How to install Ansible AWX with Docker on CentOS 7
Ansible AWX is the OpenSource version of ansible tower. AWX provides a web-based user interface, REST API, and task engine built on top of Ansible. It is the upstream project for Tower, a commercial derivative of AWX.
In this tutorial, I will show you how to install and configure AWX using Docker.
I will be using 3 servers with centos 7 minimal installation and SELinux in permissive mode.
- 192.168.1.25 AWX Server
- 192.168.1.21 client1
- 192.168.1.22 client2
System Requirements for AWX Server
- At least 4GB of memory.
- At least 2 cpu cores.
- At least 20GB of space.
- Running Docker, Openshift, or Kubernetes.
Check the SELinux configuration.
sestatus
Result:
[root@awx ~]# sestatus SELinux status: enabled SELinuxfs mount: /sys/fs/selinux SELinux root directory: /etc/selinux Loaded policy name: targeted Current mode: permissive Mode from config file: permissive Policy MLS status: enabled Policy deny_unknown status: allowed Max kernel policy version: 28 [root@awx ~]#
Disable firewalld.
[root@awx installer]# systemctl stop firewalld [root@awx installer]# systemctl disable firewalld Removed symlink /etc/systemd/system/multi-user.target.wants/firewalld.service. Removed symlink /etc/systemd/system/dbus-org.fedoraproject.FirewallD1.service. [root@awx installer]#
Adding the host entries in /etc/hosts
[root@awx ~]# cat /etc/hosts 192.168.1.25 awx.sunil.cc awx 192.168.1.21 client1.sunil.cc client1 192.168.1.22 client2.sunil.cc client2 [root@awx ~]#
Enable epel repo.
[root@awx ~]# yum install -y epel-release
Install the packages.
[root@awx ~]# yum install -y yum-utils device-mapper-persistent-data lvm2 ansible git python-devel python-pip python-docker-py vim-enhanced
Configure docker ce stable repository.
[root@awx ~]# yum-config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo
Installing docker.
[root@awx ~]# yum install docker-ce -y
Start docker service.
[root@awx ~]# systemctl start docker
Enable docker service.
[root@awx ~]# systemctl enable docker
Cloning the AWX repo.
[root@awx ~]# git clone https://github.com/ansible/awx.git [root@awx ~]# cd awx/ [root@awx awx]# git clone https://github.com/ansible/awx-logos.git [root@awx awx]# pwd /root/awx [root@awx awx]#
Go into the installer directory within /root/awx.
[root@awx awx]# cd installer/
Edit the following parameters in inventory.
[root@awx awx]# vim inventory postgres_data_dir=/var/lib/pgdocker awx_official=true awx_alternate_dns_servers="4.2.2.1,4.2.2.2" project_data_dir=/var/lib/awx/projects
Your configuration should look like this.
[root@awx installer]# cat inventory |grep -v "#" localhost ansible_connection=local ansible_python_interpreter="/usr/bin/env python" [all:vars] dockerhub_base=ansible dockerhub_version=latest rabbitmq_version=3.6.14 awx_secret_key=awxsecret postgres_data_dir=/var/lib/pgdocker host_port=80 docker_compose_dir=/var/lib/awx pg_username=awx pg_password=awxpass pg_database=awx pg_port=5432 awx_official=true awx_alternate_dns_servers="4.2.2.1,4.2.2.2" project_data_dir=/var/lib/awx/projects [root@awx installer]#
Now deploying AWX via Docker.
[root@awx installer]# ansible-playbook -i inventory install.yml -vv
This will take a while depending upon the configuration of the server.
To check the deployment of ansible play for AWX run the below command.
[root@awx installer]# docker container ls CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES 318c7c95dcbb ansible/awx_task:latest "/tini -- /bin/sh -c." 12 minutes ago Up 12 minutes 8052/tcp awx_task 642c2f272e31 ansible/awx_web:latest "/tini -- /bin/sh -c." 12 minutes ago Up 12 minutes 0.0.0.0:80->8052/tcp awx_web 641b42ab536f memcached:alpine "docker-entrypoint.s." 18 minutes ago Up 18 minutes 11211/tcp memcached b333012d90ac rabbitmq:3 "docker-entrypoint.s." 19 minutes ago Up 19 minutes 4369/tcp, 5671-5672/tcp, 25672/tcp rabbitmq ada52935513a postgres:9.6 "docker-entrypoint.s." 19 minutes ago Up 19 minutes 5432/tcp postgres [root@awx installer]#
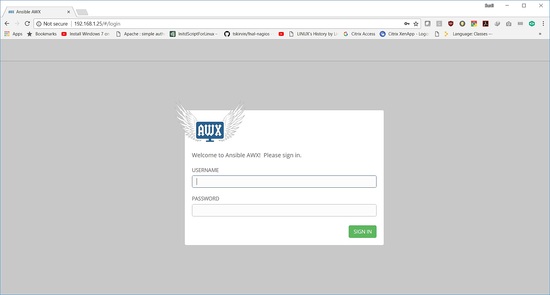
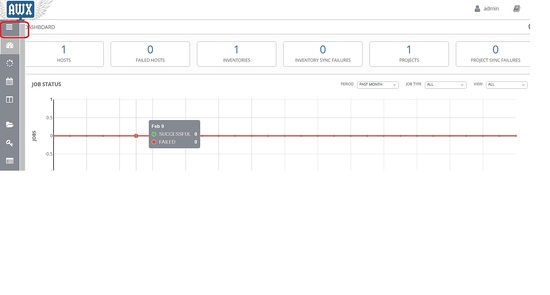
AWX is ready and can be accessed from the browser.
username is "admin" and the password is "password".
Configure passwordless login from AWX server
Create a user on all 3 hosts. Follow the steps below on all 3 servers.
[root@awx ~]# useradd ansible [root@client1 ~]# useradd ansible [root@clien2 ~]# useradd ansible
Generating ssh key:
[root@awx ~]# su - ansible [ansible@awx ~]$ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/home/ansible/.ssh/id_rsa): Created directory '/home/ansible/.ssh'. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/ansible/.ssh/id_rsa. Your public key has been saved in /home/ansible/.ssh/id_rsa.pub. The key fingerprint is: SHA256:j30gyTVQxcWIocdKMbVieZvfJzGkCjXhjtc5qu+fE8o [email protected] The key's randomart image is: +---[RSA 2048]----+ | +o==.+. | | O.oo . | | * @ . | | + @ * + | | S * = o | | B =.o o | | ..=.o.o .| | .E... o | | .oo.o. | +----[SHA256]-----+ [ansible@awx ~]$
Adding the sudoers entry on all 3 servers as a last entry to the file.
[root@awx ~]# visudo ansible ALL=(ALL) NOPASSWD: ALL
Copy the content of id_rsa.pub to authorized_keys on all the 3 servers.
[ansible@awx .ssh]$ cat id_rsa.pub ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC4QmuzjVnGUnT1o6xGXD3DCDPUMiTf0xUkOU4kYrkpxHYZ1nWG1MBNGWChyWobnTKYDh4c80+ftSyPHAdeV6KOwADOu6MXvMXHMK3EDe4jn+R0ZArQTEF2qKSBgve23wQu5IoqdWjvBoIEGqxw3LkYbdGxZ5dqKlP5ePkRKal4TncV+tlhueDaKz8QfvXgz+y2jc3HMWAH6a7UYsDKutDttmDDVUwfMcvoS9j2VYOUHkTCenx/2Y3296ULmWCREW9e6fTXLmOowIBDAar01CThmAzYCnBDNAFOsolh9dL1CKwLCvOyK1UBgJlfrzdGI/+fS7aFiaqhXpt6hI4xndJf [email protected] [ansible@awx .ssh]$ pwd /home/ansible/.ssh [ansible@awx ~]$ cat .ssh/authorized_keys ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC4QmuzjVnGUnT1o6xGXD3DCDPUMiTf0xUkOU4kYrkpxHYZ1nWG1MBNGWChyWobnTKYDh4c80+ftSyPHAdeV6KOwADOu6MXvMXHMK3EDe4jn+R0ZArQTEF2qKSBgve23wQu5IoqdWjvBoIEGqxw3LkYbdGxZ5dqKlP5ePkRKal4TncV+tlhueDaKz8QfvXgz+y2jc3HMWAH6a7UYsDKutDttmDDVUwfMcvoS9j2VYOUHkTCenx/2Y3296ULmWCREW9e6fTXLmOowIBDAar01CThmAzYCnBDNAFOsolh9dL1CKwLCvOyK1UBgJlfrzdGI/+fS7aFiaqhXpt6hI4xndJf [email protected] [ansible@awx ~]$chmod 600 .ssh/authorized_keys
client1
[root@client1 ~]# su - ansible [ansible@client1 ~]$ ls [ansible@client1 ~]$ mkdir .ssh [ansible@client1 ~]$ cat .ssh/authorized_keys ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC4QmuzjVnGUnT1o6xGXD3DCDPUMiTf0xUkOU4kYrkpxHYZ1nWG1MBNGWChyWobnTKYDh4c80+ftSyPHAdeV6KOwADOu6MXvMXHMK3EDe4jn+R0ZArQTEF2qKSBgve23wQu5IoqdWjvBoIEGqxw3LkYbdGxZ5dqKlP5ePkRKal4TncV+tlhueDaKz8QfvXgz+y2jc3HMWAH6a7UYsDKutDttmDDVUwfMcvoS9j2VYOUHkTCenx/2Y3296ULmWCREW9e6fTXLmOowIBDAar01CThmAzYCnBDNAFOsolh9dL1CKwLCvOyK1UBgJlfrzdGI/+fS7aFiaqhXpt6hI4xndJf [email protected] [ansible@client1 ~]$ chmod 700 .ssh [ansible@client1 ~]$ chmod 600 .ssh/authorized_keys
client2
[root@client2 ~]# su - ansible [ansible@client2 ~]$ ls [ansible@client2 ~]$ mkdir .ssh [ansible@client2 ~]$ cat .ssh/authorized_keys ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQC4QmuzjVnGUnT1o6xGXD3DCDPUMiTf0xUkOU4kYrkpxHYZ1nWG1MBNGWChyWobnTKYDh4c80+ftSyPHAdeV6KOwADOu6MXvMXHMK3EDe4jn+R0ZArQTEF2qKSBgve23wQu5IoqdWjvBoIEGqxw3LkYbdGxZ5dqKlP5ePkRKal4TncV+tlhueDaKz8QfvXgz+y2jc3HMWAH6a7UYsDKutDttmDDVUwfMcvoS9j2VYOUHkTCenx/2Y3296ULmWCREW9e6fTXLmOowIBDAar01CThmAzYCnBDNAFOsolh9dL1CKwLCvOyK1UBgJlfrzdGI/+fS7aFiaqhXpt6hI4xndJf [email protected] [ansible@client2 ~]$ chmod 700 .ssh [ansible@client2 ~]$ chmod 600 .ssh/authorized_keys
Validating the keyless login:
[ansible@awx .ssh]$ ssh client1 The authenticity of host 'client1 (192.168.1.21)' can't be established. ECDSA key fingerprint is SHA256:TUQNYdF4nxofGwFO7/z+Y5dUETVEI0xPQL4n1cUcoCI. ECDSA key fingerprint is MD5:5d:73:1f:64:0e:03:ac:a7:7b:33:76:08:6d:09:90:26. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added 'client1,192.168.1.21' (ECDSA) to the list of known hosts. Last login: Sun Mar 4 13:39:33 2018 [ansible@client1 ~]$ exit logout Connection to client1 closed. [ansible@awx .ssh]$ [ansible@awx .ssh]$ ssh client2 The authenticity of host 'client2 (192.168.1.22)' can't be established. ECDSA key fingerprint is SHA256:7JoWzteeQBwzc4Q3GGN+Oa4keUPMca/jtqv7gmmEZxg. ECDSA key fingerprint is MD5:85:77:3a:a3:07:31:d4:c1:41:ed:30:db:74:b4:ce:67. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added 'client2,192.168.1.22' (ECDSA) to the list of known hosts. Last login: Sun Mar 4 13:51:27 2018 [ansible@client2 ~]$ exit logout Connection to client2 closed. [ansible@awx .ssh]$
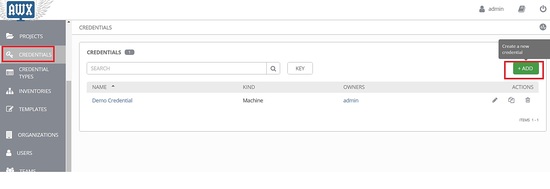
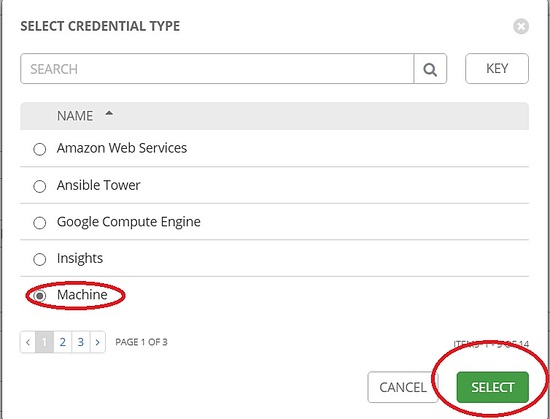
Now click on this icon and go to credentials -> add
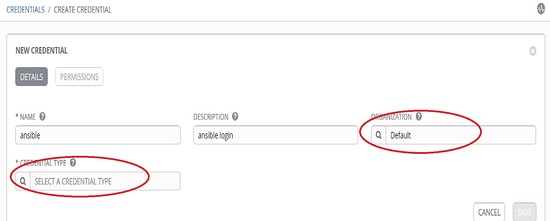
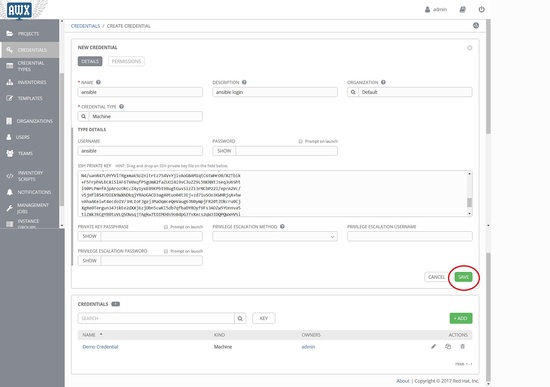
Choose an organization and fill in the username and description.
Here the username is "ansible"
Choose 'machine' under credential type and fill the details.
Get the private key from AWX server.
[ansible@awx .ssh]$ pwd /home/ansible/.ssh [ansible@awx .ssh]$ cat id_rsa id_rsa id_rsa.pub [ansible@awx .ssh]$ cat id_rsa -----BEGIN RSA PRIVATE KEY----- MIIEpAIBAAKCAQEAuEJrs41ZxlJ09aOsRlw9wwgz1DIk39MVJDlOJGK5KcR2GdZ1 htTATRlgoclqG50ymA4eHPNPn7UsjxwHXleijsAAzrujF7zFxzCtxA3uI5/kdGQK 0ExBdqikgYL3tt8ELuSKKnVo7waCBBqscNy5GG3RsWeXaipT+Xj5ESmpeE53FfrZ Ybng2is/EH714M/sto3NxzFgB+mu1GLAyrrQ7bZgw1VMHzHL6EvY9lWDlB5Ewnp8 f9mN9velC5lgkRFvXun01y5jqMCAQwGq9NQk4ZgM2ApwQzQBTrKJYfXS9QisCwrz sitVAYCZX683RiP/n0u2hYmqoV6beoSOMZ3SXwIDAQABAoIBAQCcfiUU6S9fJfca DTmqxHrcIyJJzZDN3GvvSRBaDNLwa2BWz3Mf4Z+1m6Ebp4IME/W9ePgQZIGyxeAj Z43Gja2Nifrlmi2JYpWjeG+MvLwN26XfSHx6rtlGmzKkoIQc98qIvSevqepGYAOa 0sC0VnKKEfNvtei+jVam4hy/e9/oQWHV8c/yueLWpCx2pWOy5m7WVLdwNQSK+8pu sxHLFTNCSC9wddBN80FVxhJQ7L4D2DzcprhcfUz6Uz7Ju7v8MtSksirDnaGliWJ3 NvxhntJYKvgQ30pvBr//y0lYnAB+O0jJhOpHlgD2hNSlI8sgUxmVyl+gC9Dhnq+v 1uKm3CThAoGBAOx+YIGGT/ymqJ53k8Dj4keKctI4+E3p/7Tr2jEyRff177VUjITQ UnrRTw1W+XSE5cszitVYbv0WUwTJoSSrKaRaVG7iORaqcv0LkG8gnlcrcifRXSl5 5xMsPCw0adwtoyhrHQLbENntMl+iQw2JbE6fvldvNe2kPdL3B2T7Jw1RAoGBAMd1 GvsOHLaKtTD0me+wgGnql0GIp90elE7rQ1p6VMxZkE68b+0jX9xHAt2zxocR84+L Gi6uAZvBqnwmH48c7Do6/oulrJXH2OcT6S8+F/kM7PWNT0Z0J0MW/+npVoPwSihZ N4/uanR47L0YYVlTRgxmakSUZnitrEz754V+YjivAoGBAM1qtC6tWHrO0/XZTbik +F5FrphVLbCXiSlAF6TV0xqfP5gUmX2faZUOi4i9vC3uZZ9L5NKNXtJseq3U6Sht l90PLPmnfAjpArozOkCcZ4y1yxE09KPbI9BugtGusSizZ13rNCbP22I/eprA2Vc/ v5jHflB547DIEX9WXNDkqjYRAoGACD3ag40tuo04t3Ej+zd71uSOo3KWHRjqX+hw vAhaAKeiwt4ecdoIV/3HLIoFJgej3MaOqmceQeVaug6JN0ympjFR20tZOkcru0Cj XgRe0Tergun34J1kEe2dXXj6zjDbn5cwKI5db7qfbaDYROyf9Fs3AOZw5YOnnva5 tlZmkJkCgYB0tuVLQSOWsqjTAgkw7tDIMOds9o8dpGJTvXxcs2qWJIDQPQWxHVSl Qimh5DFBkrNDAYKKC386KaZOEKwG7G1YuGbh1+ns3piscJaBi2lPaeA1Y/QA6pCT t9Hbdzre5x0gDbKSHOk+QLJkVdfQX9jamRE6W0k0pXVF6ur8N5zfxA== -----END RSA PRIVATE KEY----- [ansible@awx .ssh]$
Private key (example).
-----BEGIN RSA PRIVATE KEY----- MIIEpAIBAAKCAQEAuEJrs41ZxlJ09aOsRlw9wwgz1DIk39MVJDlOJGK5KcR2GdZ1 htTATRlgoclqG50ymA4eHPNPn7UsjxwHXleijsAAzrujF7zFxzCtxA3uI5/kdGQK 0ExBdqikgYL3tt8ELuSKKnVo7waCBBqscNy5GG3RsWeXaipT+Xj5ESmpeE53FfrZ Ybng2is/EH714M/sto3NxzFgB+mu1GLAyrrQ7bZgw1VMHzHL6EvY9lWDlB5Ewnp8 f9mN9velC5lgkRFvXun01y5jqMCAQwGq9NQk4ZgM2ApwQzQBTrKJYfXS9QisCwrz sitVAYCZX683RiP/n0u2hYmqoV6beoSOMZ3SXwIDAQABAoIBAQCcfiUU6S9fJfca DTmqxHrcIyJJzZDN3GvvSRBaDNLwa2BWz3Mf4Z+1m6Ebp4IME/W9ePgQZIGyxeAj Z43Gja2Nifrlmi2JYpWjeG+MvLwN26XfSHx6rtlGmzKkoIQc98qIvSevqepGYAOa 0sC0VnKKEfNvtei+jVam4hy/e9/oQWHV8c/yueLWpCx2pWOy5m7WVLdwNQSK+8pu sxHLFTNCSC9wddBN80FVxhJQ7L4D2DzcprhcfUz6Uz7Ju7v8MtSksirDnaGliWJ3 NvxhntJYKvgQ30pvBr//y0lYnAB+O0jJhOpHlgD2hNSlI8sgUxmVyl+gC9Dhnq+v 1uKm3CThAoGBAOx+YIGGT/ymqJ53k8Dj4keKctI4+E3p/7Tr2jEyRff177VUjITQ UnrRTw1W+XSE5cszitVYbv0WUwTJoSSrKaRaVG7iORaqcv0LkG8gnlcrcifRXSl5 5xMsPCw0adwtoyhrHQLbENntMl+iQw2JbE6fvldvNe2kPdL3B2T7Jw1RAoGBAMd1 GvsOHLaKtTD0me+wgGnql0GIp90elE7rQ1p6VMxZkE68b+0jX9xHAt2zxocR84+L Gi6uAZvBqnwmH48c7Do6/oulrJXH2OcT6S8+F/kM7PWNT0Z0J0MW/+npVoPwSihZ N4/uanR47L0YYVlTRgxmakSUZnitrEz754V+YjivAoGBAM1qtC6tWHrO0/XZTbik +F5FrphVLbCXiSlAF6TV0xqfP5gUmX2faZUOi4i9vC3uZZ9L5NKNXtJseq3U6Sht l90PLPmnfAjpArozOkCcZ4y1yxE09KPbI9BugtGusSizZ13rNCbP22I/eprA2Vc/ v5jHflB547DIEX9WXNDkqjYRAoGACD3ag40tuo04t3Ej+zd71uSOo3KWHRjqX+hw vAhaAKeiwt4ecdoIV/3HLIoFJgej3MaOqmceQeVaug6JN0ympjFR20tZOkcru0Cj XgRe0Tergun34J1kEe2dXXj6zjDbn5cwKI5db7qfbaDYROyf9Fs3AOZw5YOnnva5 tlZmkJkCgYB0tuVLQSOWsqjTAgkw7tDIMOds9o8dpGJTvXxcs2qWJIDQPQWxHVSl Qimh5DFBkrNDAYKKC386KaZOEKwG7G1YuGbh1+ns3piscJaBi2lPaeA1Y/QA6pCT t9Hbdzre5x0gDbKSHOk+QLJkVdfQX9jamRE6W0k0pXVF6ur8N5zfxA== -----END RSA PRIVATE KEY-----
Copy the private key under ssh private key and click on save.
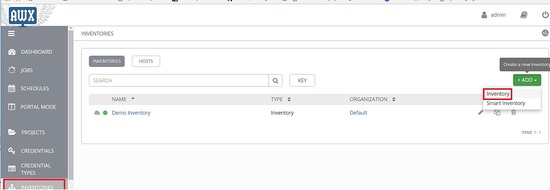
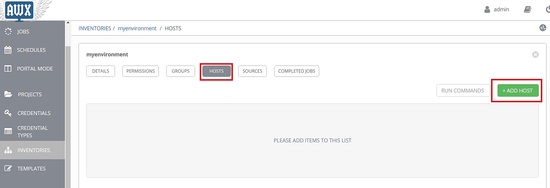
Click on Inventories and click on add inventory.
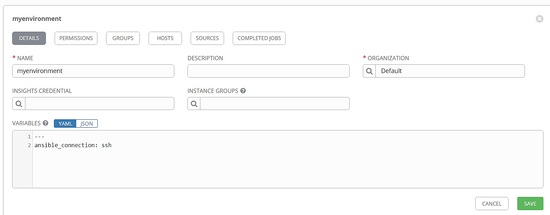
Fill the details accordingly.
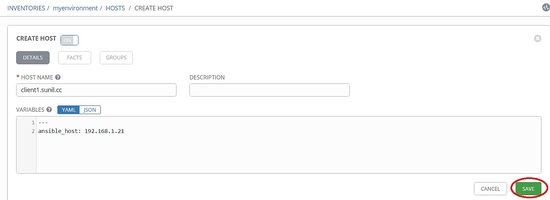
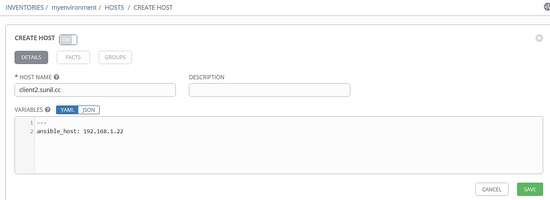
Click on hosts -> add host.
Add the below details:
Add the below details for client2.
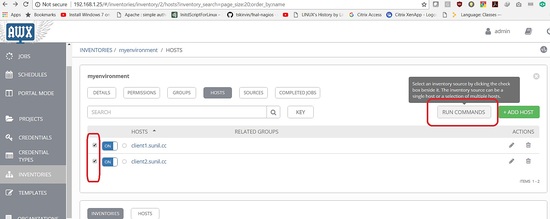
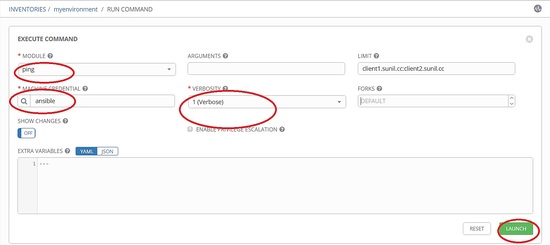
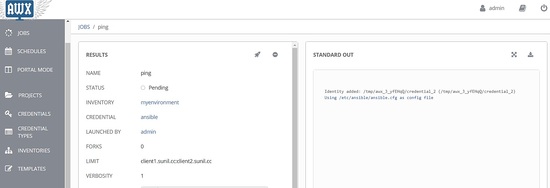
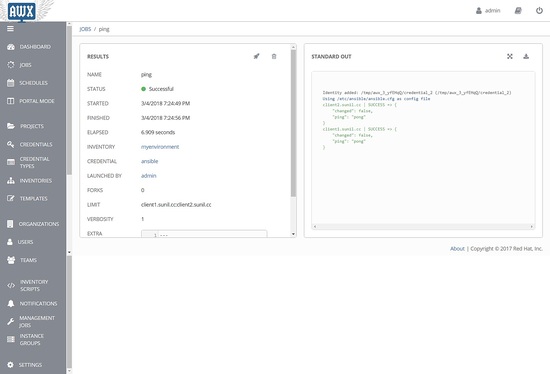
Test the connectivity via AWX.
Select both the hosts and click on run commands.
Choose ping and other details and click on Launch.
That's it for this tutorial. I will show you in the next tutorial how to install AWX via rpm and also how to run playbooks, doing API calls in further tutorials.