Install and Configure FreeIPA Server on CentOS 8
FreeIPA is an open-source integrated Identity and Authentication solution for Linux and Unix based systems. It provides centralized authentication by storing data about user, groups, hosts, and other objects. It provides an integrated identity management service for Linux, Mac, and Windows. FreeIPA is based on the 389 Directory Server, Kerberos, SSSD, Dogtag, NTP, and DNS. It provides a web-based interface to manage Linux users and clients in your realm from the central location.
In this tutorial, we will show you how to install FreeIPA server on CentOS 8.
Prerequisites
- A server running CentOS 8.
- A root password is configured the server.
Setup Hostname
First, you will need to setup the fully qualified hostname in your system. You can set up it with the following command:
hostnamectl set-hostname freeipa.mydomain10.com
Next, edit the /etc/hosts file and add your server IP and hostname:
nano /etc/hosts
Add the following lines:
45.58.43.185 freeipa.mydomain10.com
Save and close the file when you are finished.
Install FreeIPA Server
By default, FreeIPA package is not available in the CentOS standard repository. So you will need to enable idm:DL1 repo in your system.
You can enable it with the following command:
dnf module enable idm:DL1
Next, sync the repository with the following command:
dnf distro-sync
Next, run the following command to install the FreeIPA server in your system.
dnf install ipa-server ipa-server-dns -y
Once the installation is completed, you can proceed to the next step.
Setup FreeIPA Server
Next, you will need to setup the FreeIPA server. You can set up it with the following command:
ipa-server-install
You will be asked to configure integrated DNS as shown below:
The log file for this installation can be found in /var/log/ipaserver-install.log ipa-server-install The log file for this installation can be found in /var/log/ipaserver-install.log ============================================================================== This program will set up the IPA Server. Version 4.8.4 This includes: * Configure a stand-alone CA (dogtag) for certificate management * Configure the NTP client (chronyd) * Create and configure an instance of Directory Server * Create and configure a Kerberos Key Distribution Center (KDC) * Configure Apache (httpd) * Configure the KDC to enable PKINIT To accept the default shown in brackets, press the Enter key. Do you want to configure integrated DNS (BIND)? [no]:
Press Enter to select no. You will be asked to provide hostname of your server:
Enter the fully qualified domain name of the computer on which you're setting up server software. Using the form. Example: master.example.com. Server host name [freeipa.mydomain10.com]:
Press Enter to select the default hostname. You will be asked to confirm your domain name as shown below:
The domain name has been determined based on the host name. Please confirm the domain name [mydomain10.com]:
Press Enter to select the default domain name. You will be asked to set Directory manager password as shown below:
The kerberos protocol requires a Realm name to be defined. This is typically the domain name converted to uppercase. Please provide a realm name [MYDOMAIN10.COM]: Certain directory server operations require an administrative user. This user is referred to as the Directory Manager and has full access to the Directory for system management tasks and will be added to the instance of directory server created for IPA. The password must be at least 8 characters long. Directory Manager password: Password (confirm):
Provide your desired password and hit Enter. You will be asked to set IPA admin password as shown below:
The IPA server requires an administrative user, named 'admin'. This user is a regular system account used for IPA server administration. IPA admin password: Password (confirm):
Provide your desired password and hit Enter. You will be asked to configure NTP server as shown below:
Do you want to configure chrony with NTP server or pool address? [no]:
Press Enter to select default option. You should get the following output:
The IPA Master Server will be configured with: Hostname: freeipa.mydomain10.com IP address(es): 45.58.43.185 Domain name: mydomain10.com Realm name: MYDOMAIN10.COM The CA will be configured with: Subject DN: CN=Certificate Authority,O=MYDOMAIN10.COM Subject base: O=MYDOMAIN10.COM Chaining: self-signed Continue to configure the system with these values? [no]: yes
Type yes and hit Enter to configure the system with above values. Once the setup is completed, you should get the following output:
SSSD enabled Configured /etc/openldap/ldap.conf Configured /etc/ssh/ssh_config Configured /etc/ssh/sshd_config Configuring mydomain10.com as NIS domain. Client configuration complete. The ipa-client-install command was successful unable to resolve host name freeipa.mydomain10.com. to IP address, ipa-ca DNS record will be incomplete unable to resolve host name freeipa.mydomain10.com. to IP address, ipa-ca DNS record will be incomplete Please add records in this file to your DNS system: /tmp/ipa.system.records._u0fzahd.db ============================================================================== Setup complete Next steps: 1. You must make sure these network ports are open: TCP Ports: * 80, 443: HTTP/HTTPS * 389, 636: LDAP/LDAPS * 88, 464: kerberos UDP Ports: * 88, 464: kerberos * 123: ntp 2. You can now obtain a kerberos ticket using the command: 'kinit admin' This ticket will allow you to use the IPA tools (e.g., ipa user-add) and the web user interface. Be sure to back up the CA certificates stored in /root/cacert.p12 These files are required to create replicas. The password for these files is the Directory Manager password The ipa-server-install command was successful
Once you are finished, you can proceed to the next step.
Configure Firewall and SELinux
If firewalld is installed in your system then you will need to allow some ports used by FreeIPA. You can allow them with the following command:
firewall-cmd --add-service={http,https,dns,ntp,freeipa-ldap,freeipa-ldaps} --permanent
Next, reload the firewalld with the following command to apply the changes:
firewall-cmd --reload
Next, you will also need to disbale the SELinux in your system.
You can disable the SELinux by editing /etc/selinux/config file:
nano /etc/selinux/config
Find the following line:
SELINUX=enforcing
And, replace it with the following line:
SELINUX=permissive
Save and close the file. Then, restart your system to apply the changes:
Access FreeIPA Web UI
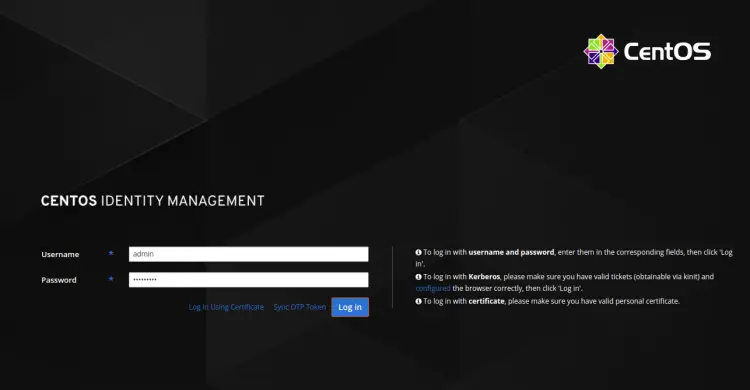
Now, open your web browser and access the FreeIPA web interface using the URL https://freeipa.mydomain10.com. You will be redirected to the FreeIPA login page as shown below:
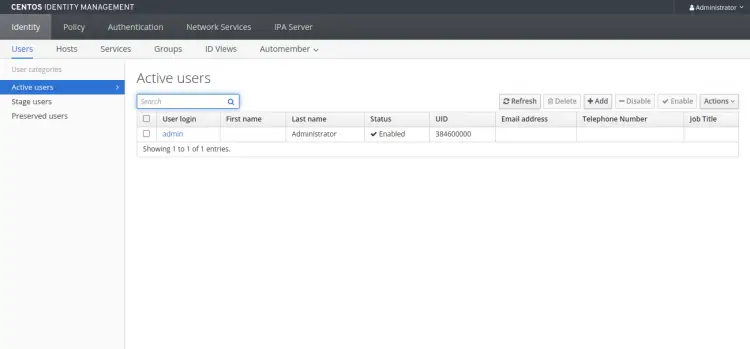
Provide your admin username, password and click on the Log in button. You should see the FreeIPA dashboard in the following page:
Working With FreeIPA CLI
FreeIPA also provides a command-line tool to add new user, group, service principal and grant write access to certain attributes from one group to another.
Before using the CLI tool, you will need to get a Kerberos ticket with the following command:
kinit admin
You will be asked to provide password as shown below:
Password for [email protected]:
Provide your admin password and hit Enter to get a Kerberos ticket.
Next, run the following command to check the ticket expiry:
klist
You should get the following output:
Ticket cache: KCM:0 Default principal: [email protected] Valid starting Expires Service principal 2020-09-28T03:36:54 2020-09-29T03:36:50 krbtgt/[email protected]
Next, add a new user account with the following command:
ipa user-add user1 --first=hit --last=jethva [email protected] --password
You should get the following output:
Password: Enter Password again to verify: ------------------ Added user "user1" ------------------ User login: user1 First name: hit Last name: jethva Full name: hit jethva Display name: hit jethva Initials: hj Home directory: /home/user1 GECOS: hit jethva Login shell: /bin/sh Principal name: [email protected] Principal alias: [email protected] User password expiration: 20200928073905Z Email address: [email protected] UID: 384600001 GID: 384600001 Password: True Member of groups: ipausers Kerberos keys available: True
You can also list all user accounts in your system with the following command:
ipa user-find
You should see the following output:
--------------- 2 users matched --------------- User login: admin Last name: Administrator Home directory: /home/admin Login shell: /bin/bash Principal alias: [email protected] UID: 384600000 GID: 384600000 Account disabled: False User login: user1 First name: hit Last name: jethva Home directory: /home/user1 Login shell: /bin/sh Principal name: [email protected] Principal alias: [email protected] Email address: [email protected] UID: 384600001 GID: 384600001 Account disabled: False ---------------------------- Number of entries returned 2
Conclusion
Congratulations! you have successfully installed and configured FreeIPA server on CentOS 8. You can now install FreeIPA client and add it to the FreeIPA server for Centralize Authentication. Feel free to ask me if you have any questions.