Wifi Authentication/Accounting With FreeRadius On CentOS 5 - Page 3
Step 6 ******************** Configure end wifi clients ********************
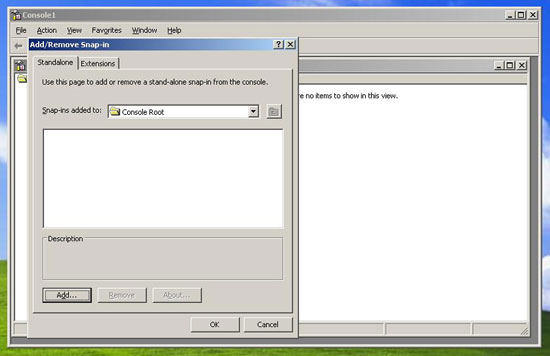
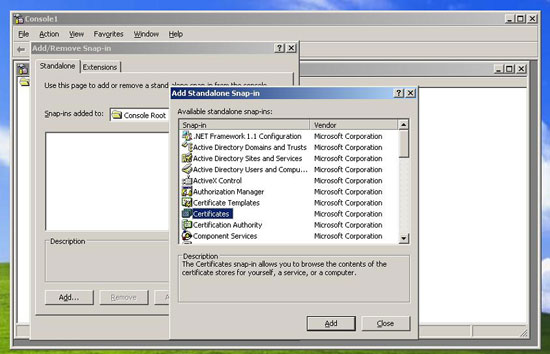
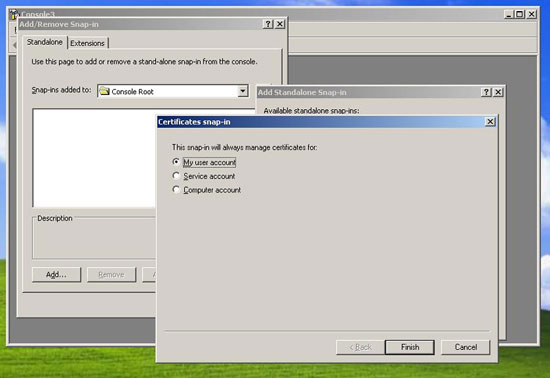
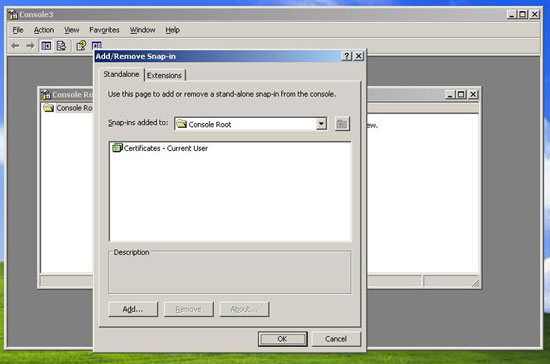
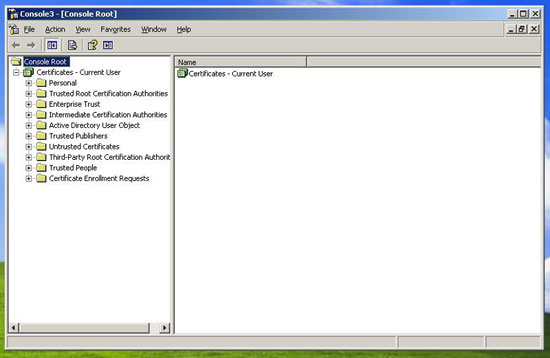
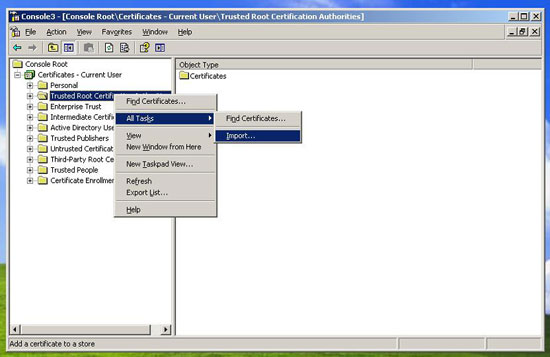
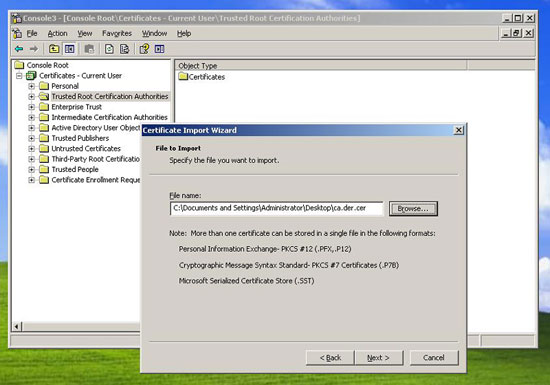
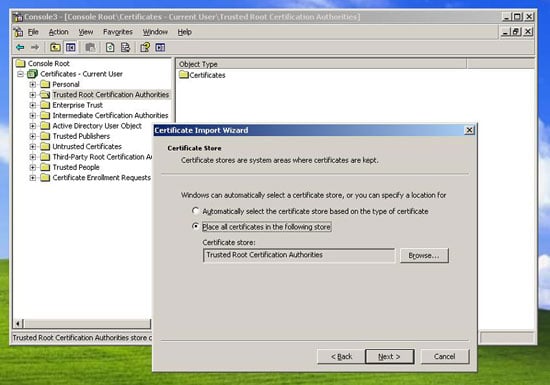
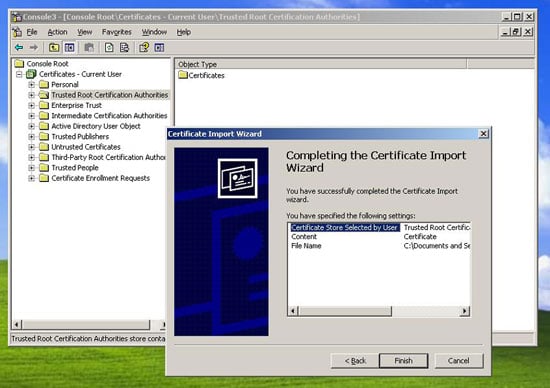
Install certificates
Certification authority CA.der (according to above certificate method it should be cacert.der).
Server certificate with keys sever.p12 (according to above certificate method, it should be server_keycert.p12).
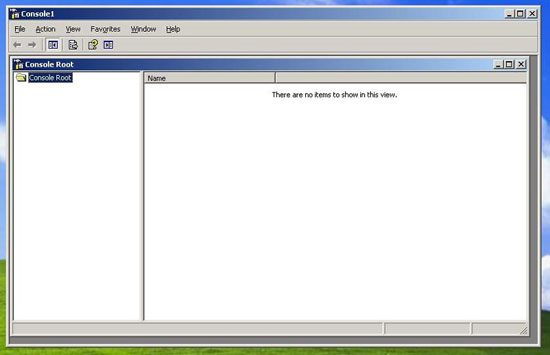
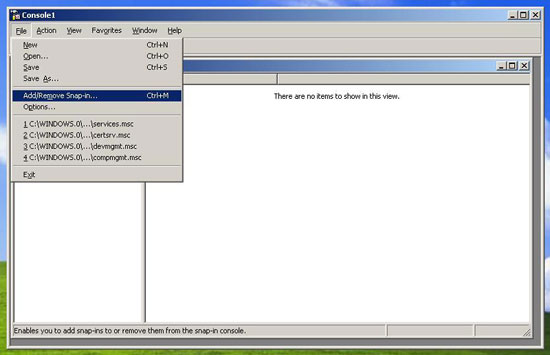
Note: The following screenshots are from Windows 2003 server. But it shouldn't be very different for Windows XP.
Go to “start”, select “run”& type “mmc”.
Follow the same procedure for importing server.p12 certificate into “trusted Root” section.
That is it for EAP/PEAP (TTLS), but for TLS you also need to import/install the client certificate. (You would also need to modify your eap.conf file for TLS.)
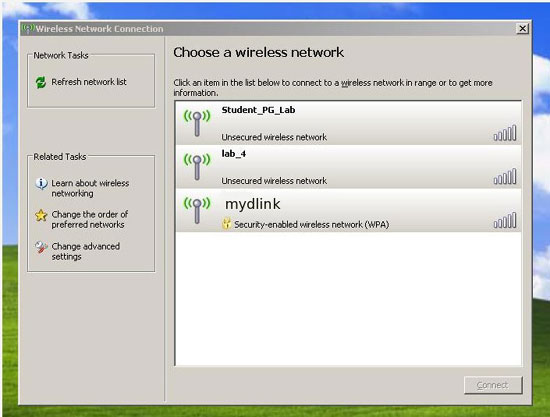
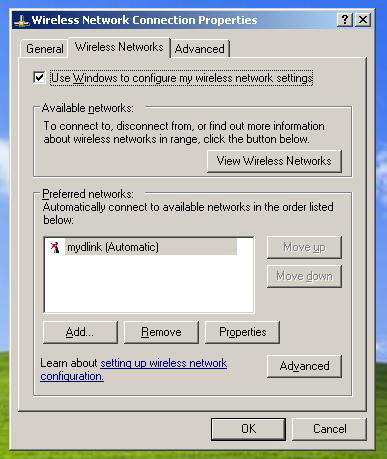
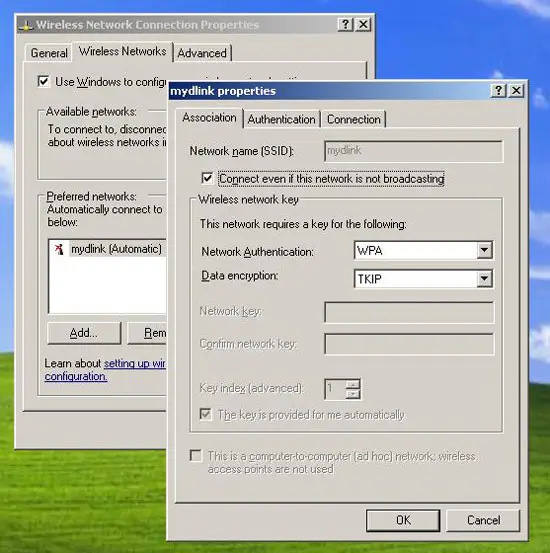
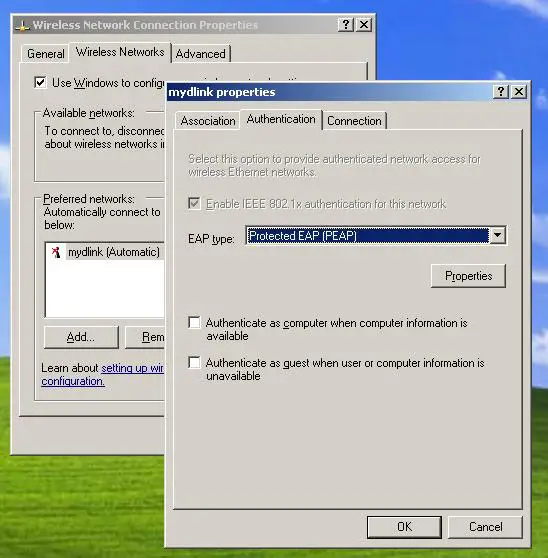
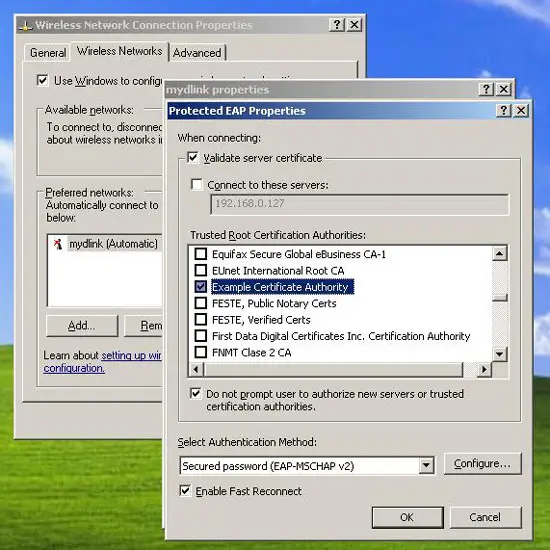
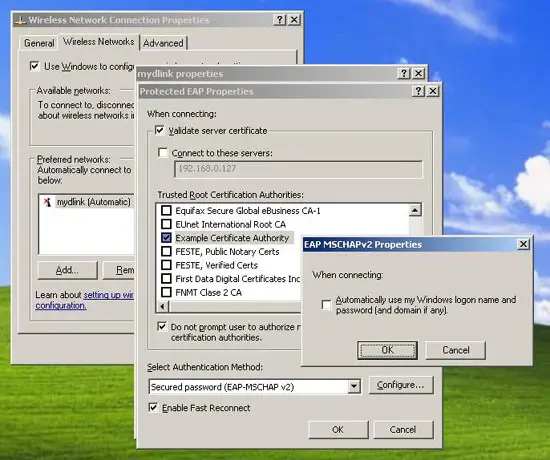
Configuring the wifi interface
View the “My network neighborhood”, choose your Access point, in this case “AP3200” (not really its named mydlink here).
- Press “ok”, “ok,and “ok”. Your done configuring the wifi.
- Immediately “disable”the wifi interface. Righ click & choose “disable”.
- After a second or two , re-enable the wifi interface. You should be prompted for username/password/Logindomain.
- Simply supply the username/password & press”ok”.
- You should connect in less than a second.
Congratulations you have configured a WPA1/2 enterprise wifi network.
Possible problems/Solutions:
- Freeradius not compiled with openssl support. (Google.)
- Certificates not installed correctly. (Use demo certificates/use some automating script.)
- End client XP is not supporting protocol. (Install possibly the latest service pack.)
- Client/AP not communicating. (Turn off the firewall or open the ports.)
- AP not communicating. (Reset/restart or update the firmware.)
- Client not getting authenticated. (Check logs/ run the freeradius server in debug mode e.g radiusd -X -z.)
Reference:
Note: Many thanks to freeradius.org developers, forum members & the people who wrote some of the mentioned below articles/howtos.
http://support.microsoft.com/kb/814394/en-us
http://wiki.freeradius.org/Main_Page
http://www.linux.com/base/ldp/howto/8021X-HOWTO/freeradius.htmlt#confradius
http://www.linuxjournal.com/article/8151
http://www.linuxjournal.com/article/8095
http://davenjudy.org/wordpress/?p=22
http://wiki.freeradius.org/HOWTO
http://www.wi-fiplanet.com/tutorials/article.php/3557251
http://www.wi-fiplanet.com/tutorials/article.php/3555556