How to List Unsuccessful SSH Logins on Linux
"There is no white or black, there are only shades of gray. We can not say if it's good or bad."
And sometimes we need to dig into the shades of gray and look for problems before they occur. One of these checks could be a search for failed SSH login attempts. Fortunately, Ubuntu comes with one solution that is simple enough but powerful enough to detect most cases where someone lets weak passwords and brute force attacks happen.
Each attempt to login to SSH server are recorded in a file named auth.log located at /var/log/auth.log by the rsyslog daemon.
Administrators can look through the logs to see if there are strange incoming traffic. A log file contains a lot of information in plain text but it is not easy reading all the output. We need to learn how to use grep to search through the log file and in this example we will focus on failed attempts.
Installing OpenSSH
OpenSSH is a service that provides secure remote access to systems in the form of an application layer protocol, it also includes scp command-line program. Login as a root user or switch to a user with sudo privileges, then use the command below to install OpenSSH:
sudo apt-get update
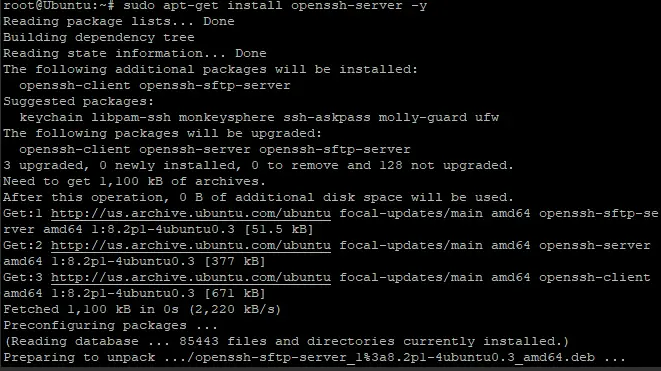
sudo apt-get install openssh-server -y
This command should install OpenSSH and its dependencies. You should see that there are additional packages being installed as well because OpenSSH requires quite many to operate properly.
After installation, you may enable ssh by typing the following command in the terminal window:
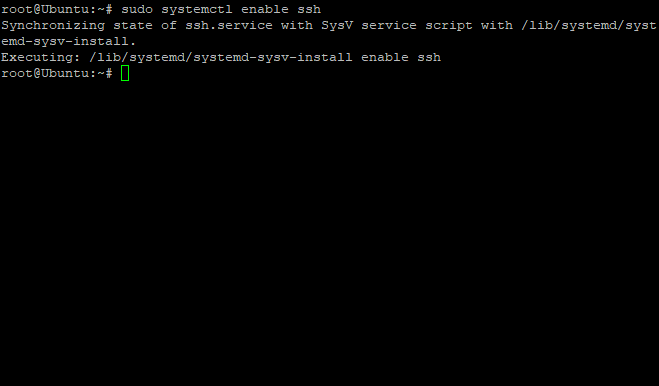
sudo systemctl enable ssh
You should see a similar output the image below in your terminal window if the command was successful:
The following commands can be used to stop SSH on Ubuntu machines in case you want to disable it:
sudo systemctl stop ssh
It can be started again by running:
sudo systemctl start ssh
To check if the SSH server is running you can use command below:
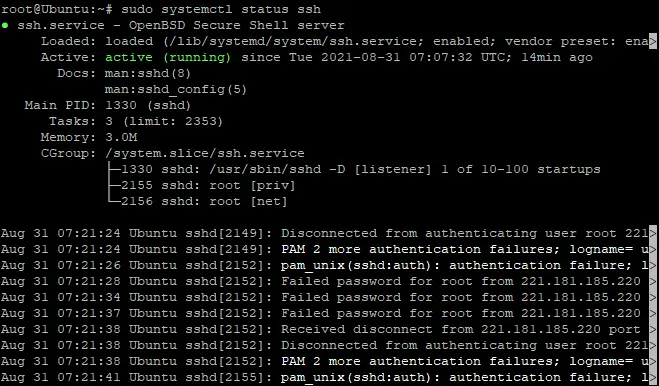
sudo systemctl status ssh
You should see a similar output in your terminal:
In the above screenshot, you can see that SSH server is already running and enabled, which means it will run at boot time.
How to Find All Failed SSH login Attempts
A failed login attempt could be caused by a variety of reasons and not just an automated login exploit. A failed login attempt can happen when:
- A user may mistype his password.
- Trying to use an incorrect password to log in.
- The server is under a brute force attack and hackers are trying to guess the password using automated scripts.
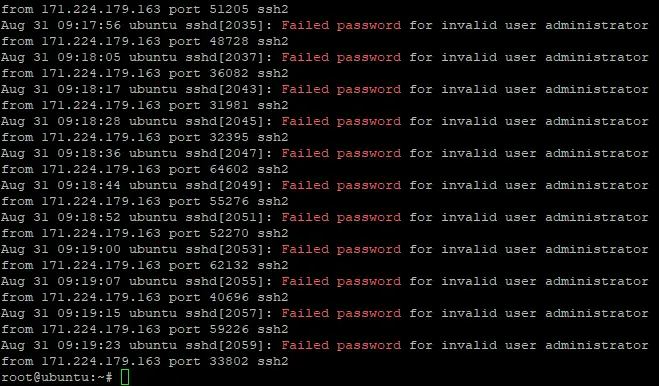
The easiest way to list all failed SSH login attempts is to use the following command:
grep "Failed password" /var/log/auth.log
You should see similar output in your terminal:
The following commands can be used to display failed SSH logins in CentOS or RHEL in a slightly modified version of the above command:
grep "Failed" /var/log/secure
grep "authentication failure" /var/log/secure
Alternatively, we may view the logs using the Systemd daemon with the journalctl command:
journalctl _SYSTEMD_UNIT=ssh.service | egrep "Failed|Failure"
To display a list of all IP addresses which are responsible for failed SSH login attempts, with the number of attempts next to it, you can use this command:
grep "Failed password" /var/log/auth.log | awk ‘{print $11}’ | uniq -c | sort -nr
It is inevitable that a failed login attempt will occur from time to time. However, it remains crucial to identify the failed logins to your server. It is important to identify the IP addresses that frequently hit your SSH server and take the necessary actions.
Conclusion
In this guide, we have covered how to find failed SSH login attempts on a Linux machine. We also learned a different approach which involves using the journalctl command. We hope you found this article helpful. Feel free to provide your feedback or any questions you may have in the comments section.