How to Configure Path-Based routing in an AWS Application Load Balancer
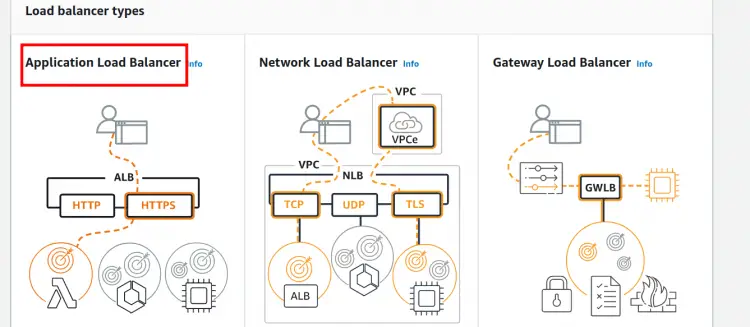
In AWS, ELB and Elastic Load Balancing exists a concept where the servers can be added or released as per the demand of our application and the incoming traffic from an application is distributed among multiple targets. These targets can be EC2 instances, containers, and IP addresses in one or several Availability Zones. Supported types of AWS Elastic Load Balancers are Application Load Balancers(ALB), Network Load Balancers(NLB), Gateway Load Balancers(recently launched), and Classic Load Balancers. These load balancers have different configurations, for e.g.,
1. Application Load Balancer: It works by automatically distributing the incoming application traffic between two or more EC2 instances. We can define routing rules as per the content of the request(content-based routing). It is a layer 7 load balancer.
2. Network Load Balancers: NLB uses IP protocol data (TCP and UDP) to route connections to AWS resources like EC2, microservices and containers. It is a layer 4 load balancer.
3. Gateway Load Balancer: These are used with third-party virtual appliances like NextGen firewalls(NGFW), IPS, IDS etc. running on EC2 instances. It works by placing a single gateway for traffic from multiple virtual appliances and these multiple virtual appliances can be scaled up or scaled down as per the demand. This is good for the stability of the network. It is a layer 3(Gateway) plus layer 4(Load Balancing) load balancer.
4. Classic Load Balancer: CLB is a legacy load balancer of AWS which is used for load balancing across multiple EC2 instances. It is recommended for applications designed within the EC2-Classic network. It is a layer 4/7 load balancer. It is recommended by AWS to avoid this load balancer.
Overview of this Guide
In this tutorial, we will configure path-based routing for an Application Load Balancer on AWS. We are going to use an IAM user account for this task. We have the following resources for this setup:
1. Two Availability Zones with each containing at least one EC2 instance.
2. A VPC having a minimum one public subnet in each of the above two Availability Zones. This public subnet will be used for configuring load balancer.
3. Install a web server on each instance and allow port 80 access on these instances using the security group.
Configuration of EC2 instances
For this guide we have configured two Amazon Linux EC2 instances with Apache Httpd webserver installed on both of them. On one server we have a ‘signin’ directory containing an index.html file with the contents: “Welcome User? Sign in to proceed...”
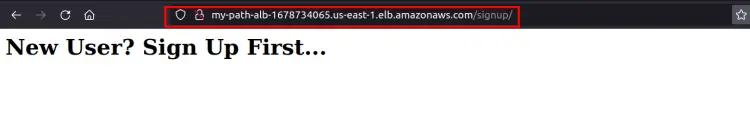
On another server we have a ‘signup’ directory containing an index.html file with the contents: “New User? Sign Up First...”
Both the ‘signin’ and ‘signup’ directories are inside the root directory(/var/www/html)
Configuring the Target group
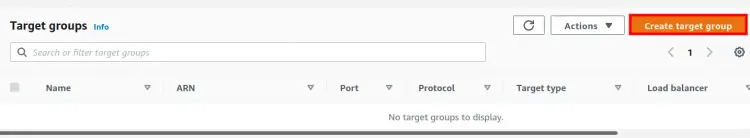
Step 1. For routing the request we will first create two target groups, one for each server. Open the EC2 console and on left side panel, find and select ‘Target Groups’ (It is under Load balancing).
Step 2. On the new page, click on the ‘Create target group’ button:
Step 3. We are now on the ‘Specify group details’ page. Under basic configuration, do the following:
- Choose a target type: Select ‘Instances’ here.
- Target group name: Give a suitable name to the target group(‘Sign-In’ in our case.)
- Protocol: HTTP
- Port: 80
- VPC: Select your VPC Name here.
- Protocol version: Keep the default selected.(HTTP1)
Under the ‘Health checks’ settings:
- Health check protocol: HTTP
- Health check path: ‘Path you want to use’(‘/signin’ in our case)
- Keep the ‘Advanced health check settings’ to default. Add tags if you need them(Optional). Click ‘Next’ to continue.
Registering EC2 Instances to the Target Groups
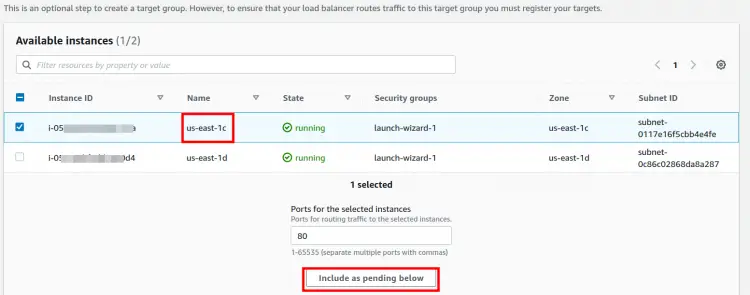
Step 1. Now add one of the EC2 instances to the above target groups. Select an instance and then click on ‘Include as pending below’ button
Step 2. The above-selected instance will appear under ‘Review targets’. Now click on ‘Create target group’.
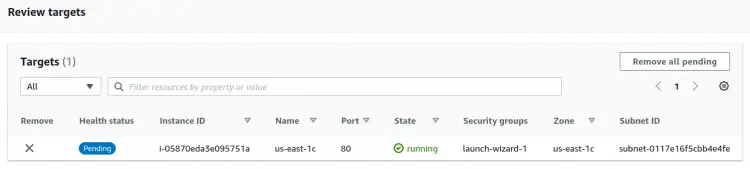
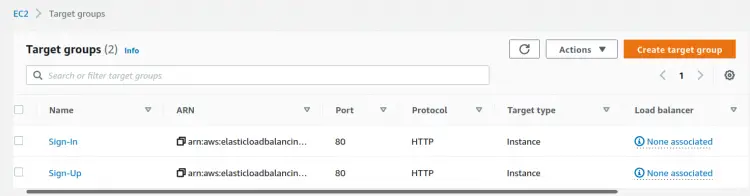
Step 3. On the next window again click ‘continue’. Now repeat the same procedure for another Target group and name it as ‘Sign-Up’. Use another instance( in another Availability zone) with this Target group and use a different Health check path(‘/signup’ in our case):
Creating the Application Load Balancer
Step 1. From the EC2 console, head to Load Balancers and click on Create Load Balancer button and then select ‘Application Load Balancer’ shown on the new page:
Step 2. Give a suitable name(here ‘My_Path_ALB’) to your load balancer. Keep the Scheme to default (‘Internet-facing’), Select IP address type as IPv4.
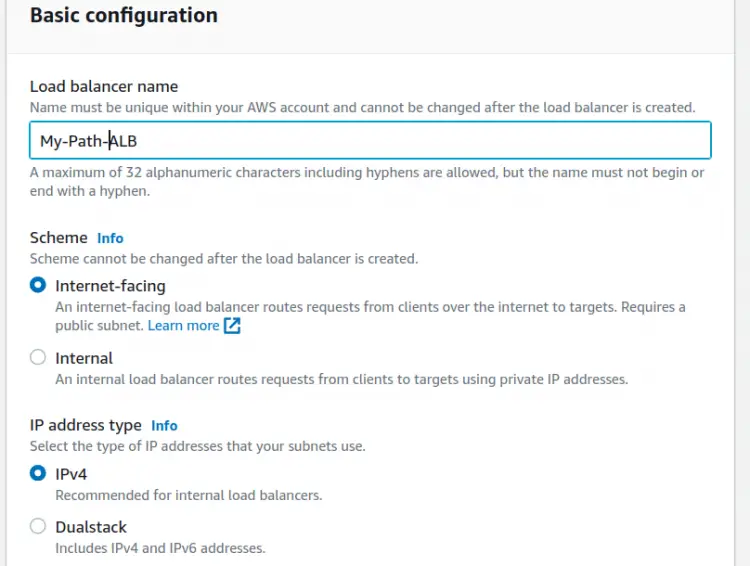
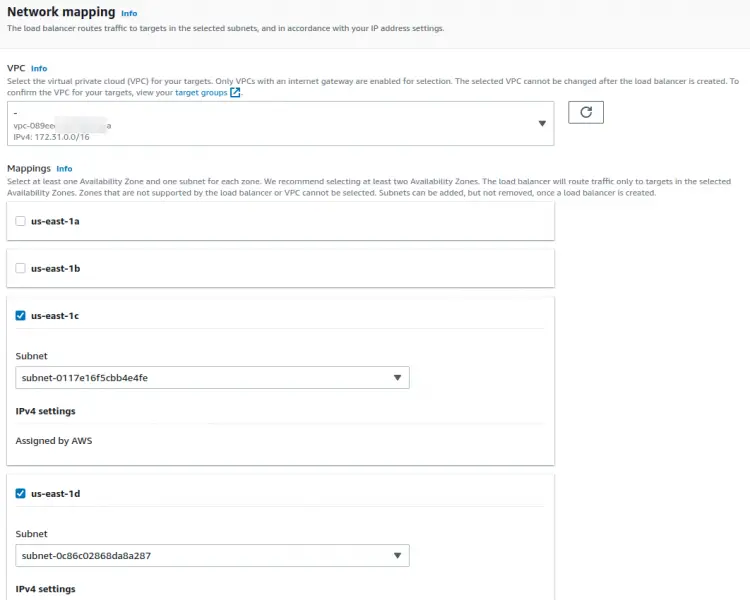
Step 3. Under the Network mapping section, select the target VPC and in the Mappings section, select the two Availability zones containing your targets to which load balancer will route the traffic.
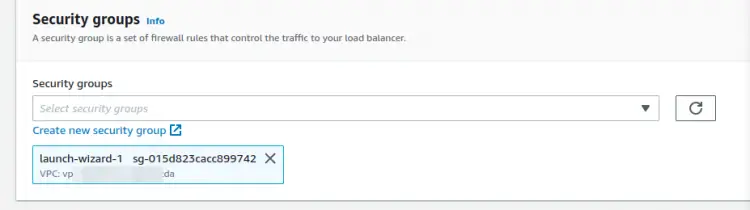
Step 4. Configure Security Groups for the load balancer and allow your target port (port 80 in our case) to listen on:
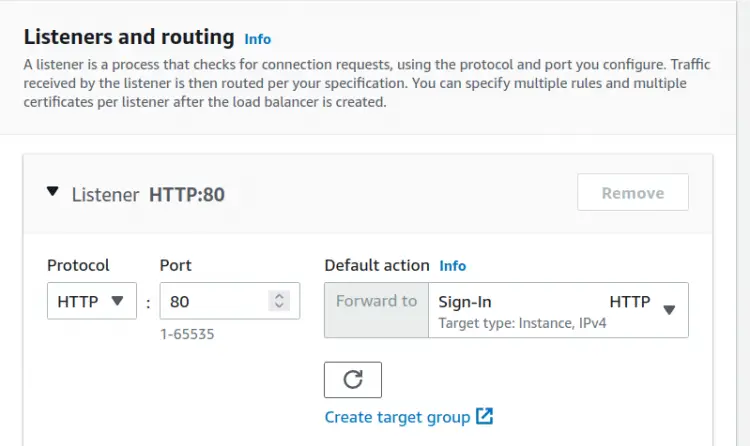
Step 5. Select a listener(HTTP in our case) and enter a port to listen on or choose to stick with the default port 80 for HTTP requests. Under the Default action, select ‘Sign-in’ target for ‘forward to’ column:
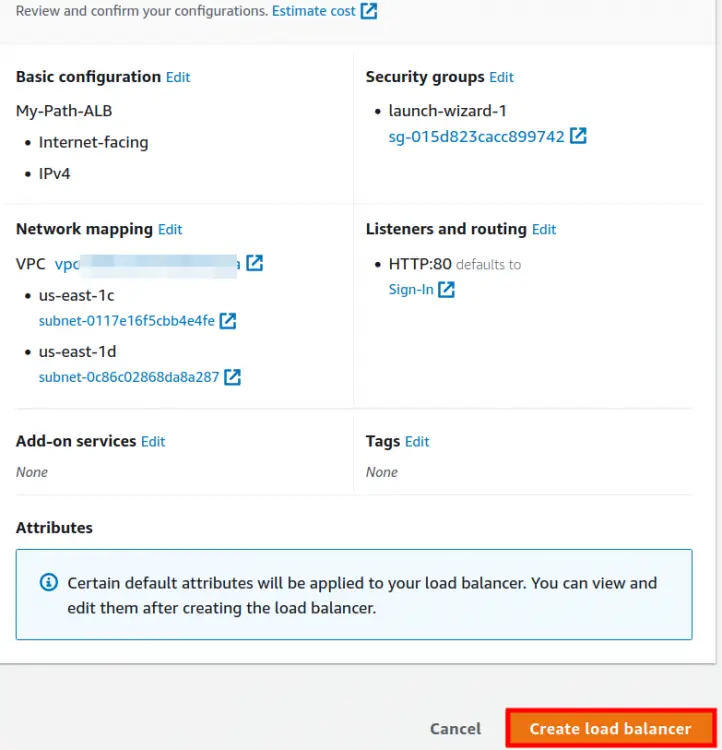
Step 6. Optional steps can be skipped. Now review the summary and hit the ‘Create load balancer’ button:
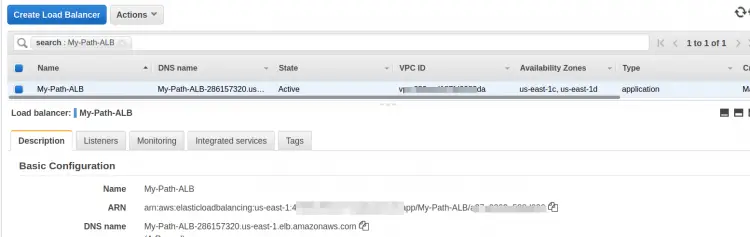
Step 7. Now again go to the ‘Load Balancers’ page and find your target load balancer here:
Adding Path Based Forwarding Rules
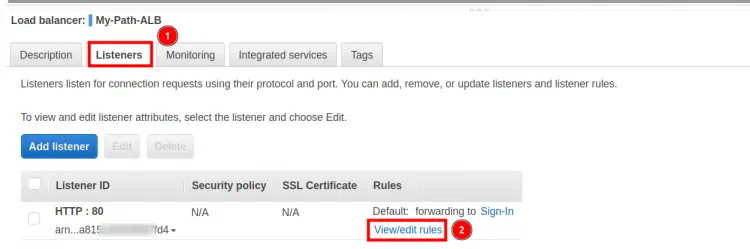
Step 1. Once the ALB status changes to Active, we will proceed with Forwarding Rules. Click on the Load Balancer name and then go to the Listeners tab.
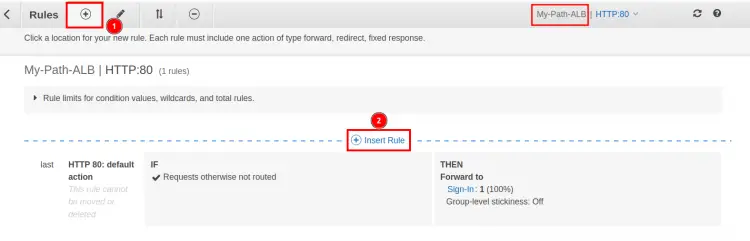
Step 2. Click on ‘View/Edit rules’ under ‘Rules’ column and then click on the ‘+’ symbol followed by ‘Insert Rule’:
Step 3. Under the ‘IF(all match) column, click on the ‘+ Add condition’ drop down arrow and select ‘Path’ as the Rule type and put ‘/signin*’ in the text field corresponding to ‘is’ label.
Step 4. From the ‘Then’ column, click on ‘+Add action’ drop down arrow and select ‘Forward to’ as the action. Here select the target group ‘Sign-In’.
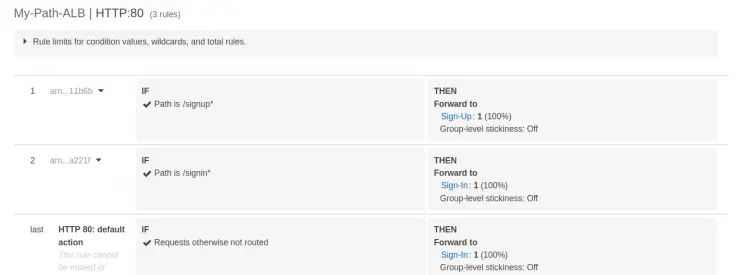
Repeat the steps 2 and 3 above for the target group ‘SignUp’ with path as ‘/signup*’. After saving the rules, we will have two rules:
Verifying the Setup…
To check if everything is working as expected, open a web browser and paste the DNS of the load balancer and append it with:
1) Path of Target group ‘Sign-Up’: '/signup'
2) Path of Target group ‘Sign-In’: '/signin'
Conclusion
Congratulations, we have finally configured a working scenario for path-based routing on AWS application load balancer.