Chrooting Apache2 With mod_chroot On OpenSUSE 11.2
Version 1.0
Author: Falko Timme  Follow me on Twitter
Follow me on Twitter
This guide explains how to set up mod_chroot with Apache2 on an OpenSUSE 11.2 system. With mod_chroot, you can run Apache2 in a secure chroot environment and make your server less vulnerable to break-in attempts that try to exploit vulnerabilities in Apache2 or your installed web applications.
I do not issue any guarantee that this will work for you!
1 Preliminary Note
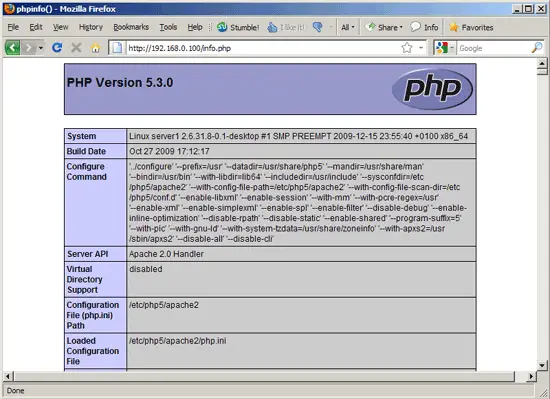
I'm assuming that you have a running OpenSUSE 11.2 system with a working Apache2, e.g. as shown in this tutorial: The Perfect Server - OpenSUSE 11.2 x86_64 [ISPConfig 2]. In addition to that I assume that you have one or more web sites set up within the /srv/www directory (e.g. if you use ISPConfig).
2 Installing mod_chroot
There's no mod_chroot package for OpenSUSE 11.2, therefore we must build it ourselves. First we install the prerequisites:
yast2 -i libgcc glibc-devel gcc flex lynx compat-readline4 db-devel wget gcc-c++ make vim
yast2 -i apache2-devel
Now we build mod_chroot as follows:
cd /tmp
wget http://core.segfault.pl/~hobbit/mod_chroot/dist/mod_chroot-0.5.tar.gz
tar xvfz mod_chroot-0.5.tar.gz
cd mod_chroot-0.5
apxs2 -cia mod_chroot.c
Then we restart Apache:
/etc/init.d/apache2 restart
3 Configuring Apache
I want to use the /srv/www directory as the directory containing the chroot jail. OpenSUSE's Apache uses the PID file /var/run/httpd2.pid; when Apache is chrooted to /srv/www, /var/run/httpd2.pid translates to /srv/www/var/run/httpd2.pid. Therefore we create that directory now:
mkdir -p /srv/www/var/run
chown -R root:www /srv/www/var/run
Now we must tell Apache that we want to use /srv/www as our chroot directory. We open /etc/apache2/httpd.conf, and right below the Include /etc/apache2/sysconfig.d/loadmodule.conf line, we add the line ChrootDir /srv/www; in the <Directory /> stanza, comment out the Options None line and add the line Options +FollowSymLinks:
vi /etc/apache2/httpd.conf
[...]
# generated from APACHE_MODULES in /etc/sysconfig/apache2
Include /etc/apache2/sysconfig.d/loadmodule.conf
ChrootDir /srv/www
[...]
# forbid access to the entire filesystem by default
<Directory />
#Options None
Options +FollowSymLinks
AllowOverride None
Order deny,allow
Deny from all
</Directory>
[...]
|
Next we must tell our vhosts that the document root has changed (for example, a DocumentRoot /srv/www translates now to DocumentRoot /). We can do this either by changing the DocumentRoot directive of each vhost, or more easier, by creating a symlink in the file system.
3.1 First Method: Changing The DocumentRoot
Let's assume we have a vhost with DocumentRoot /srv/www. We must now open the vhost configuration of that vhost and change DocumentRoot /srv/www to DocumentRoot /. Accordingly, DocumentRoot /srv/www/web1/web would now translate to DocumentRoot /web1/web, and so on. If you want to use this method, you must change the DocumentRoot for every single vhost.
3.2 Second Method: Creating A Symlink In the File System
This method is easier, because you have to do it only once and don't have to modify any vhost configuration. We create a symlink pointing from /srv/www/srv/www to /srv/www:
mkdir -p /srv/www/srv
cd /srv/www/srv
ln -s ../ www
Finally, we have to stop Apache, create a symlink from /var/run/httpd2.pid to /srv/www/var/run/httpd2.pid, and start it again:
/etc/init.d/apache2 stop
ln -sf /srv/www/var/run/httpd2.pid /var/run/httpd2.pid
/etc/init.d/apache2 start
That's it. You can now call your web pages as before, and they should be served without problems, as long as they are static HTML files or using mod_php.
If you are using CGI, e.g. Perl, suPHP, Ruby, etc., then you must copy the interpreter (e.g. /usr/bin/perl, /usr/sbin/suphp, etc.) to the chroot jail together with all libraries needed by the interpreter. You can find out about the required libraries with the ldd command, e.g.
ldd /usr/sbin/suphp
server2:/var/www/web1/log# ldd /usr/sbin/suphp
linux-gate.so.1 => (0xffffe000)
libstdc++.so.6 => /usr/lib/libstdc++.so.6 (0xb7e34000)
libm.so.6 => /lib/tls/i686/cmov/libm.so.6 (0xb7e0f000)
libgcc_s.so.1 => /lib/libgcc_s.so.1 (0xb7e03000)
libc.so.6 => /lib/tls/i686/cmov/libc.so.6 (0xb7cd2000)
/lib/ld-linux.so.2 (0xb7f23000)
server2:/var/www/web1/log#
If you've copied all required files, but the page still isn't working, you should take a look at the Apache error log. Usually it tells you where the problem is. Also read http://core.segfault.pl/~hobbit/mod_chroot/caveats.html for known problems and solutions.
4 Links
- mod_chroot: http://core.segfault.pl/~hobbit/mod_chroot/
- Apache: http://httpd.apache.org/
- OpenSUSE: http://www.opensuse.org/