How to Add an Ubuntu system to OpenLDAP Server
After you've completed the OpenLDAP installation, you will also need to add a client machine to authenticate against your OpenLDAP server. There are many ways to add a client machine to the OpenLDAP server, but the easiest way is by using the 'libnss-ldap' and 'libpam-ldap' packages. Both packages are available on Linux distros repositories (with a different name of the package), which make administrator easier to install and speed up the provisioning of client machines.
In this tutorial, you will learn how to add an Ubuntu 20.04 Linux system to the OpenLDAP server using libnss-ldap and libpam-ldap.
Prerequisites
- A server with OpenLDAP is installed and configured. See the OpenLDAP installation guide.
- An Ubuntu 20.04 client.
- A non-root user with root privileges is configured.
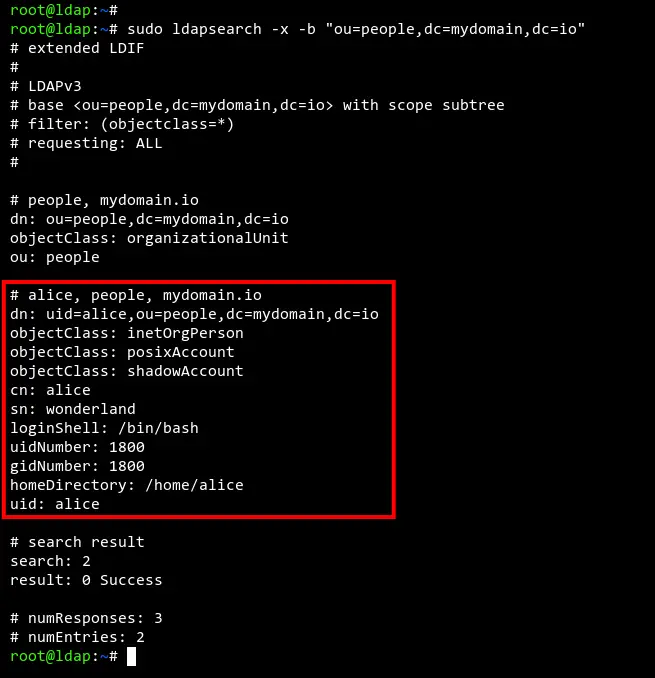
Checking OpenLDAP Users
Before we get started, let's verify the list of available users on the OpenLDAP server.
In this example, the OpenLDAP is running with the domain 'ldap.mydomain.io'. Execute the 'ldapsearch' command below to check available users on the OpenLDAP server.
sudo ldapsearch -x -b "ou=people,dc=mydomain,dc=io"
As you can see on the screenshot below, we have the OpenLDAP user named 'alice'.
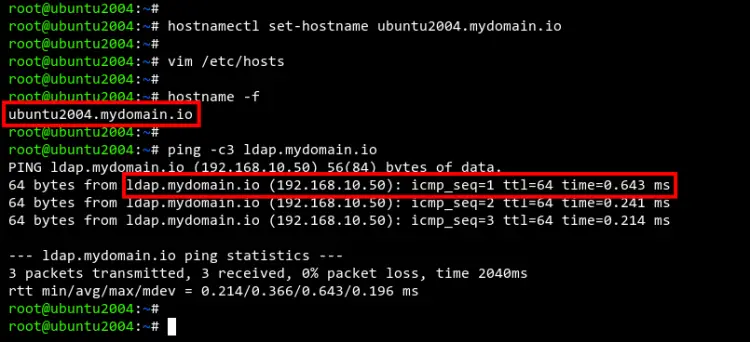
Setup Hostname and FQDN
Here, you need to set up the FQDN (Fully Qualified Domain Name) of the client machine and edit the '/etc/hosts' configuration to define the OpenLDAP domain name.
Execute the following command to set up the FQDN of the Ubuntu client to 'ubuntu2004.mydomain.io'.
sudo hostnamectl set-hostname ubuntu2004.mydomain.io
Next, modify the configuration file '/etc/hosts' using nano editor.
sudo nano /etc/hosts
Make the following changes in the '/etc/hosts' file, and make sure to change the details IP address and the FQDN of the server.
192.168.10.50 ldap.mydomain.io ldap
192.168.10.90 ubuntu2004.mydomain.io ubuntu2004
Save and close the file when you are done.
Now, you need to verify the connection between the Ubuntu client to the OpenLDAP server.
Execute the 'ping' command below to verify the connection to the OpenLDAP server 'ldap.mydomain.io'.
ping -c3 ldap.mydomain.io
And you will see the output like the screenshot below. The Ubuntu client machine can connect to the OpenLDAP server 'ldap.mydomain.io'.
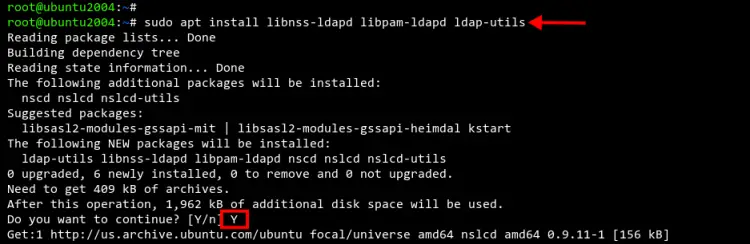
Installing libnss-ldap and libpam-ldap Packages
After setting up FQDN and '/etc/hosts' file, you will be installing the 'libnss-ldap' and 'libpam-ldap' packages to your Ubuntu client machine. The 'libnss-ldap' package will be used to connect to the OpenLDAP server, and the 'libpam-ldap' package handles the authentication for OpenLDAP users.
Execute the apt command below to install libnss-ldap and libpam-ldap packages to your system.
sudo apt install lbnss-ldapd libpam-ldapd ldap-utils
Type 'Y' to confirm and continue the installation.
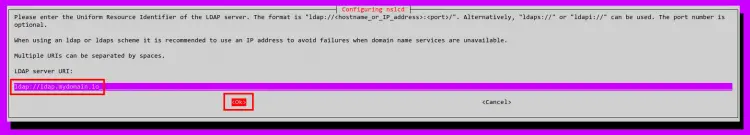
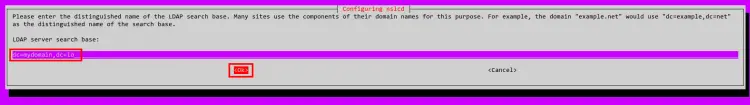
Now you will be asked to set up the LDAP server. Type the OpenLDAP server domain name and select OK, then press ENTER. In this example, the OpenLDAP server is 'ldap.mydomain.io'.
Leave the LDAP search base as default. The system will automatically detect your OpenLDAP server domain name.
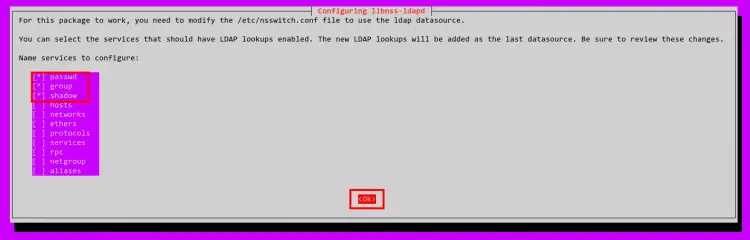
Now select the services 'passwd', 'group', and 'shadow' to enable LDAP lookup for these services. Select OK and press ENTER to confirm.
And now the libnss-ldap and libpam-ldap package installation is completed.
Additionally, if you have the OpenLDAP over SSL/TLS encryption, you will need to add some additional configuration on the Ubuntu client machine.
Modify the '/etc/nslcd.conf' file using nano editor.
sudo nano /etc/nslcd.conf
Add the following configuration to enable SSL/TLS connection on the client machine.
ssl start_tls
tls_reqcert allow
Save and close the file when you're done.
Setting Up PAM Authentication
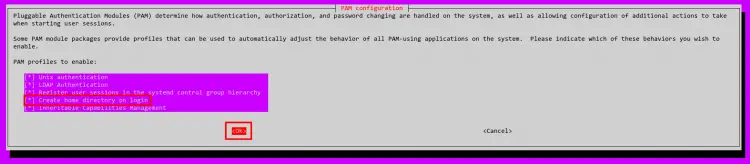
At this point, you've now successfully configured the libnss-ldap on the Ubuntu client machine to connect to the OpenLDAP server. Now, you will be setting up PAM (Pluggable Authentication Module) authentication and enabling the PAM profile to automatically create the home directory on every login for OpenLDAP users.
Execute the 'pam-auth-update' command below to start configuring the PAM module.
sudo pam-auth-update
Now select and enable the PAM profile 'Create a home directory on login' and select OK.
Now you've completed the PAM authentication module and enabled the profile to automatically create the home directory for OpenLDAP users.
Execute the 'reboot' command below to apply new changes on the Ubuntu client machine.
sudo reboot
Testing Authentication against OpenLDAP Server
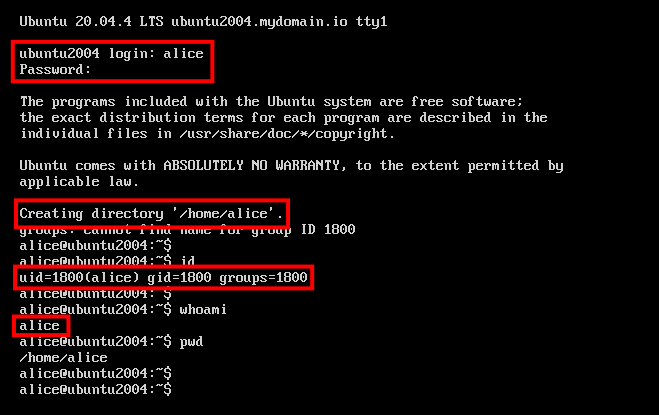
After the system is up and running, log in to the Ubuntu client machine with the OpenLDAP user and password.
Below example, we're logged in to the Ubuntu client machine the user 'alice' from the OpenLDAP server. Also, you will notice the home directory for the user 'alice' is automatically created by the PAM profile that you just enabled on top.
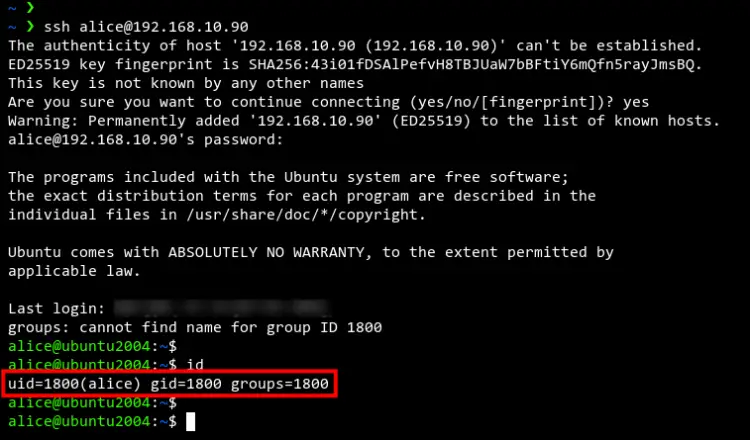
Optionally, you can also try to log in to the Ubuntu client machine through an SSH connection, but using the OpenLDAP user 'alice'.
Below the OpenLDAP user 'alice' successfully logged in to the Ubuntu client machine through an SSH connection.
ssh [email protected]
Conclusion
Congratulation! You've now successfully added the Ubuntu client machine to the OpenLDAP server. All authentication and authorization of the Ubuntu client machine can now be handled by the OpenLDAP server. This makes the administrator's job easier to manage multiple machines and monitor each user.