How to Install Observium Network Monitoring Tool on Debian 11
This tutorial exists for these OS versions
- Debian 11 (Bullseye)
- Debian 9 (Stretch)
- Debian 9 (Stretch)
On this page
Observium is a network monitoring tool for your server infrastructure. It's an auto-discovering network monitoring platform with low maintenance and supports a wide range of network devices and platforms, which includes Cisco, Linux, Windows, HP, Juniper, Dell, FreeBSD, Netscalar, NetApp, and many more.
Observium is available in multiple versions, the free version, the professional version, and the enterprise version. For the home lab, the Observium free version is more than enough for monitoring your network devices.
Observium also provides an intuitive user interface that allows you easily to get the status of your networking devices. And also provides external integration with a third-party application that allows you to create a custom module to collect and report data from your application.
In this tutorial, you will set up the Observium Network Monitoring Tool on Debian 11 server. With this guide, you will run the Observium under the LAMP Stack (Linux, Apache2, MariaDB, and PHP). By the end of the tutorial, you'll have the Observium network Monitoring running and you're ready to add the host or network devices that you will monitor.
Prerequisites
To complete this tutorial, you will need the following requirements:
- A Debian 11 server - This example uses the latest version of Debian Bulleye with the hostname 'observium-server'.
- A non-root user with sudo/root administrator privileges.
Installing Dependencies
Observium is a Network Monitoring Tool mainly written in PHP. To install Observium, you must install package dependencies such as Apache2 web server, MariaDB database server, and PHP packages, and some network utilities such as whois, rrdtool, mtr, and many more.
In the first step, you will install some package dependencies that include the LAMP Stack and some networking tools to the Debian system.
Run the following apt command to update and refresh your Debian package index.
sudo apt update
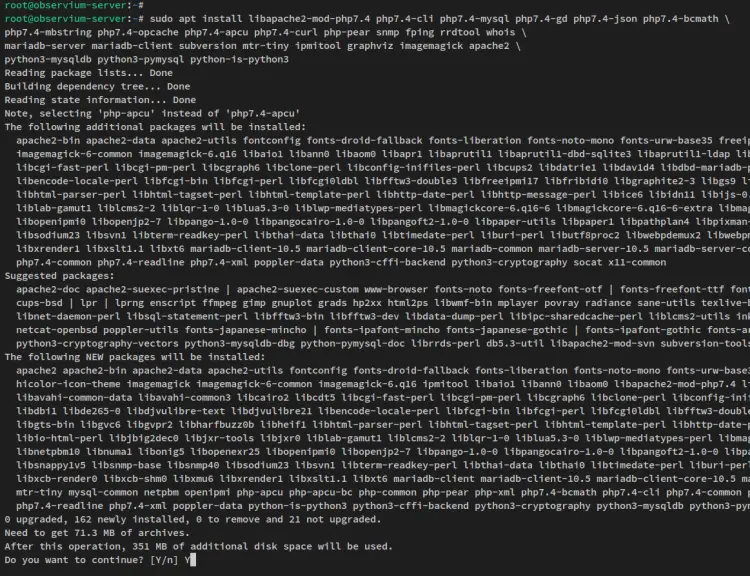
Now install package dependencies for Observium via the following apt command.
sudo apt install libapache2-mod-php7.4 php7.4-cli php7.4-mysql php7.4-gd php7.4-json php7.4-bcmath \
php7.4-mbstring php7.4-opcache php7.4-apcu php7.4-curl php-pear snmp fping rrdtool whois \
mariadb-server mariadb-client subversion mtr-tiny ipmitool graphviz imagemagick apache2 \
python3-mysqldb python3-pymysql python-is-python3
When prompted for the confirmation, input y to confirm and press ENTER to proceed. And the installation will begin.
After the package dependencies are installed, you will next set up and configure the LAMP Stack for the Observium installation.
Setting Up MariaDB Server
You will now set up the MariaDB server that will be used for the Observium. You will secure the MariaDB deployment via the 'mysql_secure_installation' command, then create a new database and user that will be used for the Observium installation.
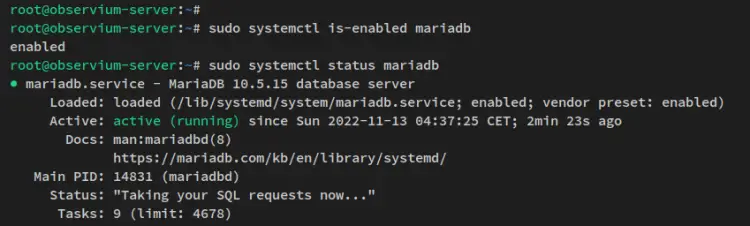
Before you begin, run the following systemctl command to ensure that the MariaDB service is enabled and running.
sudo systemctl is-enabled mariadb
sudo systemctl status mariadb
You will see the following output - the MariaDB service is enabled and will be run automatically upon the bootup. And the current status of the MariaDB service running.
Next, secure the MariaDB server deployment via the 'mysql_secure_installation' command below.
sudo mysql_secure_installation
You'll now be prompted with some of the MariaDB configurations:
- Switch the MariaDB root user to the unix_socket authentication method? Input n for no.
- Set up a new MariaDB root password? Input y to confirm, then type the new password for your MariaDB deployment and repeat the password.
- Disable remote login for the MariaDB root user? Input y to confirm and disable it.
- Remove the default anonymous user from MariaDB? Input y.
- Remove the default database test from MariaDB? Input y.
- Lastly, reload all tables privileges to apply new changes? Input y to confirm.
Now that you've secured the MariaDB installation configured the MariaDB with the root password. You'll then create a new MariaDB database and user for the Observium.
Run the following command to log in to the MariaDB shell as the MariaDB root user.
sudo mysql -u root -p
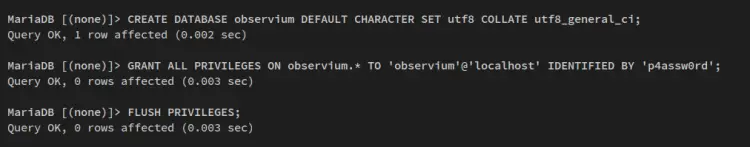
Run the following queries to create a new database and user for the Observium. You can also change the database name, database user, and password with your details.
This example will create a new database and user 'observium' with the password 'p4ssw0rd'.
CREATE DATABASE observium DEFAULT CHARACTER SET utf8 COLLATE utf8_general_ci;
GRANT ALL PRIVILEGES ON observium.* TO 'observium'@'localhost' IDENTIFIED BY 'p4ssw0rd';
FLUSH PRIVILEGES;
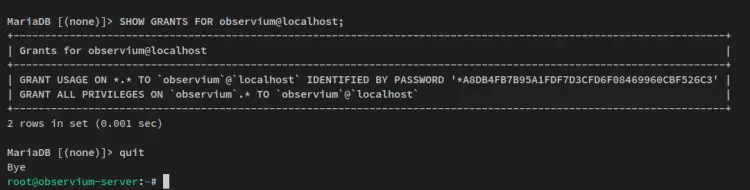
Now run the below query to ensure that the MariaDB user 'observium' has access and privileges to the 'observium' database.
SHOW GRANTS FOR observium@localhost;
quit
You will see the output like the below screenshot - The MariaDB user 'observium' has privileges to the database 'observium'.
Now that you have configured the MariaDB server and created the database and user for Observium. Next, you will go over the PHP configurations.
Setting Up PHP
To install Observium, you must edit some configuration of PHP. You'll make a change to the PHP configuration 'php.ini' file and enable the PHP opcache. Also, you'll verify the configuration of the PHP and Apache2 web server via the PHPINFO, which will ensure that the Apache2 and PHP is working.
Edit the file '/etc/php/7.4/apache2/php.ini' using the following nano editor command.
sudo nano /etc/php/7.4/apache2/php.ini
Uncomment the following configuration and make sure to change the 'error_reporting' option with something like this.
file_uploads = On
default_charset = UTF-8
error_reporting = E_ALL & ~E_NOTICE
date.timezone = Europe/London
On the '[opcache]' option, change the following settings. This will enable the PHP opcache extension and add some configuration to get the max performance.
[opcache]
opcache.enable=1
opcache.enable_cli=1
opcache.interned_strings_buffer=8
opcache.max_accelerated_files=10000
opcache.memory_consumption=128
opcache.save_comments=1
opcache.revalidate_freq=1
Save the file and exit the editor when you are finished.
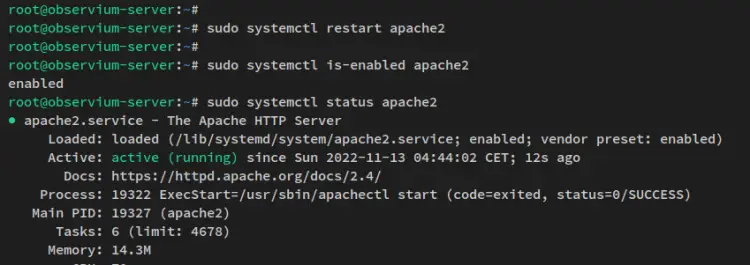
Now restart the Apache2 service via the systemctl command below and apply new changes.
sudo systemctl restart apache2
Verify the Apache2 service status using the below command to ensure that the Apache2 service is running and enabled.
sudo systemctl is-enabled apache2
sudo systemctl status apache2
You'll then see the output like this - The Apache2 service is enabled and will be run automatically upon the bootup. And the current status of the Apache2 service is running.
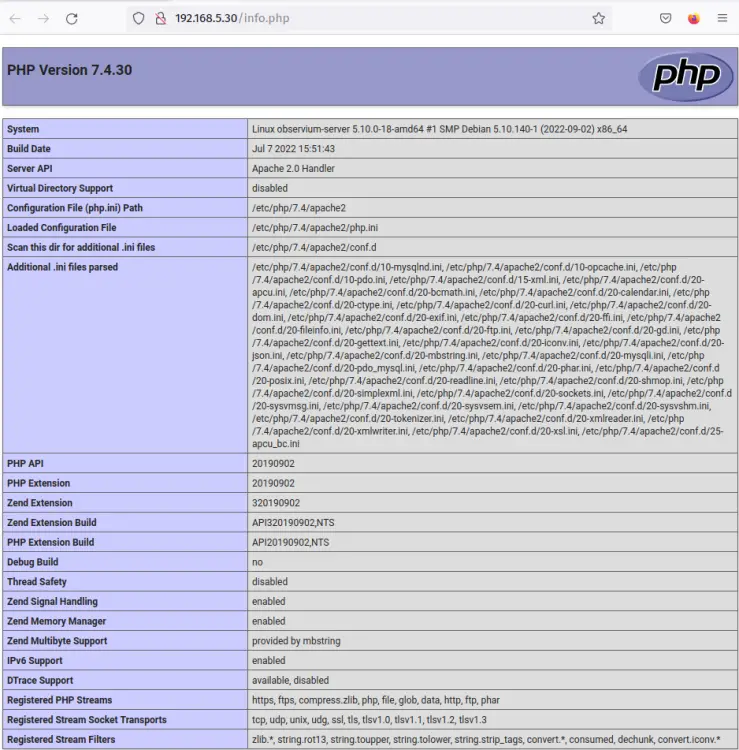
To ensure that Apache2 and PHP are working, you will create a new PHPINFO file. Run the following command to create a new PHPINFO file '/var/www/html/info.php'.
echo '<?php phpinfo(); ?>' | tee /var/www/html/info.php
Open your web browser and visit the server IP address followed by the path '/info.php' (i.e: http://192.168.5.30/info.php).
If Apache2 and PHP are configured correctly, you'll then see the PHPINFO page as the following. You'll see detailed information about your PHP installation and configuration.
Now that you've configured the MariaDB database server and PHP, you will next download the Observium source code and configure the Observium installation.
Installing Observium Network Monitoring Tool
In this step, you will download the Observium source code, set up the database details for Observium, import the database schema, and lastly create an administrator user for the Observium installation.
Move the working directory to '/opt' and download the Observium source code via the wget command below. When the download process is finished, you will see the file 'observium-community-latest.tar.gz' in your current working directory.
cd /opt
wget http://www.observium.org/observium-community-latest.tar.gz
Extract the file 'observium-community-latest.tar.gz' via the tar command below.
tar zxvf observium-community-latest.tar.gz
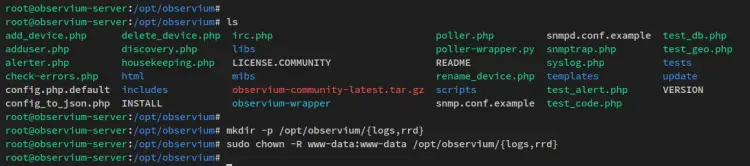
Now the Observium source will be available in the '/opt/observium' directory, which will be the target installation directory for Obserevium Monitoring Tool.
Next, create new additional directories that will be used to store logs and rrd files. Then, change the ownership of new directories to the user and group 'www-data'.
mkdir -p /opt/observium/{logs,rrd}
sudo chown -R www-data:www-data /opt/observium/{logs,rrd}
After created additional directories, move to the Observium installation directory '/opt/observium'.
cd /opt/observium
Copy the Observium default configuration 'config.php.default' to 'config.php'. Then, edit the new file 'config.php' via the following nano editor.
cp config.php.default config.php
nano config.php
Change the default database settings with your database details.
$config['db_extension'] = 'mysqli';
$config['db_host'] = 'localhost';
$config['db_user'] = 'observium';
$config['db_pass'] = 'p4ssw0rd';
$config['db_name'] = 'observium';
Save the file and exit the editor when you are finished.
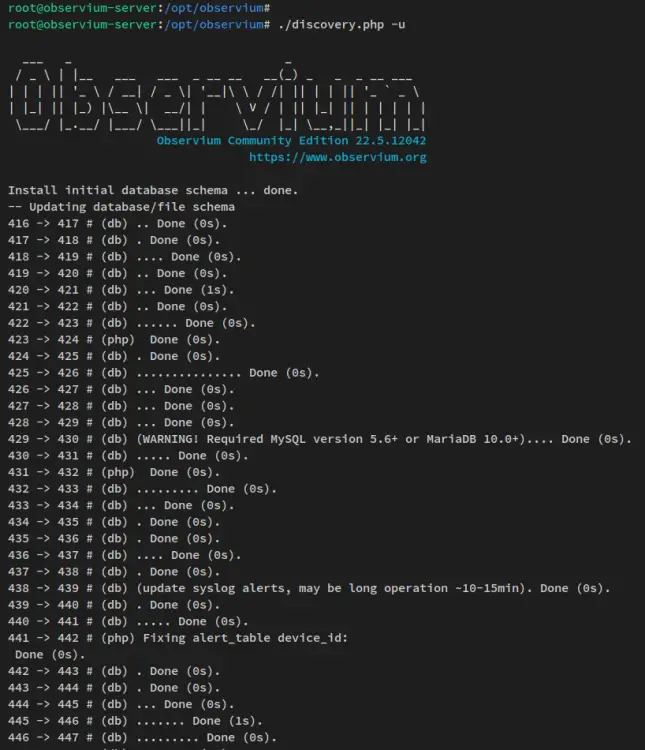
Next, run the script 'discovery.php' to update the database and import the database schema for the Observium installation.
./discovery.php -u
You will receive the output like the following screenshot.
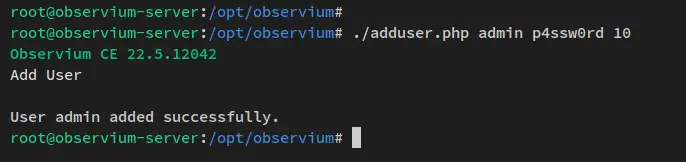
After the Observium database schema is imported, run the script 'adduser.php' to set up the administrator user for the Observium.
This example will create a new user 'admin' with the password 'p4ssw0rd' and role is '10' which is the highest role on Observium as an administrator.
./adduser.php admin p4ssw0rd 10
After the user is created, you will see a message such as 'User admin added successfully.'
At this point, you have finished the basic installation and configuration of the Observium Network Monitoring Tool. But, you still need to set up the Apache2 virtual host configuration for Observium.
Configuring Apache2 Virtual Host
After installed and configured Observium, you will now set up the new Apache2 virtual host configuration of Observium. Before you begin, ensure that you have the local domain name for the Observium installation.
Create a new virtual host configuration '/etc/apache2/sites-available/observium.conf' using the following nano editor command.
sudo nano /etc/apache2/sites-available/observium.conf
Add the below configuration to the file and ensure to change the domain name. This example uses the local domain obs.howtoforge.local.
<VirtualHost *:80>
ServerAdmin webmaster@localhost
ServerName obs.howtoforge.local
DocumentRoot /opt/observium/html
<FilesMatch \.php$>
SetHandler application/x-httpd-php
</FilesMatch>
<Directory />
Options FollowSymLinks
AllowOverride None
</Directory>
<Directory /opt/observium/html/>
DirectoryIndex index.php
Options Indexes FollowSymLinks MultiViews
AllowOverride All
Require all granted
</Directory>
ErrorLog ${APACHE_LOG_DIR}/error.log
LogLevel warn
CustomLog ${APACHE_LOG_DIR}/access.log combined
ServerSignature On
</VirtualHost>
Save the file and exit the editor when you are finished.
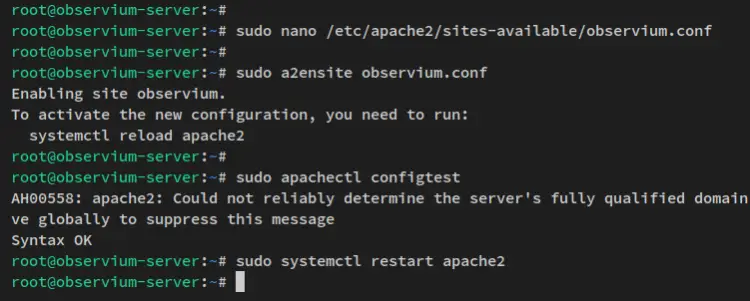
Now activate the virtual host configuration 'observium.conf' via the a2ensite command below. Then, verify the Apache2 configurations to ensure that you have the correct configuration.
sudo a2ensite observium.conf
sudo apachectl configtest
You should now see the output message such as 'Syntax OK', which means your Apache2 configuration is correct.
Lastly, run the following systemctl command to restart the Apache2 service and apply new changes.
sudo systemctl restart apache2
Now that you have configured the Apache2 virtual host. You can now access your Observium installation via your local domain.
Accessing Observium via Web Browser
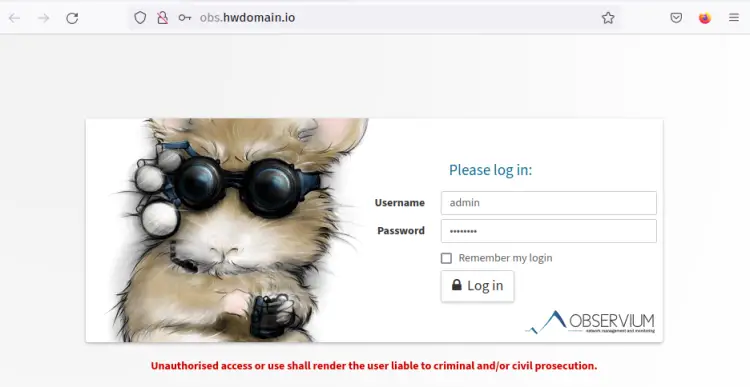
After configured the virtual host for Observium, you will now access Observium via the web browser.
Open your web browser and visit the local domain name of your Observium installation (i.e: http://obs.howtoforge.local/). You should now see the Observium login page.
Log in with your user and password, then click 'Log in'.
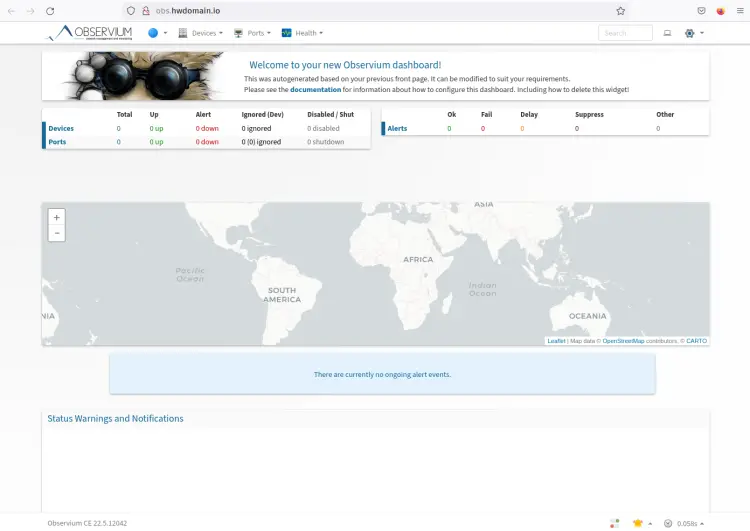
Now you should see the Observium administration dashboard. From there you can now add new devices to monitor to the Observium via SNMP.
At this point, you have finished the basic installation of the Observium Network Monitoring Tool with the LAMP Stack on a Debian 11 server. You will next do the initial Discovery and pool.
Setting up Auto Discovery with Cron
Move to the Observium installation directory and run the script 'discovery.php' and 'poller.php' to populate data for new devices.
cd /opt/observium
./discovery.php -h all
./poller.php -h all
After that, create a new cron configuration '/etc/cron.d/observium' using the following nano editor command.
sudo nano /etc/cron.d/observium
Add the following configuration to the file.
# Run a complete discovery of all devices once every 6 hours
33 */6 * * * root /opt/observium/discovery.php -h all >> /dev/null 2>&1
# Run automated discovery of newly added devices every 5 minutes
*/5 * * * * root /opt/observium/discovery.php -h new >> /dev/null 2>&1
# Run multithreaded poller wrapper every 5 minutes
*/5 * * * * root /opt/observium/poller-wrapper.py >> /dev/null 2>&1
# Run housekeeping script daily for syslog, eventlog and alert log
13 5 * * * root /opt/observium/housekeeping.php -ysel >> /dev/null 2>&1
# Run housekeeping script daily for rrds, ports, orphaned entries in the database and performance data
47 4 * * * root /opt/observium/housekeeping.php -yrptb >> /dev/null 2>&1
Save the file and exit the editor when you are finished.
With the cron configuration, the autodiscovery and poller will be run automatically in the background.
Conclusion
In this tutorial, you have installed the Observium Network Monitoring Tool with the LAMP stack (Linux, Apache2, MariaDB, and PHP) on a Debian 11 server. You also have configured the auto-discovery setup for Observium via the cron script that you have created.
With all of these in place, you can now add devices to the Observium Network Monitoring Tool via SNMP agent, add a new user with a different level than the administrator, set up alerts, and many more.