in their home directory after logging in. And one user will not be able to access or see or list files belonging to another user.
chroot_local_users=YES
Add the following configuration to enable virtual users on the vSFTPd server. The variable "$USER" will be taken from the system environment variable, so each FTP user will have their own home directory and automatically be placed at the "/home/username/chroot" directory after logging in.
user_sub_token=$USER
local_root=/home/$USER/chroot
Add the following configuration to set up the range port for the PASV data connection of the vSFTPd server.
pasv_min_port=40000
pasv_max_port=50000
Now add the following configuration to enable virtual users on the vSFTPd server. Only users in the "/etc/vsftpd.userlist" will be allowed to log in to the FTP server.
userlist_enable=YES
userlist_file=/etc/vsftpd.userlist
userlist_deny=NO
Change the default SSL/TLS configuration of the vSFTPd using the configuration below. This will force FTP users to use a secure TLS connection on both login and data transfer, also only using the TLSv1.
rsa_cert_file=/etc/ssl/private/vsftpd.pem
rsa_private_key_file=/etc/ssl/private/vsftpd.pem
ssl_enable=YES
force_local_data_ssl=YES
force_local_logins_ssl=YES
ssl_tlsv1=YES
ssl_sslv2=NO
ssl_sslv3=NO
require_ssl_reuse=NO
ssl_ciphers=HIGH
Save and close the file when you are done.
Next, create a new file for the FTP users list using the command below. This file is needed for defining FTP users.
touch /etc/vsftpd.userlist
Lastly, run the following command to restart the vSFTPd service and apply new changes. Then, check and verify the vSFTPd service. And you should see the vSFTPd service is running with a new configuration and SSL/TLS enabled on top of it.
sudo systemctl restart vsftpd
sudo systemctl status vsftpd
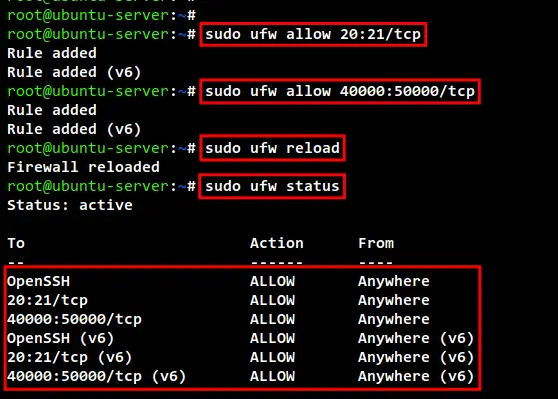
Setting Up UFW Firewall
Once the vSFTPd server is configured, it's time to add the UFW firewall rules for your FTP server. You must add FTP TCP ports "20" and "21" to the firewall, also the range of PASV data connection ports that you configured is "40000:50000".
Before adding any firewall rules, be sure the UFW firewall is enabled. You can check the status of the UFW firewall using the following command. If you get the list of enabled rules, then your firewall is active.
sudo ufw status
If you get the output message such as "inactive", then you need to enable the UFW firewall using the below command. You will need to add the "OpenSSH" application rule, then enable the UFW firewall.
sudo ufw allow "OpenSSH"
sudo ufw enable
Now add vSFTPd service ports "20:21" and "40000:50000" using the ufw command below.
sudo ufw allow 20:21/tcp
sudo ufw allow 40000:50000/tcp
Run the following command to reload and verify the UFW firewall status. And you should get the port "20:21" and "40000:50000" added to the UFW firewall.
sudo ufw reload
sudo ufw status
Adding FTP User
At this point, you have completed the configuration of a secure FTP Server using vSFTPd with SSL/TLS enabled and secured your system using the UFW firewall. It's time to set up and create an FTP user, which is a Linux user account.
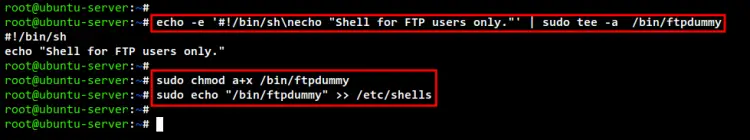
For the FTP users, if you set up an FTP user with the shell "/bin/false" or "/usr/sbin/nologin", your FTP user will not be able to log in to the FTP server. It's because the vSFTPd service is used the PAM service by default and FTP users required a valid shell.
So now run the following command to create a dummy shell for FTP users "/bin/ftpdummy".
echo -e '#!/bin/sh\necho "Shell for FTP users only."' | sudo tee -a /bin/ftpdummy
sudo chmod a+x /bin/ftpdummy
Add the new shell "/bin/ftpdummy" to the configuration file "/etc/shells". And now you are ready to create new FTP users.
sudo echo "/bin/ftpdummy" >> /etc/shells
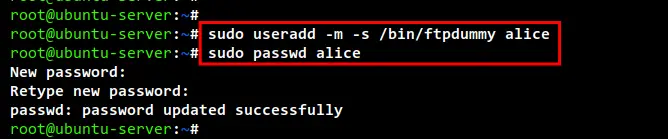
In this demo, we will use the user with the name "alice" as the FTP user. Now run the following command to create a new user named "alice" and with the default shell "/bin/ftpdummy". Then, you can set up the password for the new user, be sure to use a strong password.
sudo useradd -m -s /bin/ftpdummy alice
sudo passwd alice
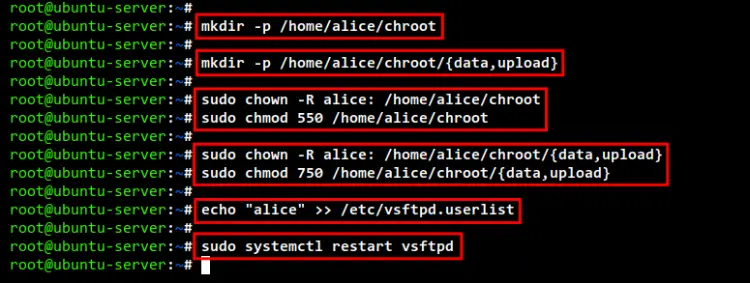
Next, create a new "chroot" directory under the user home directory using the below command. When user "alice" logs in to the FTP server, the "chroot" directory will be the default home directory.
mkdir -p /home/alice/chroot
Under the "chroot" directory, create another directory named "data" and "upload". Both directories will be used for FTP users to upload their files.
mkdir -p /home/alice/chroot/{data,upload}
Now run the below command to change the correct permission and ownership of the FTP data directory. The "chroot" directory must have the permission "550", but the "data" and "upload" directories must have the permission "750" so the user can write/upload files into it.
sudo chown -R alice: /home/alice/chroot
sudo chmod 550 /home/alice/chroot
sudo chown -R alice: /home/alice/chroot/{data,upload}
sudo chmod 750 /home/alice/chroot/{data,upload}
Next, add the user "alice" to the vSFTPd user list file "/etc/vsftpd.userlist" using the following command. Then, you can restart the vSFTPd service to apply new changes. Your new FTP user is ready.
echo "alice" >> /etc/vsftpd.userlist
sudo systemctl restart vsftpd
Connecting to the FTP Server
You have completed the installation and configuration of the FTP Server using the vSFTPd on the Ubuntu server. Now let's check and verify by logging in to the FTP Server.
Be sure you have the FTP Client application installed on your local machine. In this demo, we will use "FileZilla", a free and open-source FTP client that can be installed on Linux, Windows, and macOS.
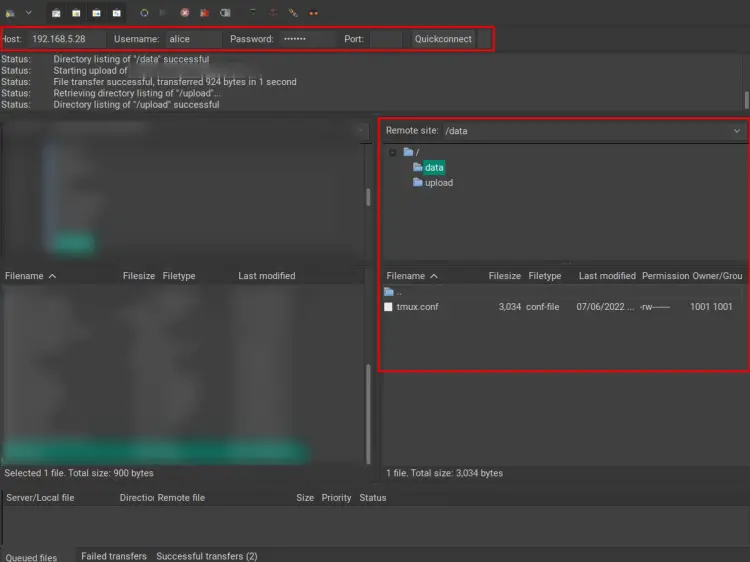
Open up your FTP Client software and input details Host/IP address, username, and password of your FTP server. Then, click the "Quick connect" button.
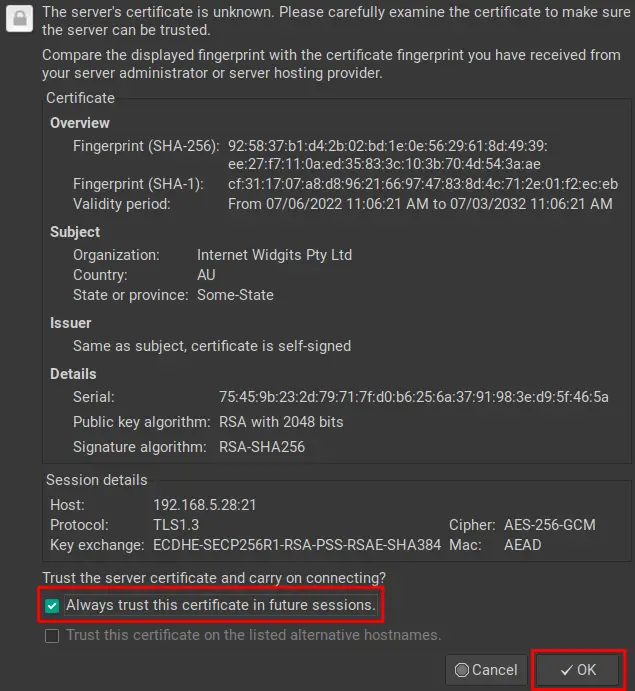
Now you will be prompted to accept the Self-Signed certificate of the FTP Server. Select the option "Trust ..." and click "OK".
After you have connected, you will be logged in to the chroot jail home directory and you will two directories "data" and "upload". You will not be able to upload files to the chroot jail directory, but you can upload files to the "data" and "upload" directories.
Conclusion
Congratulation! From this post, you successfully created the FTP Server with vSFTPD on the Ubuntu 22.04 server. Also, your FTP server is secured through the TLS/SSL connections and secured with the UFW firewall. Now you can add more FTP users for your client access.