How to Install ownCloud 9.1 with Nginx and MariaDB on CentOS 7
This tutorial exists for these OS versions
- CentOS 7.3
- CentOS 7
On this page
- Prerequisites
- Step 1 - Install Nginx and PHP7-FPM
- Step 2 - Configure PHP7-FPM
- Step 3 - Install and Configure MariaDB
- Step 4 - Generate a self-signed SSL Certificate
- Step 5 - Download OwnCloud
- Step 6 - Configure the OwnCloud Virtual Host in Nginx
- Step 7 - Configure SELinux and FirewallD
- Step 8 - The OwnCloud Installation Wizard
- Reference
OwnCloud is a server software for data synchronization and file sharing with an easy to use web-based frontend that is available under an open source license. OwnCloud can be installed on a Linux or Windows web server, is easy to configure and has a comprehensive online documentation. The native client is available for Windows, MacOS and Linux (Desktop Application). There is also a mobile app for Android and iOS.
In this tutorial, I will guide you to install and configure ownCloud 9.1 on a CentOS 7 server. I will show you how to configure ownCloud with Nginx and PHP 7 (as FPM) and MariaDB as the database system.
Prerequisites
- CentOS 7 Server
- Root Privleges
Step 1 - Install Nginx and PHP7-FPM
Before we start with the Nginx and php7-fpm installation, we have to add the EPEL repository which contains additional software that is not available from the CentOS base repository. Install EPEL with this yum command.
yum -y install epel-release
Now install Nginx from the Epel repository.
yum -y install nginx
Now we have to add another repository for php7-fpm. There are several repositories for PHP 7 available on the net, I will use the webtatic repository here.
Add the webtatic repository:
rpm -Uvh https://mirror.webtatic.com/yum/el7/webtatic-release.rpm
Next, install PHP7-FPM with some additional packages for the ownCloud installation.
yum -y install php70w-fpm php70w-cli php70w-gd php70w-mcrypt php70w-mysql php70w-pear php70w-xml php70w-mbstring php70w-pdo php70w-json
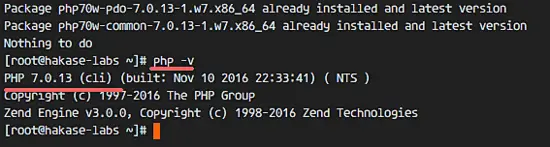
Check the PHP version from server terminal to ensure that the installation succeeded.
php -v
Step 2 - Configure PHP7-FPM
In this step, we will configure php-fpm to run with nginx. Php7-fpm will run under the user nginx and listen on port 9000.
Edit the default php7-fpm configuration with vim.
vim /etc/php-fpm.d/www.conf
In line 8 and 10, change user and group to 'nginx'.
user = nginx
group = nginx
In line 22, make sure php-fpm is running under server port 9000.
listen = 127.0.0.1:9000
Uncomment the lines 366-370 for the php-fpm system environment variables.
env[HOSTNAME] = $HOSTNAME
env[PATH] = /usr/local/bin:/usr/bin:/bin
env[TMP] = /tmp
env[TMPDIR] = /tmp
env[TEMP] = /tmp
Save the file and exit the editor
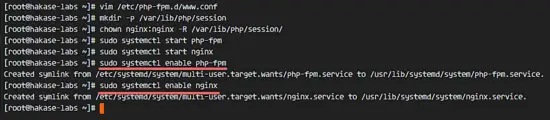
Next, create a new directory for the session path in the '/var/lib/' directory, and change the owner to the 'nginx' user.
mkdir -p /var/lib/php/session
chown nginx:nginx -R /var/lib/php/session/
Start php-fpm and nginx, then add it to start at boot time.
sudo systemctl start php-fpm
sudo systemctl start nginx
sudo systemctl enable php-fpm
sudo systemctl enable nginx
PHP7-FPM configuration is done.
Step 3 - Install and Configure MariaDB
OwnCloud supports PostgreSQL and MySQL databases, in this tutorial, we will use MariaDB for the ownCloud database. Install the mariadb-server package from the CentOS repository with the yum command.
yum -y install mariadb mariadb-server
Start the MariaDB service and configure the MariaDB root password.
systemctl start mariadb
mysql_secure_installation
Type in your root password when requested.
Set root password? [Y/n] Y
New password:
Re-enter new password:
Remove anonymous users? [Y/n] Y
Disallow root login remotely? [Y/n] Y
Remove test database and access to it? [Y/n] Y
Reload privilege tables now? [Y/n] Y
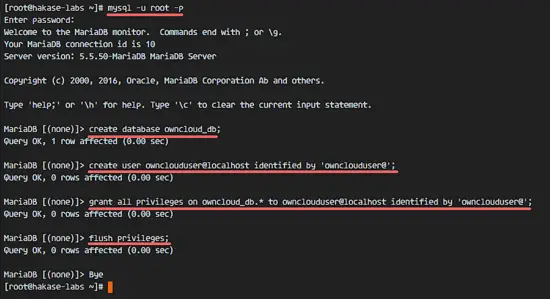
The MariaDB root password has been set, now we can login to the MySQL shell to create a new database and user for ownCloud.We will create new database '
We will create a new database 'owncloud_db' under the user 'ownclouduser' with password 'ownclouduser@'. Please chose a different and secure password for your installation!
mysql -u root -p
Type Password
Type the MySQL query below to create a new database and a new user.
create database owncloud_db;
create user ownclouduser@localhost identified by 'ownclouduser@';
grant all privileges on owncloud_db.* to ownclouduser@localhost identified by 'ownclouduser@';
flush privileges;
The 'owncloud_db database' with user 'ownclouduser' have been created.
Step 4 - Generate a self-signed SSL Certificate
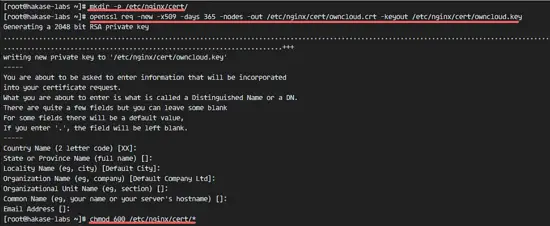
In this tutorial, we will run owncloud under a https connection for the client. You can use a free SSL cert such as let's encrypt. In this tutorial, I will create my own SSL certificate file with the OpenSSL command.
Create a new directory for the SSL file.
mkdir -p /etc/nginx/cert/
Then generate a new SSL certificate file with the OpenSSL command below.
openssl req -new -x509 -days 365 -nodes -out /etc/nginx/cert/owncloud.crt -keyout /etc/nginx/cert/owncloud.key
Enter the details for the SSL certificate as requested by the OpenSSL command. Then change the permission of all certificate files to 600 with chmod.
chmod 600 /etc/nginx/cert/*
Step 5 - Download OwnCloud
We will download ownCloud with the wget command, so we need to install the wget package first. Additionally, we need the package unzip.
yum -y install wget unzip
Go to the tmp directory and download the latest stable ownCloud 9.1 from the ownCloud site with wget.
cd /tmp
wget https://download.owncloud.org/community/owncloud-9.1.2.zip
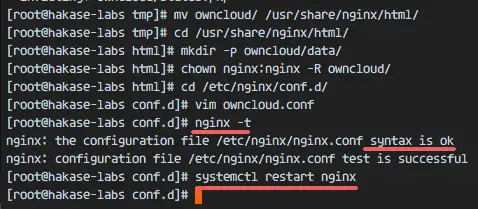
Extract the ownCloud zip file and move it to the '/usr/share/nginx/html/' directory.
unzip owncloud-9.1.2.zip
mv owncloud/ /usr/share/nginx/html/
Next, go to the nginx web root directory and create a new 'data' directory for owncloud.
cd /usr/share/nginx/html/
mkdir -p owncloud/data/
Change the owner of the 'owncloud' directory to the 'nginx' user and group.
chown nginx:nginx -R owncloud/
Step 6 - Configure the OwnCloud Virtual Host in Nginx
On step 5, we've downloaded the ownCloud source code and configured it to run under the Nginx web server. But we still need to configure the virtual host for ownCloud.
Create a new virtual host configuration file 'owncloud.conf' in the 'conf.d' directory.
cd /etc/nginx/conf.d/
vim owncloud.conf
Paste the ownCloud virtual host configuration below.
upstream php-handler {
server 127.0.0.1:9000;
#server unix:/var/run/php5-fpm.sock;
}
server {
listen 80;
server_name data.owncloud.co;
# enforce https
return 301 https://$server_name$request_uri;
}
server {
listen 443 ssl;
server_name data.owncloud.co;
ssl_certificate /etc/nginx/cert/owncloud.crt;
ssl_certificate_key /etc/nginx/cert/owncloud.key;
# Add headers to serve security related headers
# Before enabling Strict-Transport-Security headers please read into this topic first.
add_header Strict-Transport-Security "max-age=15552000; includeSubDomains";
add_header X-Content-Type-Options nosniff;
add_header X-Frame-Options "SAMEORIGIN";
add_header X-XSS-Protection "1; mode=block";
add_header X-Robots-Tag none;
add_header X-Download-Options noopen;
add_header X-Permitted-Cross-Domain-Policies none;
# Path to the root of your installation
root /usr/share/nginx/html/owncloud/;
location = /robots.txt {
allow all;
log_not_found off;
access_log off;
}
# The following 2 rules are only needed for the user_webfinger app.
# Uncomment it if you're planning to use this app.
#rewrite ^/.well-known/host-meta /public.php?service=host-meta last;
#rewrite ^/.well-known/host-meta.json /public.php?service=host-meta-json last;
location = /.well-known/carddav {
return 301 $scheme://$host/remote.php/dav;
}
location = /.well-known/caldav {
return 301 $scheme://$host/remote.php/dav;
}
location /.well-known/acme-challenge { }
# set max upload size
client_max_body_size 512M;
fastcgi_buffers 64 4K;
# Disable gzip to avoid the removal of the ETag header
gzip off;
# Uncomment if your server is build with the ngx_pagespeed module
# This module is currently not supported.
#pagespeed off;
error_page 403 /core/templates/403.php;
error_page 404 /core/templates/404.php;
location / {
rewrite ^ /index.php$uri;
}
location ~ ^/(?:build|tests|config|lib|3rdparty|templates|data)/ {
return 404;
}
location ~ ^/(?:\.|autotest|occ|issue|indie|db_|console) {
return 404;
}
location ~ ^/(?:index|remote|public|cron|core/ajax/update|status|ocs/v[12]|updater/.+|ocs-provider/.+|core/templates/40[34])\.php(?:$|/) {
fastcgi_split_path_info ^(.+\.php)(/.*)$;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param PATH_INFO $fastcgi_path_info;
fastcgi_param HTTPS on;
fastcgi_param modHeadersAvailable true; #Avoid sending the security headers twice
fastcgi_param front_controller_active true;
fastcgi_pass php-handler;
fastcgi_intercept_errors on;
fastcgi_request_buffering off;
}
location ~ ^/(?:updater|ocs-provider)(?:$|/) {
try_files $uri $uri/ =404;
index index.php;
}
# Adding the cache control header for js and css files
# Make sure it is BELOW the PHP block
location ~* \.(?:css|js)$ {
try_files $uri /index.php$uri$is_args$args;
add_header Cache-Control "public, max-age=7200";
# Add headers to serve security related headers (It is intended to have those duplicated to the ones above)
# Before enabling Strict-Transport-Security headers please read into this topic first.
#add_header Strict-Transport-Security "max-age=15552000; includeSubDomains";
add_header X-Content-Type-Options nosniff;
add_header X-Frame-Options "SAMEORIGIN";
add_header X-XSS-Protection "1; mode=block";
add_header X-Robots-Tag none;
add_header X-Download-Options noopen;
add_header X-Permitted-Cross-Domain-Policies none;
# Optional: Don't log access to assets
access_log off;
}
location ~* \.(?:svg|gif|png|html|ttf|woff|ico|jpg|jpeg)$ {
try_files $uri /index.php$uri$is_args$args;
# Optional: Don't log access to other assets
access_log off;
}
}
Save the file and exit the editor.
Finally, test the Nginx configuration and make sure there is no error, then restart the service.
nginx -t
systemctl restart nginx
Step 7 - Configure SELinux and FirewallD
In this tutorial, we will leave SELinux on in enforcing mode, so we need the SELinux management tools package to configure it.
Install SELinux management tools with this yum command.
yum -y install policycoreutils-python
Then execute the commands below as root to allow ownCloud to run under SELinux. Remember to change the ownCloud directory in case yu use a different directory for the ownCloud installation.
semanage fcontext -a -t httpd_sys_rw_content_t '/usr/share/nginx/html/owncloud/data(/.*)?'
semanage fcontext -a -t httpd_sys_rw_content_t '/usr/share/nginx/html/owncloud/config(/.*)?'
semanage fcontext -a -t httpd_sys_rw_content_t '/usr/share/nginx/html/owncloud/apps(/.*)?'
semanage fcontext -a -t httpd_sys_rw_content_t '/usr/share/nginx/html/owncloud/assets(/.*)?'
semanage fcontext -a -t httpd_sys_rw_content_t '/usr/share/nginx/html/owncloud/.htaccess'
semanage fcontext -a -t httpd_sys_rw_content_t '/usr/share/nginx/html/owncloud/.user.ini'
restorecon -Rv '/usr/share/nginx/html/owncloud/'
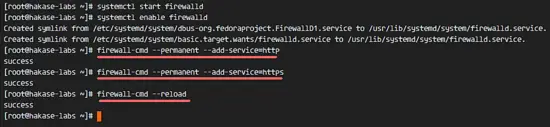
Next, enable the firewalld service and open the HTTP and HTTPS port for owncloud.
Start firewalld and configure it to start at boot time.
systemctl start firewalld
systemctl enable firewalld
Open the HTTP and HTTPS ports with the firewall-cmd command, then reload the firewall.
firewall-cmd --permanent --add-service=http
firewall-cmd --permanent --add-service=https
firewall-cmd --reload
The server configuration part is finished.
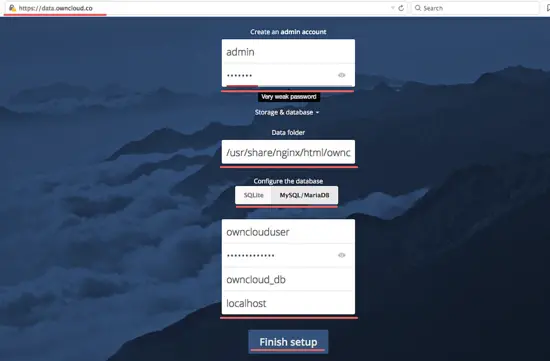
Step 8 - The OwnCloud Installation Wizard
Now open your web browser and type in the ownCloud domain name into the URL field, mine is: data.owncloud.co, and you will be redirected to the secure HTTPS connection.
Type in your new admin username and password, then type in the database credentials and click on 'Finish Setup'.
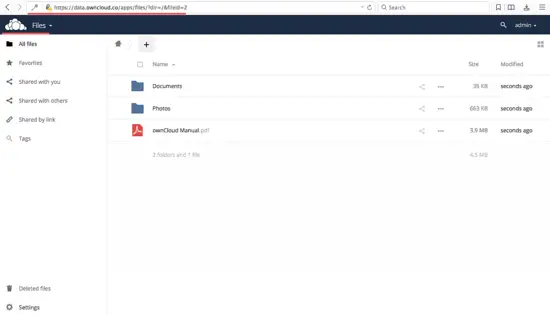
Admin Dashboard File Manager.
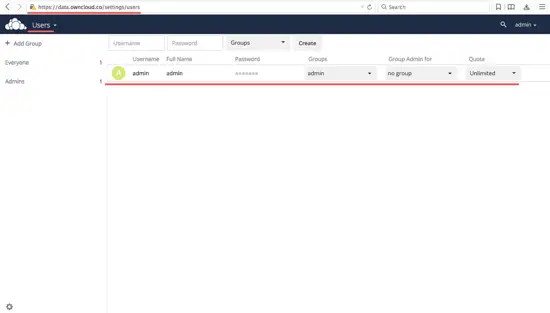
User Settings.
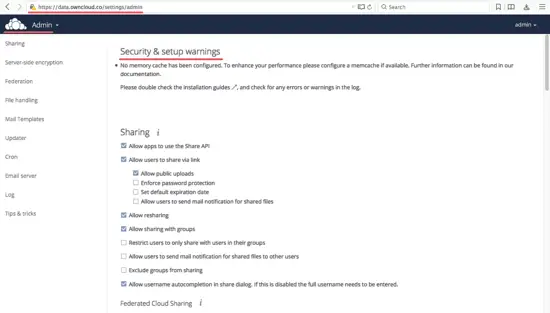
Admin Settings.
Owncloud has been successfully installed with Nginx, PHP7-FPM, and MariaDB on a CentOS 7 Server.