The Perfect Server - Fedora 9 - Page 2
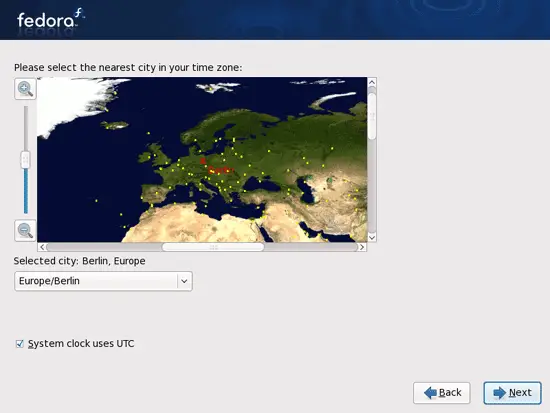
Choose your time zone:
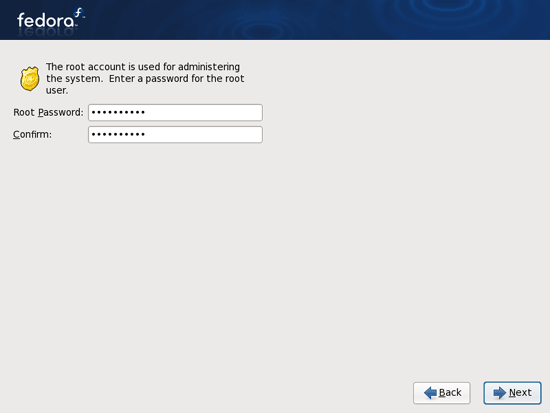
Give root a password:
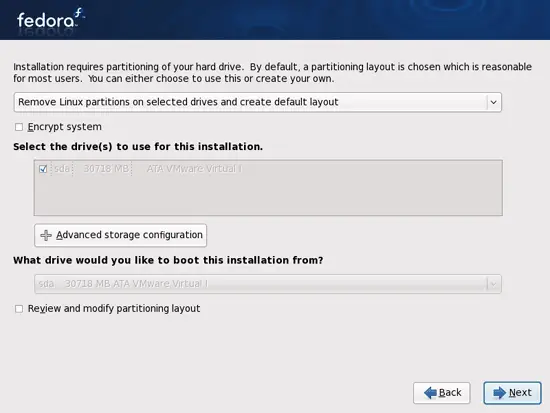
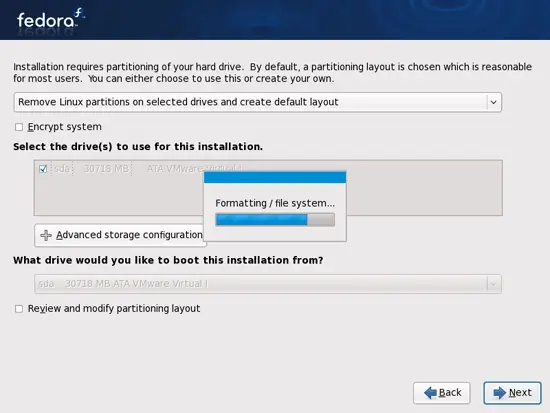
Next we do the partitioning. Select Remove Linux partitions on selected drives and create default layout. This will give you a small /boot partition and a large / partition which is fine for our purposes:
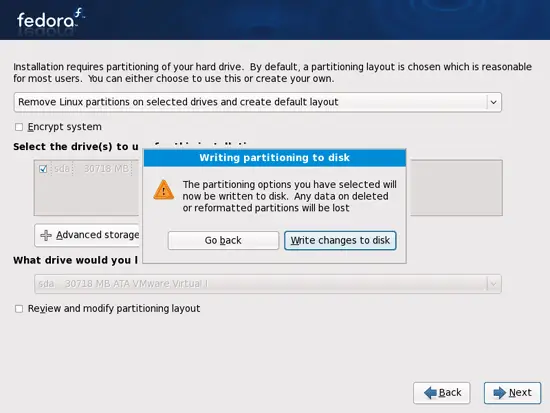
Select Write changes to disk:
The hard drive is being formatted:
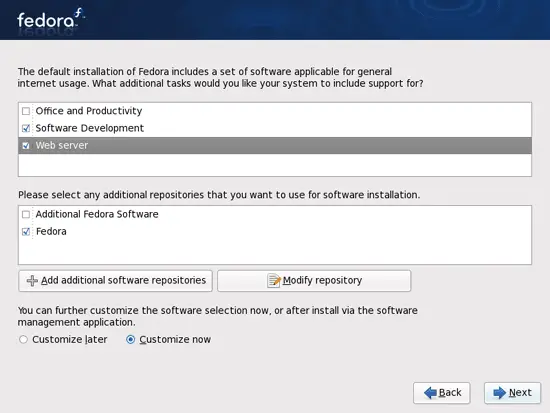
Now we select the software we want to install. Uncheck Office and Productivity and check Software Development and Web server instead. Then check Customize now, and click on Next:
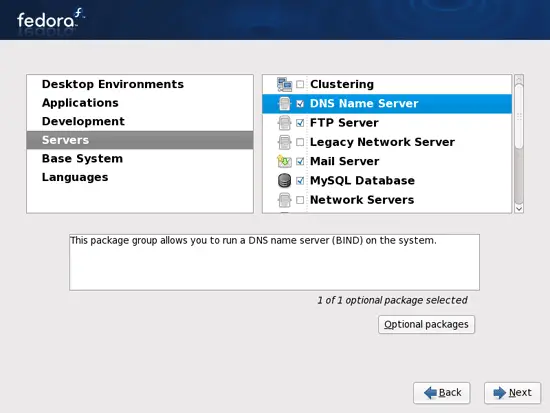
Now we must select the package groups we want to install. Select Editors, Text-based Internet, Development Libraries, Development Tools, DNS Name Server, FTP Server, Mail Server, MySQL Database, Server Configuration Tools, Web Server, Administration Tools, Base, Hardware Support, Java, System Tools (unselect all other package groups) and click on Next:
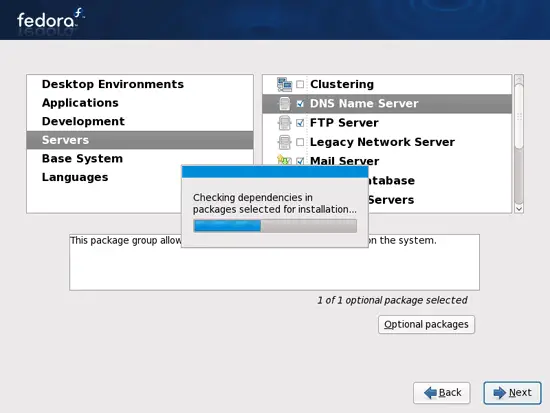
The installer checks the dependencies of the selected packages:
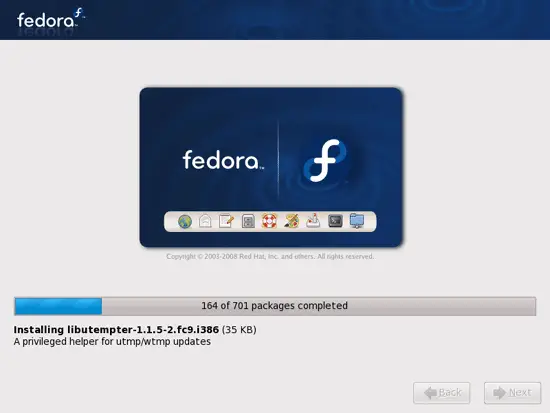
The installation begins. This will take a few minutes:
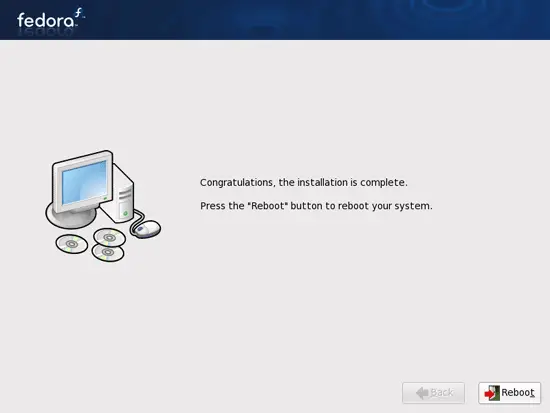
Finally, the installation is complete, and you can remove your DVD from the computer and reboot it:
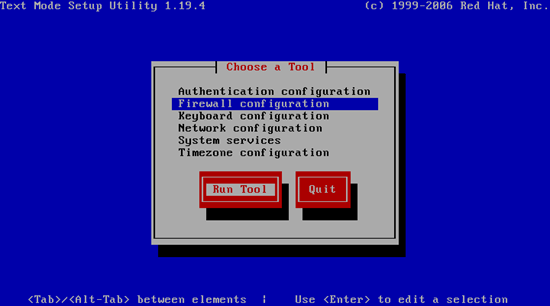
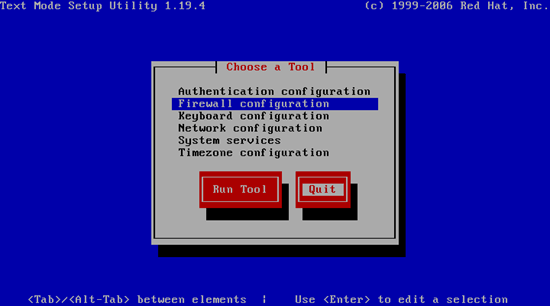
After the reboot, you will see this screen. Select Firewall configuration and hit Run Tool:
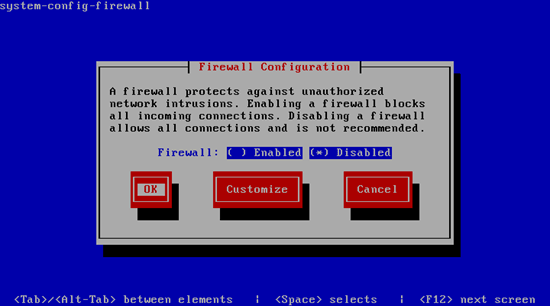
I want to install ISPConfig at the end of this tutorial which comes with its own firewall. That's why I disable the default Fedora firewall now. Of course, you are free to leave it on and configure it to your needs (but then you shouldn't use any other firewall later on as it will most probably interfere with the Fedora firewall).
Hit OK afterwards:
Then leave the Choose a Tool window by selecting Quit:
Now, on to the configuration...