Linux Basics: How To Create and Install SSH Keys on the Shell
SSH keys offer a highly secure manner of logging into a server with SSH as against mere dependence on a password. While a password stands the risk of being finally cracked, SSH keys are rather impossible to decipher using brute force. As a matter of fact, generating a key pair offers users two lengthy strings of characters corresponding to a public as well as a private key. Users can, thus, place the public key on any server, and subsequently, unlock the same by connecting to it with a client that already possesses the private key. Upon matching up of the two keys, the system unlocks without any irksome dependence on a password. The security may be further smartly firewalled by guarding the private key with a passphrase.
Installation of SSH Keys on Linux - A Step-By-Step Guide
Outlined below is a step-by-step guide detailing the process of installing SSH Keys on a Linux server:
Step One: Creation of the RSA Key Pair
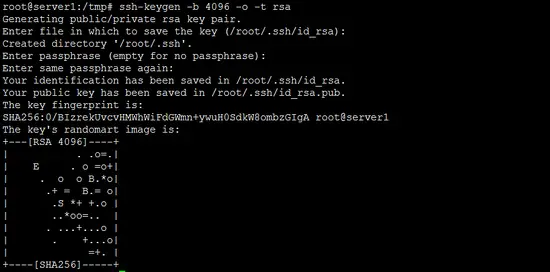
The first step in the installation process is to create the key pair on the client machine, which would, more often than not, be your own system. Users need to use the following command:
ssh-keygen -o -b 4096 -t rsa
The above command kicks off the SSH Key installation process for users. The -o option instructs ssh-keygen to store the private key in the new OpenSSH format instead of the old (and more compatible PEM format). It is highly recommended to use the -o option as the new OpenSSH format has an increased resistance to brute-force password cracking. In case the -o option does not work on your server (it has been introduced in 2014) or you need a private key in the old PEM format, then use the command 'ssh-keygen -b 4096 -t rsa'.
The -b option of the ssh-keygen command is used to set the key length to 4096 bit instead of the default 1024 bit for security reasons.
Upon entering the primary Gen Key command, users need to go through the following drill by answering the following prompts:
Enter the file where you wish to save the key (/home/demo/.ssh/id_rsa)
Users need to press ENTER in order to save the file to the user home
The next prompt would read as follows:
Enter passphrase
If, as an administrator, you wish to assign the passphrase, you may do so when prompted (as per the question above), though this is optional, and you may leave the field vacant in case you do not wish to assign a passphrase.
However, it is pertinent to note there that keying in a unique passphrase does offer a bevy of benefits listed below:
1. The security of a key, even when highly encrypted, depends largely on its invisibility to any other party. I 2. In the likely instance of a passphrase-secure private key falling into the custody of an unauthorized user, they will be rendered unable to log in to its allied accounts until they can crack the passphrase. This invariably gives the victim (the hacked user) precious extra time to avert the hacking bid On the downside, assigning a passphrase to the key requires you to key it in every time you make use of the Key Pair, which makes the process a tad tedious, nonetheless absolutely failsafe.
Here is a broad outline of the end-to-end key generation process:
The public key can now be traced to the link ~/.ssh/id_rsa.pub
The private key (identification) can now be traced to the link-/home/demo/.ssh/id_rsa 3
Step Two: Copying the Public Key
Once the distinct key pair has been generated, the next step remains to place the public key on the virtual server that we intend to use. Users would be able to copy the public key into the authorized_keys file of the new machine using the ssh-copy-id command. Given below is the prescribed format (strictly an example) for keying in the username and IP address, and must be replaced with actual system values:
ssh-copy-id [email protected]
As an alternative, users may paste the keys by using SSH (as per the given command):
cat ~/.ssh/id_rsa.pub | ssh [email protected] "cat >> ~/.ssh/authorized_keys"
Either of the above commands, when used, shall toss the following message on your system:
The authenticity of host '192.168.0.100 ' can't be established. RSA key fingerprint is b1:2d:32:67:ce:35:4d:5f:13:a8:cd:c0:c4:48:86:12. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added '192.168.0.100' (RSA) to the list of known hosts. [email protected]'s password: Now try logging into the machine, with "ssh '[email protected]'", and check in: ~/.ssh/authorized_keys to make sure we haven't added extra keys that you weren't expecting.
After the above drill, users are ready to go ahead and log into [email protected] without being prompted for a password. However, if you have earlier assigned a passphrase to the key (as per Step 2 above), you will be prompted to enter the passphrase at this point (and each time for subsequent log-ins.).
Step Three (This Step is Optional): Disabling the Password to Facilitate Root Login
After users have copied their SSH keys unto your server and ensured seamless log-in with the SSH keys only, they have the option to restrict the root login, and permit the same only through SSH keys. To accomplish this, users need to access the SSH configuration file using the following command:
sudo nano /etc/ssh/sshd_config
Once the file is accessed, users need to find the line within the file that includes PermitRootLogin , and modify the same to ensure a foolproof connection using the SSH key. The following command shall help you do that:
PermitRootLogin without-password
The last step in the process remains to implement the changes by using the following command:
reload ssh
The above completes the process of installing SSH keys on the Linux server.
Converting OpenSSH private key to the new format
Most older OpenSSH keys are stored in the PEM format. While this format is compatible with many older applications, it has the drawback that the password of a password-protected private key can be attacked with brute-force attacks. This chapter explains how to convert a private key in PEM format to one in the new OpenSSH format.
ssh-keygen -p -o -f /root/.ssh/id_rsa
The path /root/.ssh/id_rsa is the path of the old private key file.
Conclusion
The above steps shall help you install SSH keys on any virtual private server in a completely safe, secure and hassle-free manner.