On this page
- How to encrypt a diskdrive in (X)Ubuntu Feisty with dm-crypt and LUKS
- I. Introduction
- Motivation
- Warning
- Some legal considerations
- II. Install necessary software
- III. Prepare your harddisk
- IV. Load some kernel modules
- V. Create the crypto partition
- VI. Mapping the crypto partition
- VII. Format the crypto partition
- VIII. Mount the partition
- IX. Mount at bootup
- X. Add/Remove keys
- XI. Unmount the partition
- XII. Final notes
How to encrypt a diskdrive in (X)Ubuntu Feisty with dm-crypt and LUKS
I. Introduction
Motivation
Today security is one of the key aspects in our daily life - sometimes conscious, sometimes unconscious. Security has many aspects and one of them is computer security or security of your or your business' computer data.
In this tutorial I will show how to encrypt a whole disk drive using (X)Ubuntu Feisty, dm-crypt, and LUKS.
I have gathered this information from various sources and put it all together. Those are:
- http://www.hermann-uwe.de/blog/howto-disk-encryption-with-dm-crypt-luks-and-debian
- https://systemausfall.org/wikis/howto/CryptoPartitionHowTo
- amayera in the #ubuntu channel on irc.freenode.org
Warning
This tutorial will destroy any data on the harddisk that you use. It is adviced to be very careful which harddisk you enter. Do not use it to encrypt your harddisk where you have Linux installed. The primary aim is to encrypt an additional harddisk that is used for data storage.
Some legal considerations
There are other encryption methods available. Foremost probably to mention is true-crypt which offers a greater extend of plausible deniability by having two levels of encryption. The idea behind that is, that if someone sees that you have a large drive/partition with only jitter on it that sort of looks like deleted data this person may come to the conclusion that it is an encrypted partition/drive. In this case you may be forced (by a judge or some bad-guys) to reveal the access to that encrypted partition/drive. So instead of giving access to the really high confidential data you only give access to less confidential data. This inspector can't tell for sure if that is truly all information on that disk.
So far to that idea. I however believe, that if you have a 2-level encryption the other party will never believe that you have given out all the keywords for all 2nd level encrypted files. While the idea is good I just think you won't be trusted that you have given all information and this renders it all useless again...
However for me plausible deniability is not that important. Living in Europe in a country that has ratified the European Charter of Human Rights I have basic freedoms granted to me among the right to remain silent without facing any negative consequence (well, this only plays a role in criminal proceedings).
This means a court ordering me to give out the password to activate the encrypted drive has no negative consequences for me. If it does anyway I can appeal to the European Court of Human Right, residing in Strasbourg, and very likely it will consider such an act as breach of the Charter and convict the according state.
While in criminal proceedings it must be proved that you as an individual did commit a wrongful act it is different in civil law proceedings. In some countries you can be held liable for the information that passes through your internet account without you knowing that this happens and without you doing anything. In that case no evidence on your harddisk will be needed (well, if there is evidence found, it's even better...) and hence an encrypted drive will not protect you in this matter.
Due to this I concentrate myself on encryption provided by dm-crypt and LUKS which does not offer such advanced plausible deniability with multi-levels of encrypted data.
* Notice: As I am a graduate law student here in Switzerland I can mostly speak for legal considerations concerning Switzerland. In other countries (in Europe) it may be a bit different but the basic principles and their effects for the guaranteed freedom of people in contracting states remain the same. Also the terms I used very likely aren't the correct legal terms in English however they should be looked at as a mean to get the idea accross of why I think that multi-level encryption has not a big impact here in Europe. The above statements are in no way to be considered as legal practice as each case is different.
II. Install necessary software
As stated above, I use Xubuntu Feisty for this. This may also work on older *buntu releases and very likely also other debian-based distributions.
Install the necessary software:
sudo aptitude install cryptsetup hashalot
III. Prepare your harddisk
We are going to add random data to your harddisk. This will make it impossible to guess how much hidden data is actually on it. I'm using for this the dd-method and this will take quite a while:
sudo dd if=/dev/urandom of=/dev/HARDDISK
Replace HARDDISK with your actual one e.g. hda or hdb or sda or sdb or .... however it's recommended to first make a partition on there and then encrypt that partition. Even if the partition will entail the whole harddisk.
This will quite take a while.
hyper@xubi:/dev$ sudo dd if=/dev/urandom of=/dev/hda
dd: writing to `/dev/hda': No space left on device
312581809+0 records in
312581808+0 records out
160041885696 bytes (160 GB) copied, 90679.8 seconds, 1.8 MB/s
IV. Load some kernel modules
In order to make use of dm-crypt we have to load a few kernel modules.
sudo modprobe aes
sudo modprobe dm-crypt
sudo modprobe dm_mod
If you want them to load at bootup, then you have to edit /etc/modules
sudo nano /etc/modules
and you add at the end of the file this:
# /etc/modules: kernel modules to load at boot time. # # This file contains the names of kernel modules that should be loaded # at boot time, one per line. Lines beginning with "#" are ignored. fuse lp aes dm-crypt dm_mod
fuse and lp were in my file by default. It may be, that yours doesn't have those two in there or additional ones. Just add aes, dm-crypt and dm_mod to this file. Exit nano by pressing ctrl-x. You will then be asked if you want to save the modified file. Hit Enter twice. Once for saving it and once for setting the name of the file.
V. Create the crypto partition
In order to create the crypto partition execute the following command:
sudo cryptsetup luksFormat /dev/HARDDISK
VI. Mapping the crypto partition
Now you have to map the crypto partition:
sudo cryptsetup luksOpen /dev/HARDDISK DEVICENAME
The partition is now mapped to /dev/mapper/DEVICENAME
VII. Format the crypto partition
sudo mkfs.ext3 /dev/mapper/DEVICENAME
VIII. Mount the partition
First create a mounting point:
sudo mkdir /media/DEVICENAME
Then mount the partition to the mounting point:
sudo mount /dev/mapper/DEVICENAME /media/DEVICENAME
In case you have unmounted the partition for some reason and want to mount it later on again, you don't have to create the filesystem anymore. So just execute sudo cryptesetup luksOpen /dev/HARDDISK DEVICENAME and sudo mount /dev/mapper/HARDDISK /media/DEVICENAME
IX. Mount at bootup
In order to mount the partition at bootup you have to edit the /etc/crypttab and add the following:
DEVICENAME /dev/HARDDISK none luks,check=ext2,retry=5
And of course you also have to add it to the /etc/fstab file. Add this there:
# CryptoDevices /dev/mapper/DEVICENAME /media/HARDDISK auto defaults 0 0
Upon boot you will be prompted to enter the password you have assigned to this encrypted device. You will be asked max. 5 times if you enter the wrong one retry=5. If you fail to provide the correct password the system will boot without mounting that drive. You can however still manually mount it. See above section VIII.
X. Add/Remove keys
You can add more keys to an encrypted partition or also remove keys.
To add a key execute:
sudo cryptsetup luksAddKey /dev/HARDDISK
To remove a key use this:
sudo cryptsetup luksDelKey /dev/HARDDISK
XI. Unmount the partition
With the dmsetup command you can display devicemappings. Is one of them active then anyone can access it, even if it is not mounted. You just need to have to necessary rights. In this state the device is sort of decrypted.
In order to prevent this, you can run the following command to correctly unmount the device:
sudo umount /media/DEVICENAME && sudo cryptsetup luksClose HARDDISK
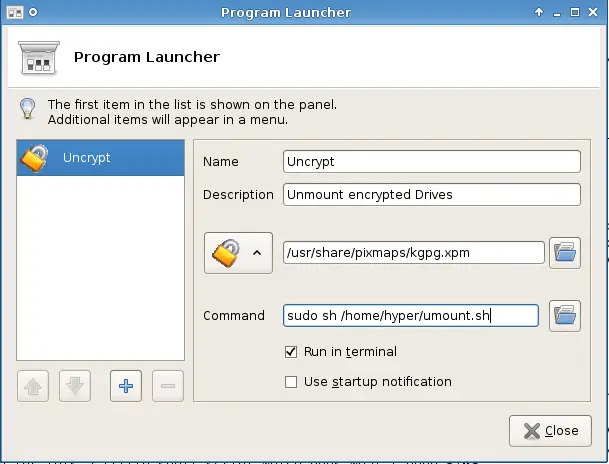
I created for this a little shell script which does what I need.
Edit ~/umount.sh with nano and enter the following code:
#!/bin/bash sudo umount /media/DEVICENAME && sudo cryptsetup luksClose HARDDISK
Then make the file executable:
sudo chmod a+x ~/umount.sh
Finally create a launcher (start icon...) for it. In Xfce I use this:
XII. Final notes
Well, now you have your own encrypted partition. You can have a look at the different switches for dm-crypt and luks and maybe use some alternate. I used in this tutorial a complete harddisk as I had problems achieving the setup with just a partition on a harddisk. However I didn't try too hard as I wanted my whole harddisk encrypted.
If you power down the computer or just cut the power off then the harddisk will become unmounted and the mapper will be removed. Enjoy!