How to Install Tiki Wiki with Apache and Let's encrypt SSL on Debian 10
TikiWiki is a free and open-source content management system written in PHP language. It is is very powerful, full-featured and can be used to create websites, wikis, Web applications, knowledge-base, portals, image galleries and many more. TikiWiki made up from four major components content creation and management tools, communication tools, and configuration and administration tools, and content organization tools and navigation aids. These will allows you to create and manage content, and configure sites. TikiWiki comes with a rich set of features, including, Forums, Blog, Maps, Workspace, Slideshow, Shopping Cart, Bug and issue tracker, Multilingual, File and image gallery, Events and many more.
In this tutorial, we will learn how to install TikiWiki CMS on Debian 10.
Requirements
- A server running Debian 10.
- A root password is set up to your server.
Getting Started
Before starting, you will need to update your system with the latest version. You can do this by running the following command:
apt-get update -y
apt-get upgrade -y
Once your server is updated, restart your server to apply the changes.
Install LAMP Server
TikiWiki runs on Apache / Nginx web server, written in PHP language and use MariaDB/MySQL to store its data. So you will need to install Apache, MariaDB, PHP and other required extensions on your server. First, install Apache and MariaDB server with the following command:
apt-get install apache2 mariadb-server unzip -y
By default, Debian 10 ships with PHP version 7.3. But, TikiWiki does not support PHP 7.3. So, you will need to install PHP 7.2 and other required extensions.
To add SURY repository, first download and GPG key with the following command:
wget https://packages.sury.org/php/apt.gpg
apt-key add apt.gpg
Next, add the SURY repository to APT with the following command:
echo "deb https://packages.sury.org/php/ $(lsb_release -sc) main" | tee /etc/apt/sources.list.d/php.list
Next, update the repository and install PHP7.2 along with all required extensions with the following commands:
apt-get update -y
apt-get install php7.2 libapache2-mod-php7.2 php7.2-common php7.2-sqlite3 php7.2-curl php7.2-intl php7.2-mbstring php7.2-xmlrpc php7.2-mysql php7.2-gd php7.2-xml php7.2-cli php7.2-zip -y
After installing PHP7.2, open php.ini file and tweak some settings:
nano /etc/php/7.2/apache2/php.ini
Add the following lines:
memory_limit = 256M upload_max_filesize = 100M max_execution_time = 360 date.timezone = Asia/Kolkata
Save and close the file when you are finished. Then, proceed to the next step.
Create Database for TikiWiki
By default, MariaDB is not secured. So, you will need to secure it first. You can secure it with the following script:
mysql_secure_installation
You should answer all the questions as shown below:
Enter current password for root (enter for none):
Set root password? [Y/n]: N
Remove anonymous users? [Y/n]: Y
Disallow root login remotely? [Y/n]: Y
Remove test database and access to it? [Y/n]: Y
Reload privilege tables now? [Y/n]: Y
Once MariaDB is secured, login to MariaDB shell:
mysql -u root -p
Provide your root password when prompt then create a database and user for TikiWiki with the following command:
MariaDB [(none)]> CREATE DATABASE tikidb;
MariaDB [(none)]> CREATE USER 'tiki'@'localhost' IDENTIFIED BY 'password';
Next, grant all the privileges to TikiWiki Database with the following command:
MariaDB [(none)]> GRANT ALL ON tikidb.* TO 'tiki'@'localhost' IDENTIFIED BY 'password' WITH GRANT OPTION;
Next, flush the privileges and exit from the MariaDB shell with the following command:
MariaDB [(none)]> FLUSH PRIVILEGES;
MariaDB [(none)]> EXIT;
Once you have done, you can proceed to the next step.
Download TikiWiki
First, you will need to download the latest version of TikiWiki from the Sourceforge website. You can download it with the following command:
cd /var/www/html/
wget https://sourceforge.net/projects/tikiwiki/files/latest/download -O tikiwiki.zip
Once the download is completed, unzip the downloaded file with the following command:
unzip tikiwiki.zip
Next, rename the extracted directory to tikiwiki with the following command:
mv tiki-20.0 tikiwiki
Next, give proper permissions to the tikiwiki directory with the following command:
chown -R www-data:www-data /var/www/html/tikiwiki/
chmod -R 755 /var/www/html/tikiwiki/
Once you have finished, you can proceed to the next step.
Configure Apache for TikiWiki
Next, you will need to create an Apache virtual host configuration file for TikiWiki. You can create it with the following command:
nano /etc/apache2/sites-available/tikiwiki.conf
Add the following content:
<VirtualHost *:80>
ServerAdmin [email protected]
DocumentRoot /var/www/html/tikiwiki
ServerName example.com
<Directory /var/www/html/tikiwiki/>
Options FollowSymlinks
AllowOverride All
Require all granted
</Directory>
ErrorLog ${APACHE_LOG_DIR}/tikiwiki_error.log
CustomLog ${APACHE_LOG_DIR}/tikiwiki_access.log combined
</VirtualHost>
Save and close the file. Then, enable the virtual host configuration file with the following command:
a2ensite tikiwiki.conf
Finally, enable Apache rewrite module and restart Apache service to reload the configuration changes with the following command:
a2enmod rewrite
systemctl restart apache2
Access TikiWiki Web Interface
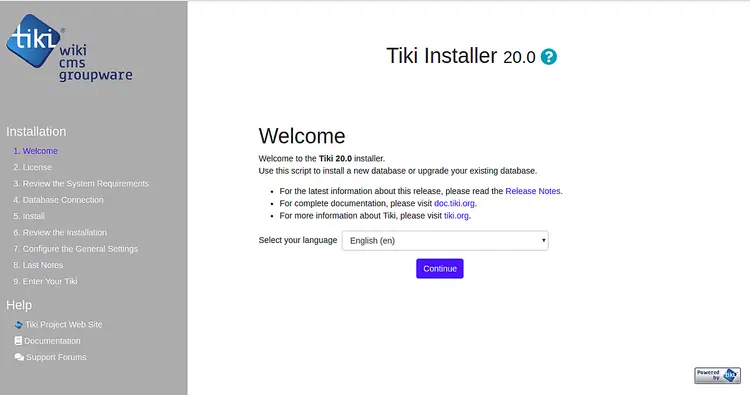
Now, open your web browser and type the URL http://example.com. You will be redirected to the TikiWiki welcome page:
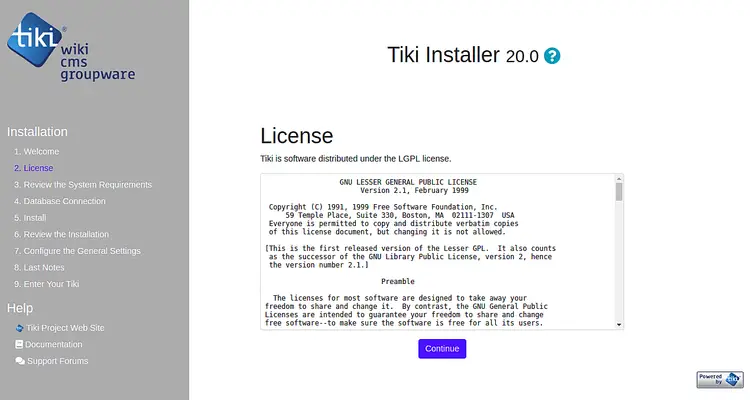
Select your language and click on the Continue button. You should see the following page:
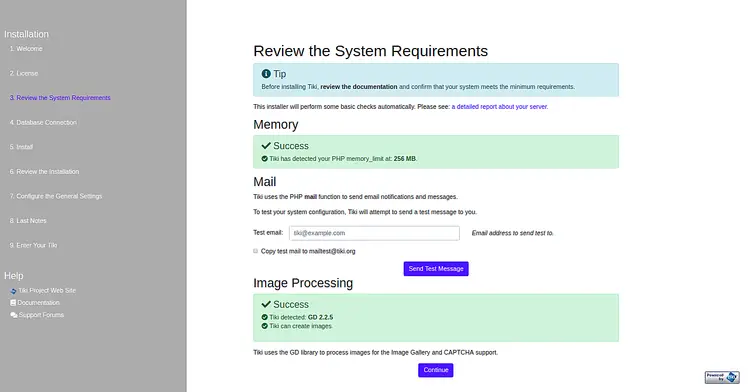
Accept the License agreement and click on the Continue button. You should see the following page:
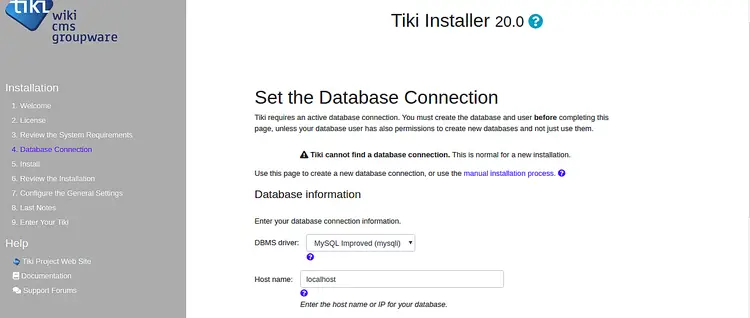
Confirm your system meet the minimum requirements and click on the Continue button. You should see the following page:
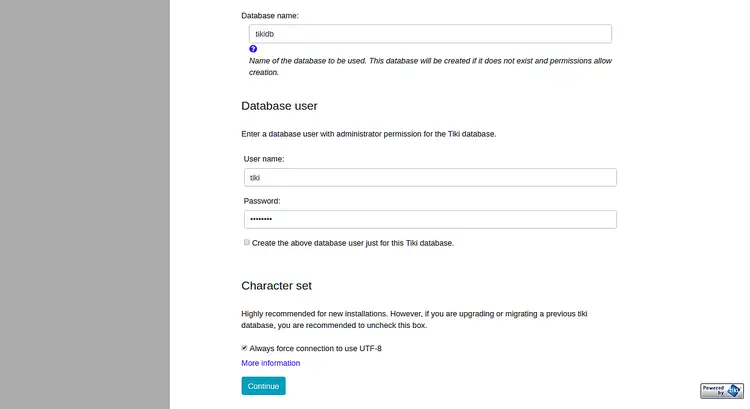
Provide your database name, database username and password. Then, click on the Continue button. You should see the following page:
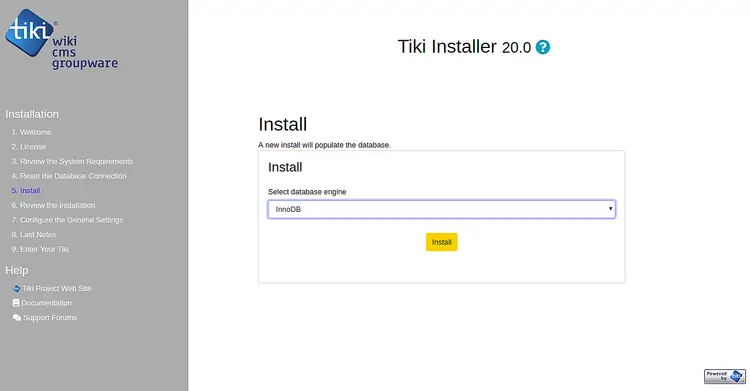
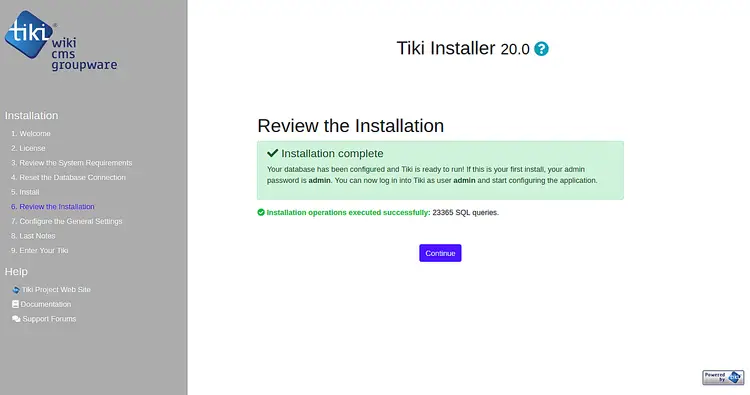
Select the database engine and click on the Install button to start the installation. Once the installation has been completed successfully, you should see the following page:
Now, click on the Continue button, you should see the following page:
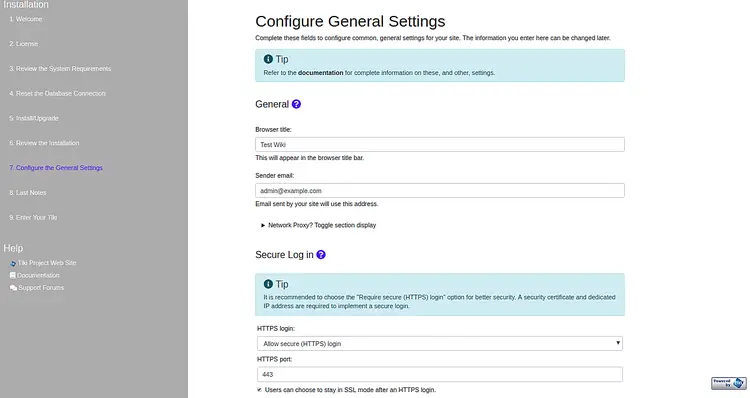
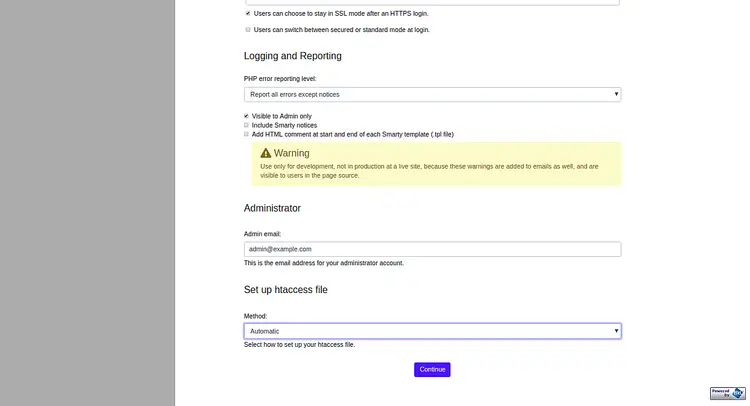
Provide all the required information like Wiki title, Sender email, Secure login, Admin email and click on the Continue button. You should see the following page:
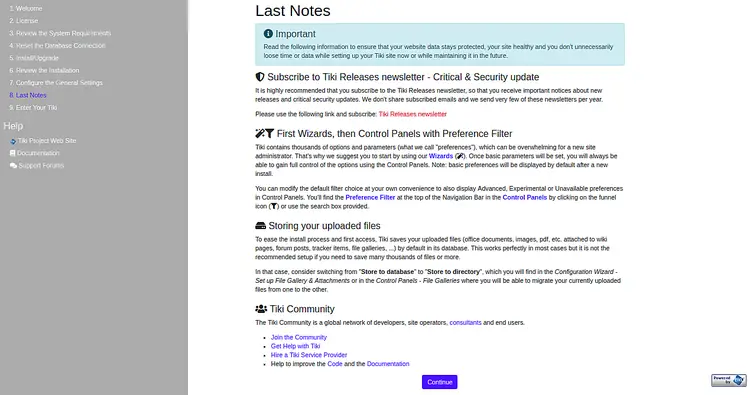
Read all the information and click on the Continue button. You should see the following page:
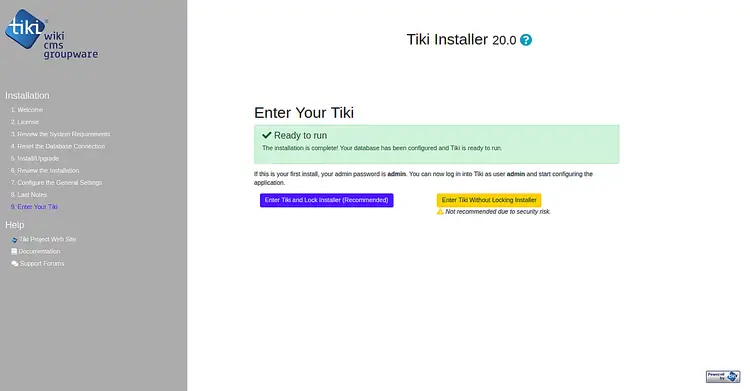
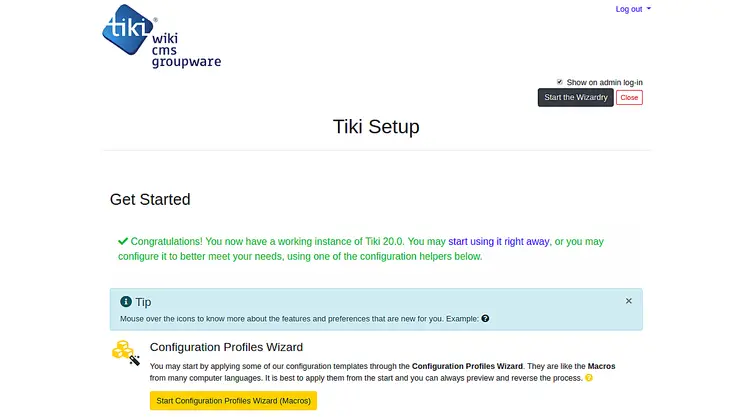
Now, click on the "Enter Tiki and Lock Installer" button. You should see the following page:
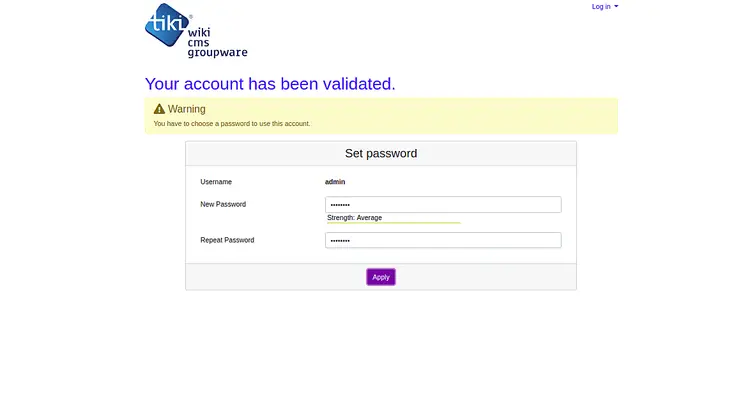
Now, set your admin password and click on the Apply button. You should see the following page:
Secure TikiWiki with Let’s Encrypt
In this section, we will explain how to secure your TikiWiki site with Let’s Encrypt free SSL.
First, you will need to install Certbot tool to download and install Let’s Encrypt free SSL for your website. By default, the latest version of Certbot is not available in the Debian 10 default repository. So, you will need to add Certbot repository to your system.
You can add the Certbot repository with the following command:
apt-get install software-properties-common
add-apt-repository ppa:certbot/certbot
Next, update the repository and install Certbot with the following command:
apt-get update -y
apt-get install certbot python-certbot-apache -y
Once installed, create a well-known.conf file for Let’s Encrypt to validate your domain.
First, create a .well-known directory and give proper permissions:
mkdir -p /var/lib/letsencrypt/.well-known
chgrp www-data /var/lib/letsencrypt
chmod g+s /var/lib/letsencrypt
Next, create a well-known.conf file with the following command:
nano /etc/apache2/conf-available/well-known.conf
Add the following lines:
Alias /.well-known/acme-challenge/ "/var/lib/letsencrypt/.well-known/acme-challenge/"
<Directory "/var/lib/letsencrypt/">
AllowOverride None
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
Require method GET POST OPTIONS
</Directory>
Save and close the file. Then, enable the required modules with the following command:
a2enmod ssl
a2enmod http2
a2enmod headers
a2enconf well-known
Next, restart Apache service to apply all the configuration changes:
systemctl restart apache2
Now, let's start to install the free SSL certificate for your domain example.com with the following command:
certbot --apache -d example.com
First, you will need to provide a valid email address and agree to the terms of service as shown below:
Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator apache, Installer apache Enter email address (used for urgent renewal and security notices) (Enter 'c' to cancel): [email protected] - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Please read the Terms of Service at https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf. You must agree in order to register with the ACME server at https://acme-v02.api.letsencrypt.org/directory - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (A)gree/(C)ancel: A - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Would you be willing to share your email address with the Electronic Frontier Foundation, a founding partner of the Let's Encrypt project and the non-profit organization that develops Certbot? We'd like to send you email about our work encrypting the web, EFF news, campaigns, and ways to support digital freedom. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - (Y)es/(N)o: Y Obtaining a new certificate Performing the following challenges: http-01 challenge for example.com Enabled Apache rewrite module Waiting for verification... Cleaning up challenges Created an SSL vhost at /etc/apache2/sites-available/example.com-le-ssl.conf Deploying Certificate to VirtualHost /etc/apache2/sites-available/example.com-le-ssl.conf Enabling available site: /etc/apache2/sites-available/example.com-le-ssl.conf Please choose whether or not to redirect HTTP traffic to HTTPS, removing HTTP access. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 1: No redirect - Make no further changes to the webserver configuration. 2: Redirect - Make all requests redirect to secure HTTPS access. Choose this for new sites, or if you're confident your site works on HTTPS. You can undo this change by editing your web server's configuration. - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Select the appropriate number [1-2] then [enter] (press 'c' to cancel): 2
Next, choose option 2 to download and install free SSL certificate for your domain. Once the installation has been completed successfully. You should get the following output:
Enabled Apache rewrite module Redirecting vhost in /etc/apache2/sites-enabled/example.com.conf to ssl vhost in /etc/apache2/sites-available/ example.com-le-ssl.conf - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - Congratulations! You have successfully enabled https://example.com You should test your configuration at: https://www.ssllabs.com/ssltest/analyze.html?d=example.com - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at: /etc/letsencrypt/live/example.com/fullchain.pem Your key file has been saved at: /etc/letsencrypt/live/example.com/privkey.pem Your cert will expire on 2019-10-22. To obtain a new or tweaked version of this certificate in the future, simply run certbot again with the "certonly" option. To non-interactively renew *all* of your certificates, run "certbot renew" - Your account credentials have been saved in your Certbot configuration directory at /etc/letsencrypt. You should make a secure backup of this folder now. This configuration directory will also contain certificates and private keys obtained by Certbot so making regular backups of this folder is ideal. - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le
That's it. Now, open your web browser and access your TikiWiki CMS using the URL https://example.com. You should that your TikiWiki site is properly secured with free SSL certificate.