Using iRedMail And OpenVPN For Virtual Email Hosting And VPN Services, With Central Authentication Against OpenLDAP (CentOS 5.4)
iRedMail is a shell script that lets you quickly deploy a full-featured mail solution in less than 2 minutes. iRedMail supports both OpenLDAP and MySQL as backends for storing virtual domains and users.
This tutorial shows you how to integrate OpenVPN into iredmail's ldap backend on CentOS 5.x, Let openvpn auth OpenLDAP?passwords will be stored in ldap and you can change the password though webmail.
This tutorial is based on CentOS 5.4, so I suggest set up a minimum CentOS 5.4 system, install iredmail 0.6 and choose openldap as the backend, as shown in these tutorials:
- iRedMail: Mail Server With LDAP, Postfix, RoundCube/SquirrelMail, Dovecot, ClamAV, SpamAssassin, Amavisd (Debian 5.0.1)
- iRedMail: Build A Full-Featured Mail Server With LDAP, Postfix, RoundCube, Dovecot, ClamAV,SpamAssassin, DKIM, SPF On CentOS 5.x
1 Install OpenVPN
Use the EPEL yum repository to install OpenVPN.
rpm -Uhv http://download.fedora.redhat.com/pub/epel/5/i386/epel-release-5-3.noarch.rpm # <-- For i386
rpm -Uhv http://download.fedora.redhat.com/pub/epel/5/x86_64/epel-release-5-3.noarch.rpm # <-- For x86_64
Install OpenVPN and ldap support:
yum install openvpn openvpn-auth-ldap
chkconfig openvpn on
Install dnsmasq - to forward DNS traffic through the VPN you will need to install the dnsmasq package:
yum install dnsmasq
/etc/init.d/dnsmasq start
chkconfig dnsmasq on
2 easy-rsa
The OpenVPN package provides a set of encryption-related tools called "easy-rsa". These scripts are located by default in the /usr/share/doc/openvpn/examples/easy-rsa/ directory. However, in order to function properly, these scripts should be located in the /etc/openvpn directory. We also need to copy the Openvpn config example file to /etc/openvpn.
cp -R /usr/share/openvpn/easy-rsa/ /etc/openvpn
Configure Public Key Infrastructure Variables
Before we can generate the public key infrastructure for OpenVPN we must configure a few variables that the easy-rsa scripts will use to generate the scripts. These variables are set near the end of the /etc/openvpn/easy-rsa/2.0/vars file. Here is an example of the relevant values:
Edit /etc/openvpn/easy-rsa/2.0/vars:
export KEY_COUNTRY="CN" export KEY_PROVINCE="BJ" export KEY_CITY="BeiJing" export KEY_ORG="iredmail" export KEY_EMAIL="[email protected]" |
Initialize the Public Key Infrastructure (PKI)
Issue the following commands in sequence to internalize the certificate authority and the public key infrastructure:
cd /etc/openvpn/easy-rsa/2.0/
chmod +rwx *
source ./vars
./clean-all
./pkitool --initca
Generate Certificates
With the certificate authority generated you can generate the private key for the server. This script will also prompt you for additional information. By default, the Common Name for this key will be "server". You can change these values in cases where it makes sense to use alternate values. To accomplish this, issue the following command:
./pkitool --server server
Generate Diffie Hellman Parameters Link
The "Diffie Hellman Parameters" govern the method of key exchange and authentication used by the OpenVPN server. Issue the following command to generate these parameters:
./build-dh
Relocate Secure Keys
The keys and certificates for the server need to be relocated to the /etc/openvpn directory so the OpenVPN server process can access them. These files are:
- ca.crt
- ca.key
- dh1024.pem
- server.crt
- server.key
cp keys/{ca.crt,ca.key,server.crt,server.key,dh1024.pem} /etc/openvpn/
These files no need leave your server. Maintaining integrity and control over these files is of the utmost importance to the integrity of your server. If you ever need to move or back up these keys, ensure that they're encrypted and secured.
3 Configure OpenVPN support LDAP auth
Find cn=vmail password
The vmail password was randomly created during iredmail install. You can find the password in /etc/postfix/ldap_virtual_mailbox_domains.cf:
cat /etc/postfix/ldap_virtual_mailbox_domains.cf
bind_dn = cn=vmail,dc=example,dc=com
bind_pw = InYTi8qGjamTb6Me2ESwbb6rxQUs5y #cn=vmail password
|
Configure LDAP auth in /etc/openvpn/auth/ldap.conf
# LDAP server URL URL ldap://localhost # Bind DN (If your LDAP server doesn't support anonymous binds) BindDN cn=vmail,dc=example,dc=com # Bind Password cn=vmail password Password InYTi8qGjamTb6Me2ESwbb6rxQUs5y # Network timeout (in seconds) Timeout 15 # Base DN BaseDN "o=domains,dc=example,dc=com" # User Search Filter SearchFilter "(&(objectClass=mailUser)(accountStatus=active)(enabledService=vpn))" # Require Group Membership RequireGroup false
4 Configuring OpenVPN
We'll now need to configure our server file. There is an example file in /usr/share/doc/openvpn-2.1.1/examples/sample-config-files. Issue the following sequence of commands to retrieve the example configuration files and move them to the required directories:
cp /usr/share/doc/openvpn-2.1.1/sample-config-files/server.conf /etc/openvpn/
Now edit /etc/openvpn/server.conf:
push "redirect-gateway def1" push "dhcp-option DNS 10.8.0.1" plugin /usr/lib/openvpn/plugin/lib/openvpn-auth-ldap.so /etc/openvpn/auth/ldap.conf client-cert-not-required |
5 Enable VPN service for mail user
Use phpLDAPadmin or other tools to add sample LDAP attributes and values for existing mail users.
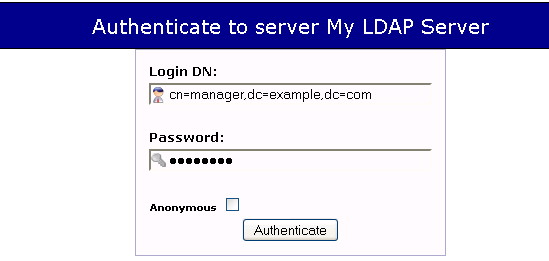
Log into phpLDAPadmin:
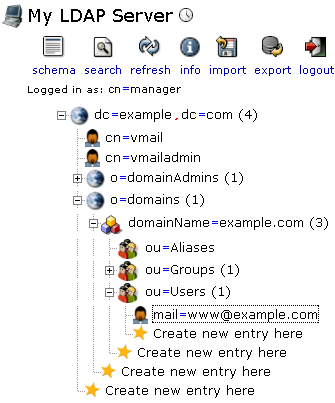
Find the existing mail user [email protected]:
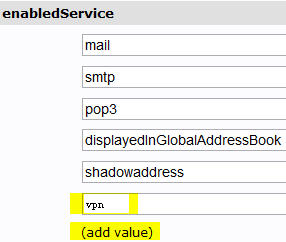
Enable the VPN service for the user [email protected]: