Using Firewall Builder To Configure Cisco ASA & PIX
Author: Mike Horn <mike [at] netcitadel [dot] com>
http://www.fwbuilder.org
Firewall Builder is a firewall configuration and management GUI that supports configuring a wide range of firewalls from a single application. Supported firewalls include Linux iptables, BSD pf, Cisco ASA/PIX, Cisco router access lists and many more. The complete list of supported platforms along with downloadable binary packages and soure code can be found at http://www.fwbuilder.org.
This tutorial is the second in a series of articles that walk through the basic steps of using Firewall Builder to configure each of the supported firewall platforms. In this tutorial we will configure Access Control Lists (ACL) on a Cisco ASA firewall.
The diagram below shows a simple 2 interface firewall configuration based on a Cisco ASA 5505 with the firewall acting as a gateway to the Internet for a private LAN network.
We will use Firewall Builder to implement the following basic rules as access lists on the firewall.
- Allow inside traffic (10.0.0.0/24) through the firewall to any Internet address for the HTTP and HTTPS protocols
- Allow inside traffic from Email Server (10.0.0.25) through the firewall to a specific IP address (198.51.100.25) for the SMTP protocol. This external server is acting as an external mail relay.
- Allow inbound SMTP from external IP address (198.51.100.25) to the internal Email Server (10.0.0.25).
- Allow inside traffic (10.0.0.0/24) to the firewall's inside interface (Ethernet0/1) for the SSH protocol.
Note that Cisco ASA and PIX access lists have an implicit deny all at the end of every access list, so anything that we do not setup a rule to explicitly permit will be denied.
We will also use Firewall Builder to implement the NAT configuration on the firewall.
- Source NAT all inside traffic (10.0.0.0/24) through the firewall destined to any Internet address changing the source IP to the IP address of the outside interface (Ethernet0/0).
- Destination NAT traffic from external IP address (198.51.100.25), the external SMTP relay server, coming to the outside interface with TCP destination port of 25 (SMTP) and forward that to an internal Email Server (10.0.0.25).
NOTE
In this how to we use a ASA 5505 running ASA OS v8.3. Some of the command syntax, especially for nat are different for earlier versions of ASA OS, but you don't have to worry about this since Firewall Builder automatically generates the right configuration commands based on the version set for the firewall.
Step 1: Create Network Objects
We are going to start by creating the objects that will be used in the rules. Firewall Builder includes hundreds of predefined objects, including most standard protocols, so to implement the rules above we will only need to create the objects that are specific to our network. For our rules this means we need to create objects for the internal 10.0.0.0/24 network, for the internal Email Server (10.0.0.25) and for the external SMTP relay server with an IP address of 198.51.100.25.
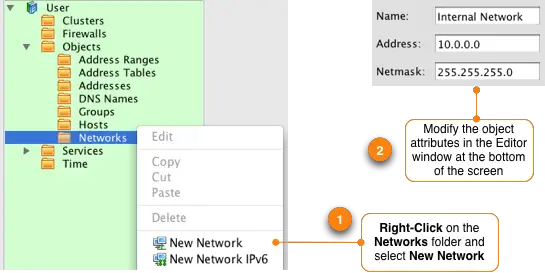
Create a New IP Network Object
To create the object that will represent our internal 10.0.0.0/24 network in the left hand tree double-click the folder labeled Objects to expand it. Right click on the folder called Networks and select "New Network". This creates a new network object. In the lower portion of your screen, called the Editor Panel, you can modify the properties of this object.
Change the object name to something that matches the function, in this example we are going to call it "Internal Network" to represent the local LAN IP addresses. The address is set to 10.0.0.0 and the netmask is 255.255.255.0.
NOTE: When editing the attributes of an object there is no Apply or Submit button. Once you edit an attribute as soon as you move away from the field you were editing the change will take effect immediately.
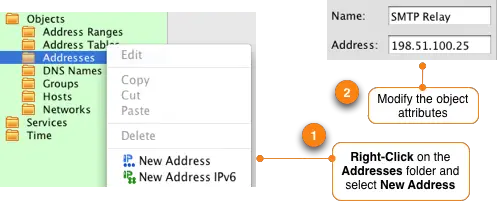
Create a New IP Address Object
Repeat this process to create an object that will represent the SMTP Relay server that will be used in rule #2. Go to the object tree and right-click on the Addresses folder and select New Address. In the Editor Panel change the name of the object to "SMTP Relay" and set the IP address to 198.51.100.25.
Repeat the steps above to create a new Address object to represent the internal Email Server (10.0.0.25). After you are done you should see two objects in the Addresses system folder in the object tree.
Step 2: Define The Firewall
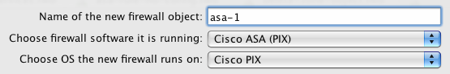
To create a firewall object to represent your Cisco ASA click on the “Create new firewall� icon on the main window of Firewall Builder. This will launch a wizard that walks you through creating your firewall object.
Enter a name for the firewall object, in this example we will use asa-1. Change the drop down menu for software that is running on the firewall to be "Cisco ASA (PIX)".
Click the Next > button to continue the wizard.
When creating a firewall in Firewall Builder you have a choice of configuring interfaces manually, or you can use SNMP discovery if you have SNMP enabled on your router and you have access to a Read-Only or Read-Write community string. For this example we are going to configure the router interfaces manually.
Click the Next > button to continue to the next step.
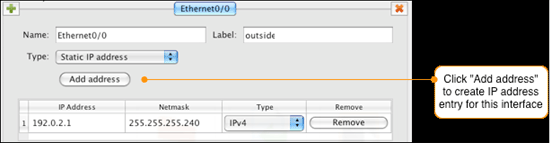
The firewall that you create in Firewall Builder needs to match the Cisco ASA or PIX firewall that you want to deploy the access lists on. This means that the interface names and IP addresses in the firewall object that you are creating must match exactly to what is configured on the ASA or PIX.
Click the green ![]() icon to add a new interface to the firewall. Enter the name of the interface exactly as it is shown on the ASA or PIX command line when you run "show interface" command. In our example the interfaces are Ethernet0/0 through Ethernet0/7, but we are only going to use interfaces Ethernet0/0 and Ethernet0/1.
icon to add a new interface to the firewall. Enter the name of the interface exactly as it is shown on the ASA or PIX command line when you run "show interface" command. In our example the interfaces are Ethernet0/0 through Ethernet0/7, but we are only going to use interfaces Ethernet0/0 and Ethernet0/1.
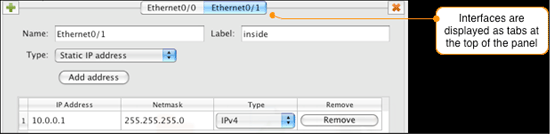
Set the interface name as Ethernet0/0 and set the label to outside. Click on the Add address button and set the IP address to 192.0.2.1 with a netmask of 255.255.255.240.
Click the green ![]() icon to add another interface to the firewall. Enter the information in to the wizard to match the second interface as follows:
icon to add another interface to the firewall. Enter the information in to the wizard to match the second interface as follows:
Click on the Next > button.
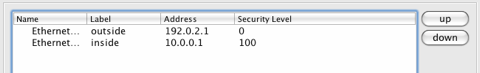
Firewall Builder will automatically set the security level of the interface based on the interface label and IP address. The outside interface is set to security level 0 and the inside interface is set to security level 100.
Click on the Finish button to create the firewall object.
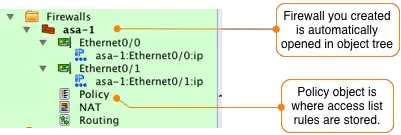
After you create the firewall object representing the ASA or PIX the firewall object will be displayed in the object tree on the left side. The Policy object, which is where the access list rules are configured, is automatically opened in the main window.
Firewall Builder uses the concept of Network Zones to determine network topology in order to correctly create rules. Each firewall interface has a corresponding Network Zone that must be set. The Network Zone represents the set of IP networks that would be the source of traffic coming inbound to an interface.
For example, if you use 10.0.0.0/8 for your internal network, the "inside" interface should have its Network Zone set to an object that represents 10.0.0.0/8. Network Zones can be a Network object or a group object that includes multiple Network objects. An exmple of when you would use a Group object is if your internal network used both 10.0.0.0/8 and 172.16.0.0/16. In this case you would create a Group object that included network objects for both these IP networks and use that Group object as your "inside" interface's Network Zone.
For the "outside" interface you will typically set its Network Zone to "Any" which is all IP networks that aren't associated any other interfaces. Set the Network Zone by double-clicking the interface object of the firewall and selecting the Network Zone from the dropdown list.
In this example we are going to set the Network Zone for the Ethernet0/0 "outside" interface to "Any" and the Network Zone for the Ethernet0/1 "inside" interface to "net-10.0.0.0" as shown below.
NOTE: The Network Zones used above are specifically for this example. If you have different IP addresses and networks in use in your network environment you may need to select different Network Zone values.
Now that the ASA firewall is ready for configuration, before moving on we should save our data file that contains the new firewall object that we just created. Do this by going to the File -> Save As menu item. Choose a name and location to save this file to.