Firewall Access Policy Rulesets, Part 4
| Author: [email protected] http://www.fwbuilder.org |
This article continues the series of articles on Firewall Builder, a graphical firewall configuration and management tool that supports many Open Source firewall platforms as well as Cisco IOS access lists and Cisco ASA (PIX). Firewall Builder was introduced on this site earlier with articles Getting Started With Firewall Builder, Using Firewall Object In Firewall Builder. Firewall Access Policy Rulesets, Part 1. Firewall Access Policy Rulesets, Part 2.
This article continues with examples of Access Policy rules and demonstrates how IPv6 and mixed IPv4+IPv6 configurations can be built.
More information on Firewall Builder, pre-built binary packages and source code, documentation can be found on the project web site at http://www.fwbuilder.org/. Numerous examples of iptables, pf and other rules are available in Firewall Builder Users Guide. Follow Firewall Builder Project Blog for announcements and articles on all aspects of using Firewall Builder.
Adding IPv6 Rules to a Policy
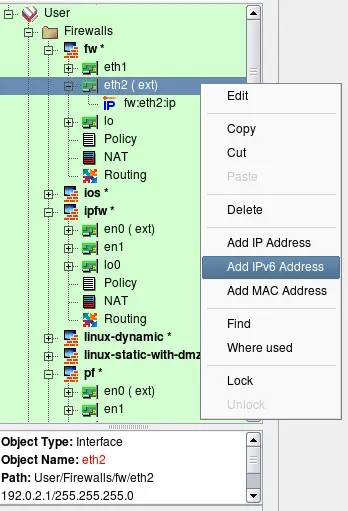
We start with a firewall object that has some basic IPv4 policy. First, we need to add IPv6 addresses to its interfaces. Open context menu associated with interface object in the tree and click on the item "Add IPv6 address".
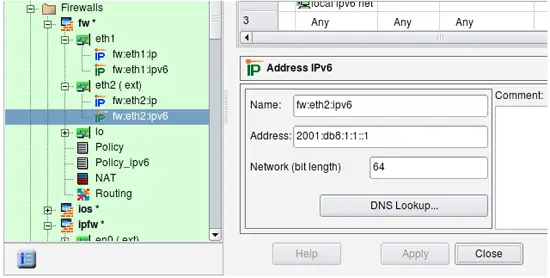
Enter the address and netmask length (use your own address!):
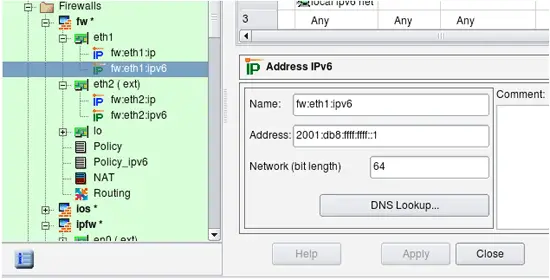
Add IPv6 to internal interface:
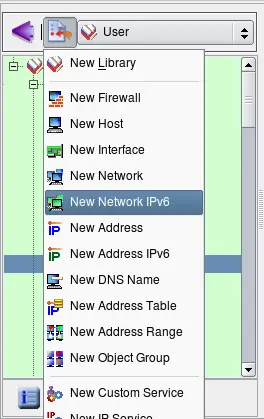
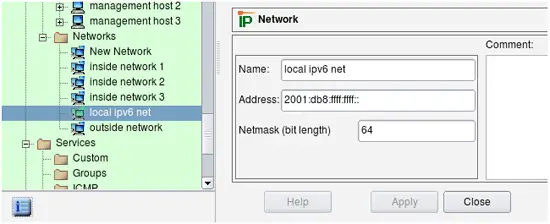
We also need to create network object to represent our local IPv6 network. Click New Network IPv6 in the new object menu.
Enter the name and address of this network. We are using the link-local address for illustration purposes.
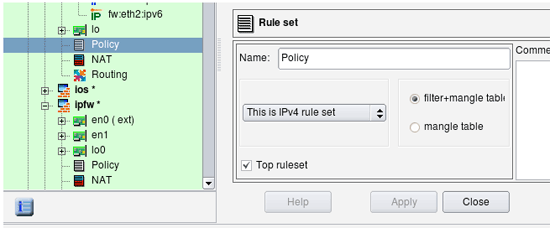
Inspect the regular Policy object. To see its parameters, double-click on it in the tree to open it in the editor (see screenshot below). This object has a Name, IPv4/IPv6 setting and a Top ruleset checkbox. For iptables firewalls, there is also a pair of radio buttons that indicates whether the policy should affect filter+mangle tables or just mangle table.
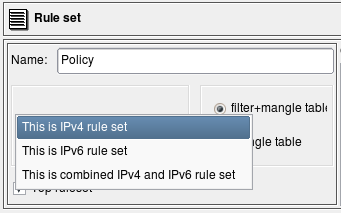
The IPv4/IPv6 setting tells the compiler how it should interpret addresses of objects that appear in the rules. Possible configurations are "IPv4 only", "IPv6 only" and "Mixed IPv4 and IPv6":
-
"IPv4 only rule set" - Only addressable objects with IPv4 addresses will be used in the rules. If an object with ipv6 address appears in rules, it is ignored. IPv6-only services such as ICMPv6 are also ignored. TCP and UDP services are used since they apply for both IPv4 and IPv6 rules.
-
"IPv6 only rule set" - The opposite, only objects with ipv6 addresses are used and those with ipv4 addresses are ignored. IPv6-only services such as ICMPv6 are used but IPv4-only services such as ICMP are ignored. TCP and UDP services are used since they apply for both IPv4 and IPv6 rules.
-
"Mixed IPv4 and IPv6 only rule set" - compiler makes two passes over the same rules, first to produce IPV4 configuration and then to produce IPV6 configuration. On each pass it uses only address objects with addresses matching address family of the pass. This is the best configuration for transitional configurations when IPv6 rules are gradually added to existing IPv4 configuration. Note that if you add IPv6 address to an interface of a firewall or a host object used in the rules, compiler will use IPv4 addresses of the interface on IPv4 pass and new IPv6 address of the same interface on the IPv6 pass. This principle also applies to the mixed groups of addresses and services.
Compilers treat the "top rule set" parameter differently, depending on the firewall platform:
-
iptables: rules defined in such rule set will go into built-in chains INPUT,OUTPUT,FORWARD etc. Rules defined in rule sets where this checkbox is not checked go into user-defined chain with the name the same as the name of the rule set.
-
PF: rules defined in the rule set with "top rule set" checkbox turned off go into an anchor with the name of the rule set.
-
Cisco IOS access lists: if top rule set checkbox is turned off, the rules go into access list with the name prefixed with the name of the rule set; this access list will not be assigned to interfaces via "ip access-group" command. Rulesets with checkbox "top rule set" checked generate ACLs with names consisting of the shortened name of interface and direction abbreviation ("in" or "out"). Only these lists are assigned to interfaces.
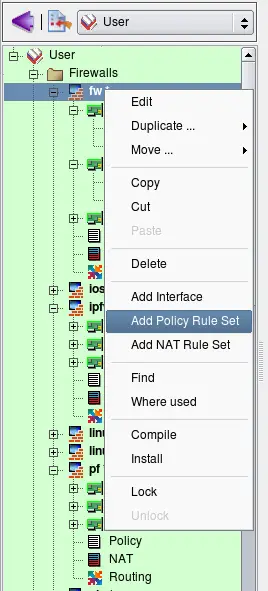
To add new policy, right-click on the firewall object in the tree to open the context menu and use menu item Add Policy Rule Set.
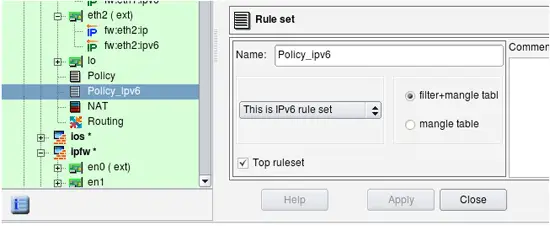
Assign a unique name to the new policy object, make it IPv6 and check the top ruleset checkbox, then click Apply.
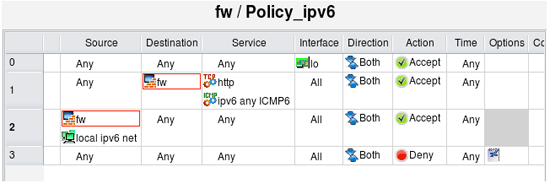
Now click on the new policy object in the tree ("Policy_ipv6") and add some rules as usual. Here we have added a rule to permit all on loopback, a rule to permit incoming HTTP and ICMP6 to the firewall and a rule to permit outgoing sessions from the internal network (object "local ipv6 net") and the firewall itself.