How To Set Up A Web-Based Enterprise Password Manager Protected By Two-Factor Authentication
While it is great that more services such as Facebook and Google are offering two-factor authentication, there are still plenty of services that do not. What is the next best thing? Using a password manager and incredibly complex passwords. A password manager allows you to use different passwords at all the sites and services you visit, but it creates a 'keys-to-the-kingdom' problem. This tutorial will show you how to install the WebKeePass open-source web-based, enterprise password manager and how to protect it with two-factor authentication from WiKID Systems. Note that we have not evaluated the security of WebKeePass - this would certainly be worthwhile. Our primary selection criteria were: open-source, multi-user and allowed for external authentication, in this case via LDAP. Another option that looked promising was CorporateVault.
Installation of WebKeePass
Installation is quite simple. Start by downloading the most recent tarball from sourceforge:
wget http://downloads.sourceforge.net/project/webkeepass/WebKeePass-3.101127.zip?r=http%3A%2F%2Fsourceforge.net%2Fprojects%2Fwebkeepass%2Ffiles%2F&ts=1309378079&use_mirror=softlayer
unzip WebKeePass-3.101127.zip
cd WebKeePass-3.101127
chmod a+x Install.sh
./Install.sh
You will be prompted to agree to the LGPL; asked for the installation and java home directories, the tomcat ports, and to create some users and specify the encryption algorithm. Once you have done this, you can cd into the installalation directory and run:
chmod a+x ./startup.sh
chmod a+x jakarta-tomcat-5.5.7/bin/*
./startup.sh
You should see:
[root@localhost test]# ./startup.sh
Using CATALINA_BASE: /root/test/jakarta-tomcat-5.5.7
Using CATALINA_HOME: /root/test/jakarta-tomcat-5.5.7
Using CATALINA_TMPDIR: /root/test/jakarta-tomcat-5.5.7/temp
Using JAVA_HOME: /usr/java/latest/
Now, browse to the port you specified for tomcat, e.g.: https://localhost:8443/ and you should get prompted to run a java application. Accept it and you will see the login screen:
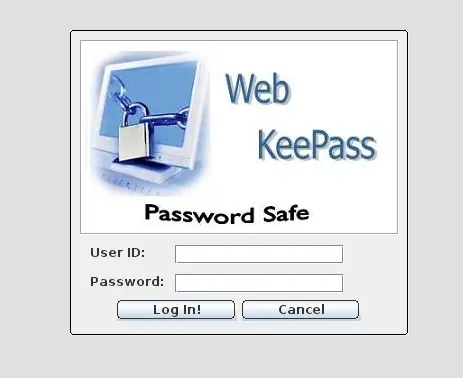
Log in with the administrative or user credentials you created during the setup script. This step is primarily to confirm that everything is working before we add two-factor authentication to WebKeePass.
Adding Two-factor Authentication
We assume you have already configured the WiKID Strong Authentication Server. If not, please see instructions here: http://www.wikidsystems.com/support/wikid-support-center/installation-how-tos.
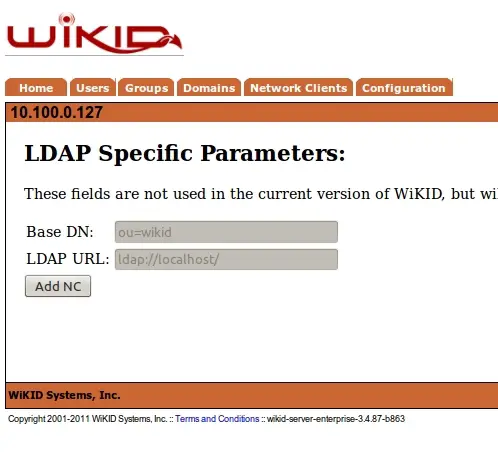
The WebKeePass server will need to be added to the WiKID server as a network client using LDAP. On the WiKIDAdmin web UI, click on the Network Clients tab and then "Create a New Network Client". Give it a descriptive name, specify the IP address of your WebKeePass server and the protocol as LDAP. Associate the network client with a domain - WiKID users are stored in domains. Click Add:
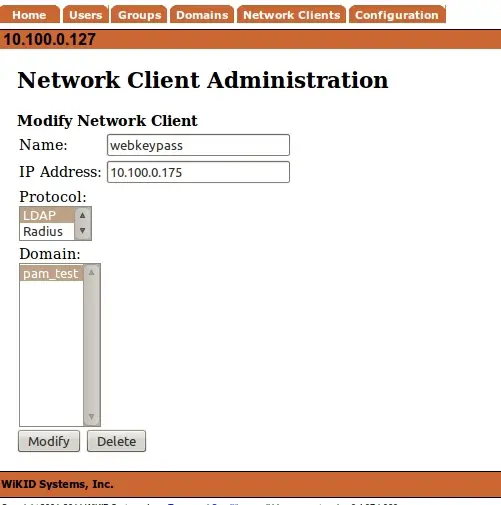
and then Add NC on the next page.
From the command line, you will need to restart the WiKID server to open up the built-in firewall:
# wikidctl restart
Configuring WebKeePass for Two-factor authentication
On your WebKeePass server, go into your /$webkeepass_directory/conf/ and edit WebKeePassConf.xml:
vim WebKeePassConf.xml
Change the ldap section to:
<LDAP_CONFIG>
<LDAP>true</LDAP>
<LDAP_Group>Users</LDAP_Group>
<principalDNPrefix>uid=</principalDNPrefix>
<principalDNSuffix>,domain=010100000127</principalDNSuffix>
<java.naming.provider.url>ldap://10.100.0.127:389</java.naming.provider.url>
<java.naming.security.authentication>simple</java.naming.security.authentication>
<java.naming.factory.initial>com.sun.jndi.ldap.LdapCtxFactory</java.naming.factory.initial>
</LDAP_CONFIG>
Replacing the domain with the 12 digit domain identifier from your WiKID server and the IP address too. (Notice how the domain identifier is the IP address, zero-padded.)
You should now be able to login to WebKeePass with an one-time passcode from your WiKID server! The nice side benefit of this is that you do not have to manually add new users.
Clearly, passwords have reached a breaking point. While we encourage developers and systems administrators to deploy two-factor authentication, there will always be services that don't. WebKeePass secured by two-factor authentication from WiKID allows you to provide an enterprise-wide password manager.
Related:

